The military’s IT and communications arm will partner with contractor Booz Allen Hamilton later this year on a $6.8 million project to prototype a new security model based on zero trust principles.
The Defense Information Systems Agency said the project, which will last six months, is designed to bring it into alignment with a cybersecurity executive order issued by President Joe Biden last year. It will also put a greater emphasis on protecting data and incorporate technologies and concepts — like secure access service edge (SASE) and software-defined wide-area networks (SD-WAN) — that were recommended in a zero trust plan developed by DISA in 2020.
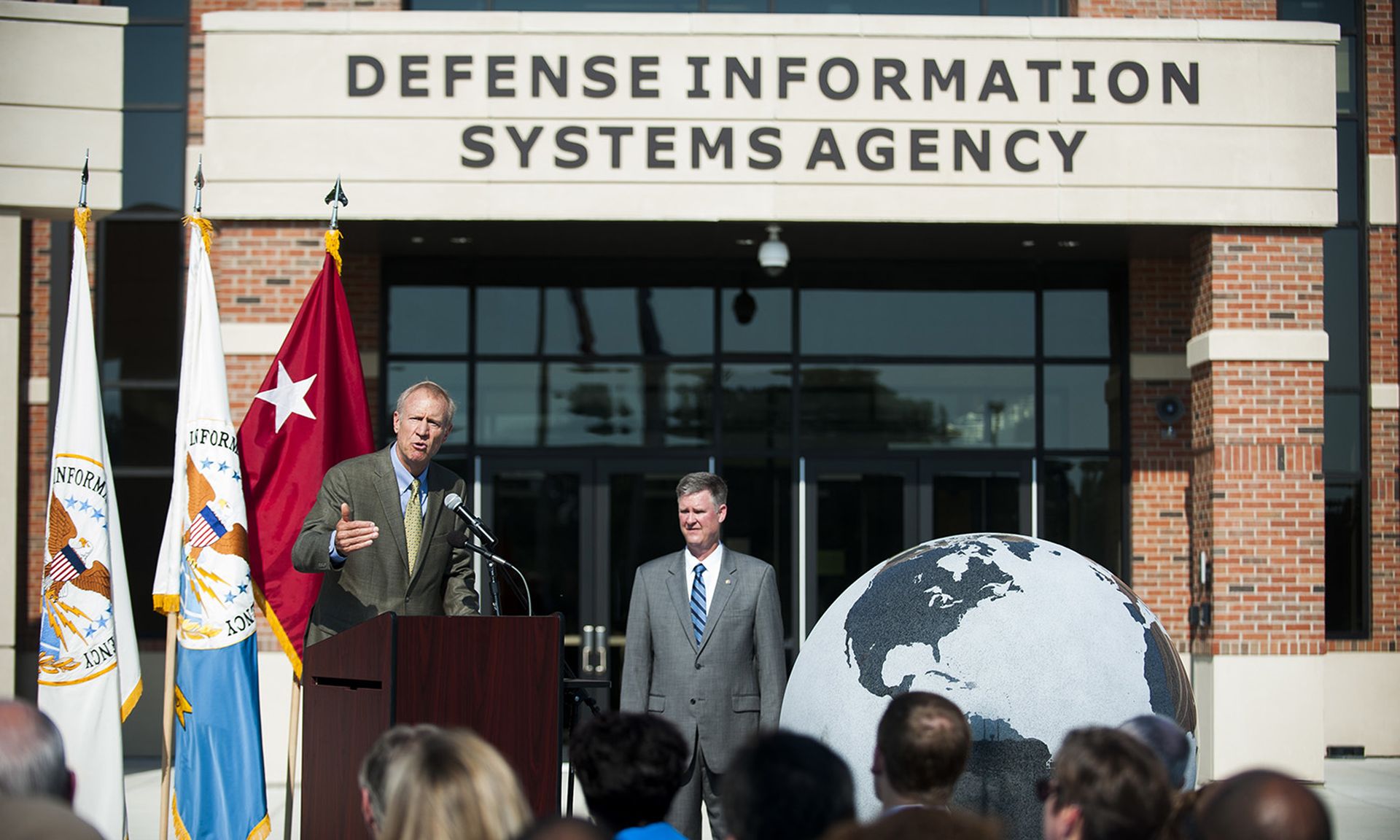
“Over the course of the next six months, we plan to produce a working prototype that is scalable across the department. During that time, we will do what DISA does best — build, test, validate and implement the premier cybersecurity solutions for the Department of Defense and warfighter around the world,” said Jason Martin, director of DISA’s digital capabilities and security center, in a statement.
The model will eventually replace the Joint Regional Security Stack, a suite of technologies and services that DoD information systems have relied on for network security, firewalls, intrusion detection and prevention, virtual routing and other capabilities. DISA is “actively developing a department-wide strategy where mission partners will transition from current cybersecurity solutions, like the JRSS, to Thunderdome or other zero trust implementations,” the agency said in a release.
Defense officials have been preparing for a lengthy transition and, as FCW reported earlier this month, DISA officials have clarified that despite the Thunderdome pilot, the JRSS will “be here for some time” and “won’t be going away right away.”
“JRSS isn't going away right away, it'll be here for some time. And what will happen is Thunderdome will cut into it over time. And eventually JRSS will transition to, you know, something else, which is the future of Thunderdome," said Maj. Gen. Garret Yee, who also serves as assistant to DISA Director Lt. Gen. Robert Skinner. "Firewalls aren't going away; they're just going to different places in the system of systems that we have to defend.
Among other goals put forth by program officials are simplifying their suite of endpoint security solutions and allowing users to connect directly to DoD applications over the internet regardless of its hosting environment.
Like many parts of the federal government, the Pentagon is looking to move away from the kind of classic, perimeter-based network cybersecurity defenses that are ill-suited to defending against modern threats in the cloud, through the supply chain and from disgruntled or compromised insiders who have established credentials and access.
One of the heftier cybersecurity mandates passed down by the Biden administration over the past year is a requirement for civilian federal agencies to identify all of their connected endpoint devices and implement new endpoint detection and response technologies over top, part of a broader plan to improve the government's ability to spot emerging threats, conduct incident response and perform forensic analysis of cyber attacks that hit federal systems. The cybersecurity executive order put the National Security Agency and the secretary of defense in charge of determining "appropriate actions for improving detection of cyber incidents affecting National Security Systems...including recommendations concerning EDR approaches and whether such measures should be operated by agencies or through a centralized service."
As SC Media has reported, civilian agencies are facing a similar need to simplify their endpoint security protocols. Large organizations like the federal government typically deploy a wide variety of devices and operating systems, many of which run on different versions or operate in different environments. Most EDR products, on the other hand, are highly customized and require significant tuning and management.