Archived: Legitimizing Zero Trust: A buzzword no longer?
Earn up to 6.5 CPE credits by attending this virtual event.
Depending on whom you ask, zero trust appears to be passing the credibility test. Despite continued misconceptions around zero trust architectures, the principles of “least privilege” and “never trust, always verify” have caught on as a bona fide approach to minimizing the risk of a data breach.
But to truly legitimate zero trust as a viable strategy and not just a buzzword, security practitioners must put in a genuine effort to apply its chief principles properly and comprehensively. This eSummit will reveal precisely how to do just that. Lessons include:
- The latest exclusive research on zero trust from the CyberRisk Alliance
- Defining zero trust, including the solutions and practices truly required for a legitimate ZTA implementation
- Which technologies and policies should be highest priority when building a ZTA
- Incorporating zero trust into your cloud migration strategy
- Developing a career specialization in zero trust through training or certification
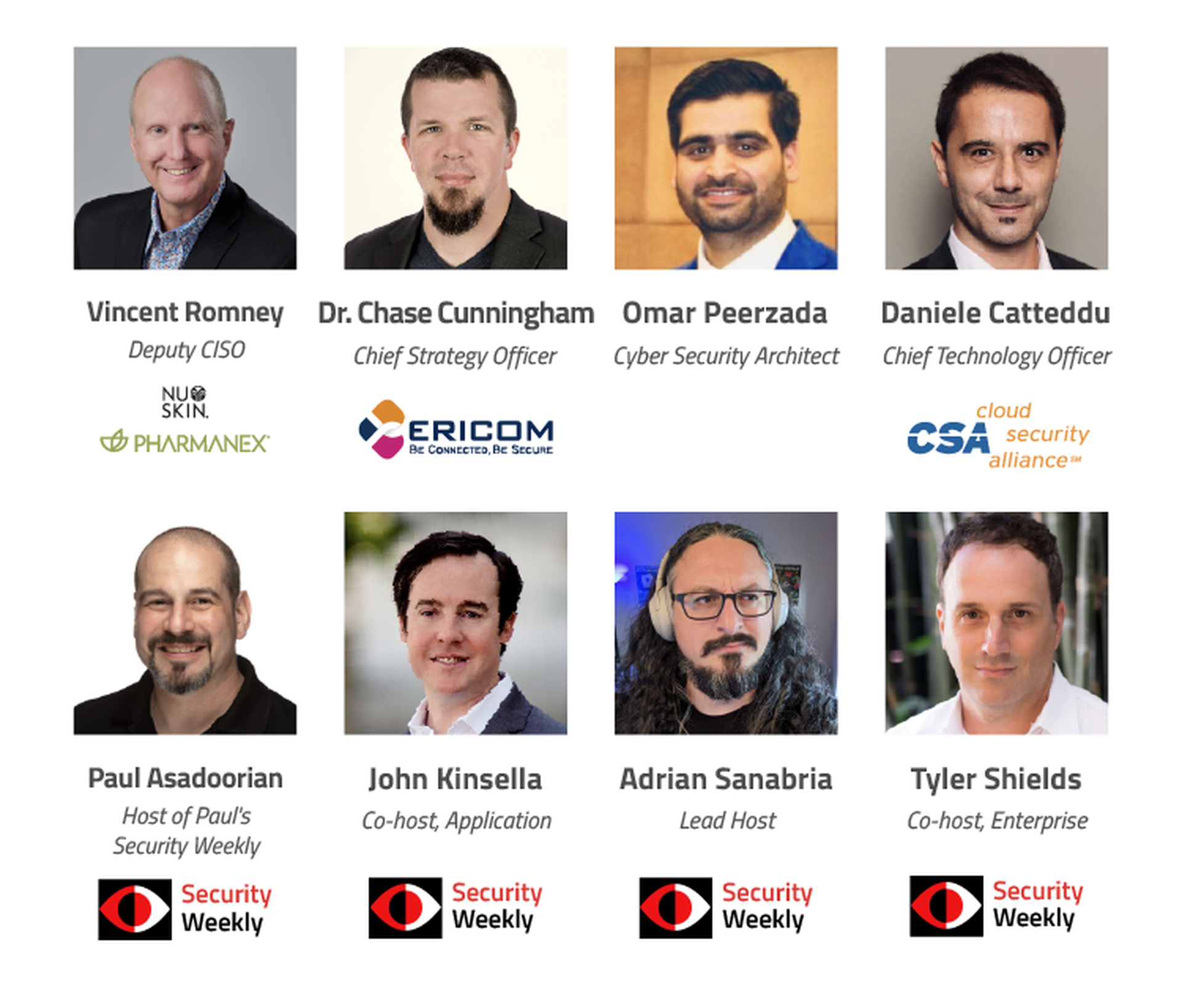
Featured Speakers:
Day 1
11:00 AM
KEYNOTE | Vincent Romney: Deputy CISO, Nuskin & Pharmanex
Pass or fail? Putting vendors through the zero-trust sniff test
A lot of vendors claim to be zero trust solutions, but are they? A key stage in the evolution of zero trust from unproven buzzword to legitimate strategy is separating the wheat from the chaff in terms of identifying which vendors truly do enhance your zero-trust strategy, and which are just jumping on the bandwagon. This session will focus on NIST 800-207 guidelines and how they can be used to determine whether or not a vendor's claim of being an integral part of zero trust architecture can be justified.
11:30 AM
Zero trust with zero fluff
J. Wolfgang Goerlich; Advisory CISO, Cisco Secure
Join Cisco Advisory CISO Wolfgang Goerlich for a practical discussion on the promises and the realities of zero trust architecture for the enterprise. Past the buzzwords and lofty promises, can zero-trust strategies help build better defenses where the rubber hits the road? In this talk, you’ll learn which types of organizations are most likely to have adopted zero-trust initiatives, how they are handling their legacy systems and assets, and what accelerates adoption across the business.
12:00 PM
Approaching security with an identity-first mindset
Alexandria Hodgson; Senior Solutions Product Marketing Manager
It's no longer news that we need to support and secure increasingly distributed organizations. As companies look for long-term solutions for their hybrid and fully remote workforces, one thing is clear - identity is at the centre of businesses today. An identity-first approach to security reduces today's cybersecurity risks and provides the foundation for a Zero Trust security strategy. A modern identity solution can also help you tie the complexities of protecting people and assets together in a seamless way.
Join this session to learn:
- How to enable and secure your workforce
- How identity can lay the foundation for any Zero Trust security initiative
- How identity fits into a larger ecosystem and supports a more robust security posture
12:30 PM
Break
12:45 PM
Research roundup: Analyzing the latest zero-trust trends and sentiments
Even as the outlook around zero trust -- and where it fits within the overall cybersecurity landscape -- becomes clearer, there are still many questions left to be resolved. More information, more investigation is needed. Fortunately, cyber researchers at hard at work identifying the latest trends and evolutions in the zero-trust space, while also surveying the latest user sentiments around this never trust, always verify strategy. This session will look at some of the more salient zero-trust research findings from the last year.
1:30 PM
Accelerating transformation with zero trust
Sanjit Ganguli; VP, Transformation Strategy and Field CTO
Zero trust is a framework for securing organizations in the cloud and mobile world that asserts that no user or application should be trusted by default. Following a key zero trust principle, least-privileged access, trust is established based on context (e.g., user identity and location, the security posture of the endpoint, the app or service being requested) with policy checks at each step. Zero trust has the power to transform how you connect and secure your enterprise in a hyper-distributed world. This session will separate fact from fiction to implement true zero trust without the pitfalls of false approaches.
2:00 PM
KEYNOTE | Daniele Catteddu: CTO, Cloud Security Alliance
Zero trust training & certification as a career differentiator
Can developing a specialization in ZTA help infosec workers stand out from their peers? This session will look at to what extent professional development opportunities such as zero-trust training and certification programs can serve as a career-booster for cyber pros looking to advance and qualify for strategic leadership roles.
DAY 2
11:00 AM
Podcaster roundtable: Defining what zero trust is… and isn't
Paul Asadoorian; Founder & CTO, Security Weekly Productions & Host of Paul's Security Weekly
John Kinsella; Co-host, Application Security Weekly
Tyler Shields; Co-host, Enterprise Security Weekly
How is the definition of zero trust changing? What is it, and what isn't it? And is zero trust at this point an inclusive concept that can be universally adopted by companies of all kinds (including smaller businesses), or is it only achievable for certain organizations and certain use cases? Hear from a panel of Security Weekly's leading podcaster personalities who will weigh in with their own perspectives. One thing's for sure: This session won't be lacking in strong opinions.
11:45 AM
The new paradigm for work-from-anywhere: Zero trust network access
Steve Fallin; Director Product Management – Secure Access, Absolute Software
Dr. Torsten George; Cybersecurity Evangelist, Absolute Software
In today’s perimeter-less environment, security practitioners can no longer assume implicit trust among applications, users, devices, services, and networks. That’s why many organizations have started to embrace a Zero Trust approach and are considering augmenting their conventional network access security concepts such as virtual private networks (VPNs) and demilitarized zones (DMZs) with Zero Trust Network Access (ZTNA) solutions. Join two renowned industry experts in this webinar to talk about the drivers for ZTNA, best practices for implementation, and what characteristics to look for when evaluating solutions to fulfill both business and end user requirements.
12:15 PM
Break
12:30PM
Trust no-one, not even the machines
Kenny DuMez; Developer Relations Engineer, Teleport
Often when people talk about Zero-Trust models, it’s framed in verifying all the access attempts made by people: engineers, contractors, various employees and the devices used to access infrastructure resources. In this talk we’ll focus on how to employ that same identity-first zero-trust model for your VMs, server and machines. We’ll go over how you can use open-source tooling like Teleport Machine ID to assign an identity, implement rich audit logging and access monitoring while enforcing compliance and accountability for every microservice, machine, and bot in your organization.
1:00 PM
KEYNOTE | Dr. Chase Cunningham: Chief Strategy Officer, Ericom Software
Building your ZTA: What technologies & polices should be highest priority?
If you were building a hierarchy of solutions and policies that you need to have a complete zero-trust architecture, what would be at the top of your list? What are your foundational technologies, what enhancements can wait until later, and what additions are of less importance? In this session, hear from Dr. Zero Trust for his take on how best to prioritize the components of your ZTA strategy.




