By Stu Sjouwerman, CEO, KnowBe4
As we have noted in a number of previous posts, the bad guys tend to do the majority of their innovation, for lack of a better term, around the payloads delivered by phishing attacks as opposed to the social engineering schemes used to bamboozle unwitting email recipients into triggering those payloads.
Ransomware is the best example of this relentless innovation in phishing, with hundreds of ransomware strains or variants deployed in the wild over the past few years. We see a similar level of innovation and development around backdoor trojans, which have steadily become stealthier, more capable, and increasingly deadly.
Malicious actors do not just innovate around traditional, malware-based payloads, a process which typically involves layering on ever more dense and sophisticated forms of obfuscation and increasingly dangerous functionality. No, these actors also develop new ways to extract exploitable data from targeted organizations.
In this piece we will look at two notable developments in the range of phishing emails forwarded to us by customers using the Phish Alert Button (PAB). We will close by considering the case of an odd and puzzling phish shared with us that speaks (somewhat ironically) to the sorry state of data privacy and security at present.
Pay Stubs & Wage Statements
One of the more curious new phishes that we've seen over the past few months involves phishing emails requesting copies of pay stubs and wage statements. Both are obvious variations on the W-2 phishing campaigns that erupt every year around tax season. Already familiar with the ways in which this kind of employee data can be exploited for fraud, some malicious actors are now turning to phishing attacks targeting the same kind of data, but with versions that can be conducted year round.
We ourselves almost missed the rise of pay stub phishes, as they seemed so innocuous when we initially encountered them. Moreover, because these emails typically request a single, specific pay stub for one employee (instead of a complete collection of W-2 statements covering an organization's entire employee base), these emails seem designed to "fly under the radar" and not attract undue attention.
These malicious emails are simple, direct, and dispense with any attempt to construct believable back stories or pretexts for the request. In short, they invite an unthinking, reflexive response from targeted users.
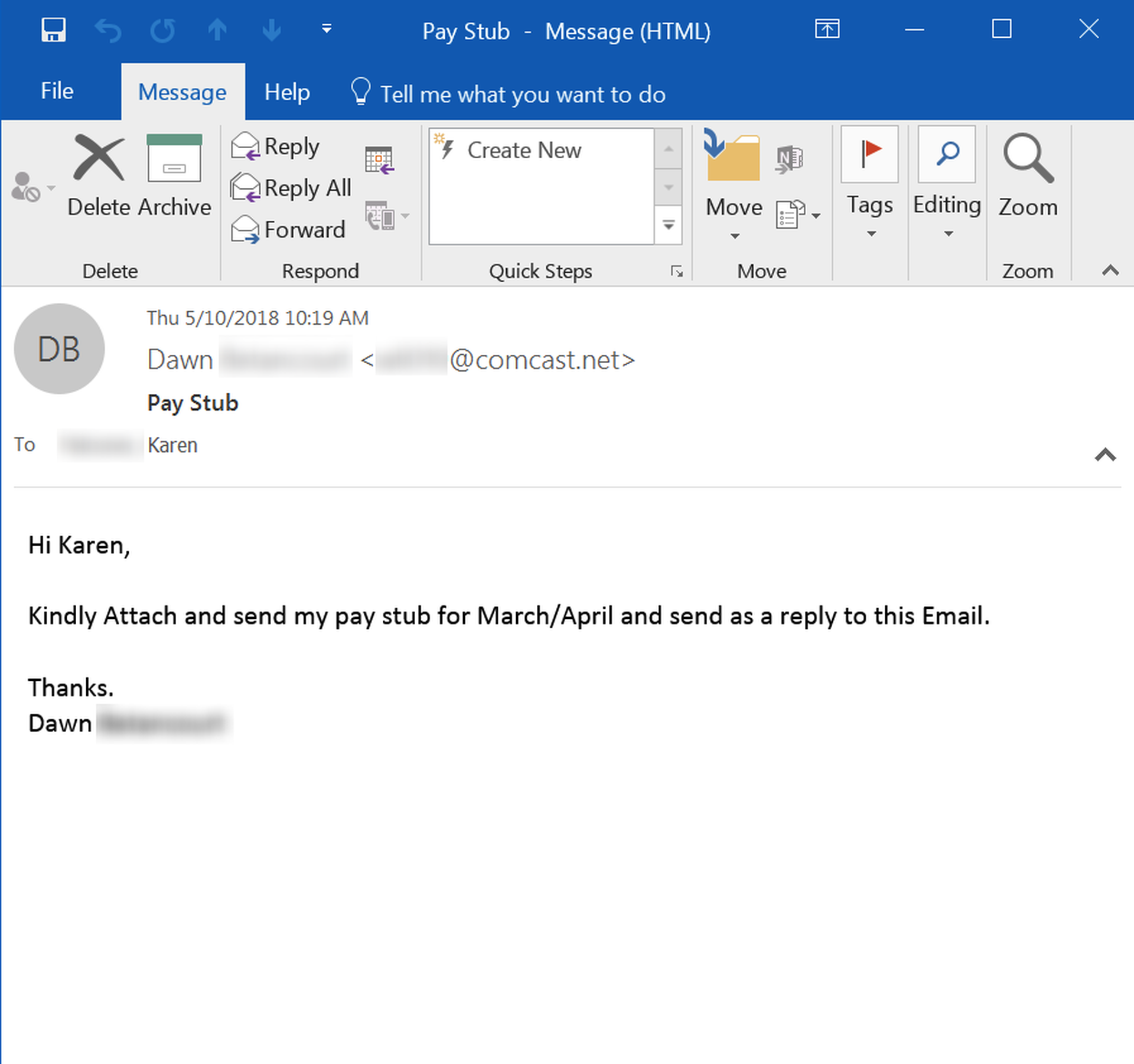
Several things eventually caught our eye. First, these phishing emails use almost identical language with small variations. Second, every single example that we've seen uses an oddball Comcast.net email address, all with nonsense usernames of similar length. We strongly suspect that this particular campaign is being prosecuted by a single group of malicious actors. We also suspect that this group is enjoying some success with the campaign, as it seems to have acquired legs over the past two-three months.
Whoever this group is, the pay stub phishes we've seen tell us that these bad guys have done their research. These phishes spoof presidents, CEOs, and other C-level executives within targeted organizations. Moreover, these phishes almost unfailingly seem to land in the inboxes of employees whose work involves payroll processing.
Pay stubs typically contain much the same kinds of data that can also be found on W-2 statements, which means that they can be exploited for identity theft and other forms of financial fraud. Given that the requested pay stubs are for senior executives, the bad guys are clearly calculating that the high value of the target more than makes up for the low volume of data requested.
Although we have not seen any email exchanges between targeted employees and the malicious actors prosecuting this campaign, we do suspect that these pay stub request could be used as a pretext to finagle help gaining access to online payroll services, which most companies are using these days.
Another variation on the standard W-2 phish that we've seen is the request for "wage statements."
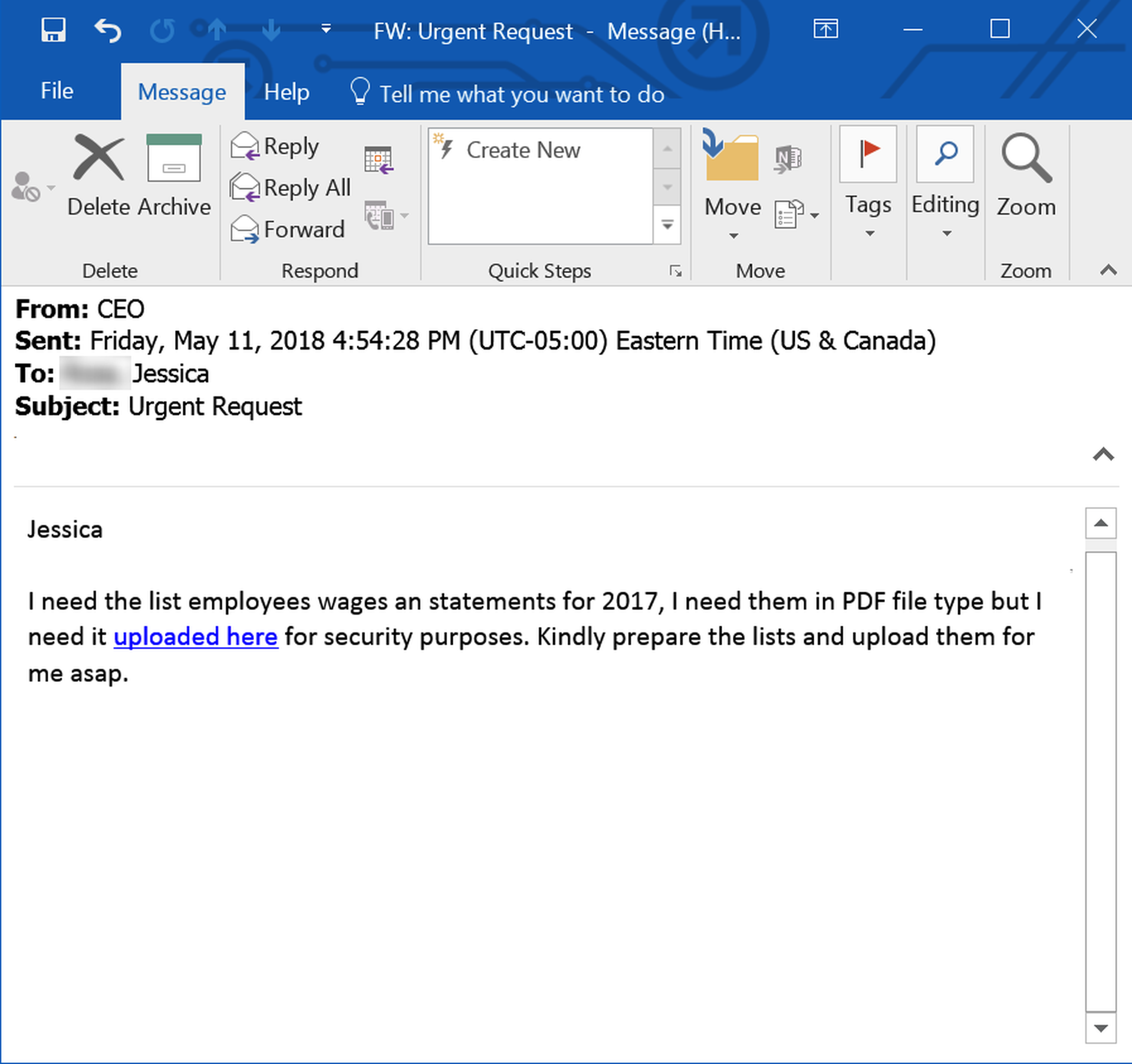
Although it is not entirely clear what specific documents are being requested here, if malicious actors, however, confused they may be themselves, manage to get one of your overly solicitous employees in a back-and-forth, there's no telling what the bad guys could walk away with. Professional, confident men in need of money can be awfully persuasive.
ZoomInfo Logins
Payroll is one obvious source for highly valuable and easily exploitable data for malicious actors. But it is hardly the only one. And the next source of exploitable data may not seem overly obvious to potential targets, because that data actually lies outside the company.
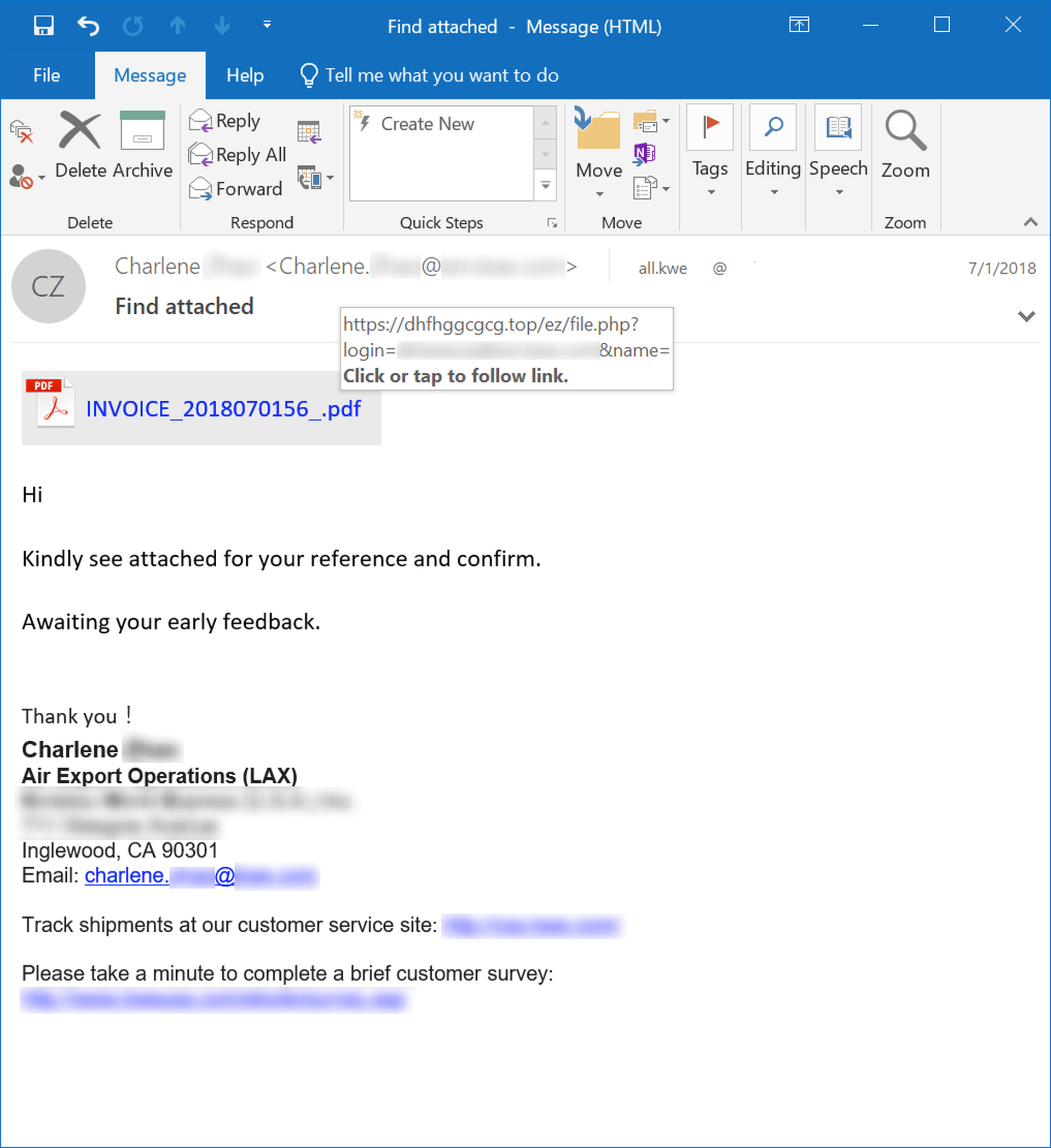
Around the same time that we first noticed a rise in pay stub phishing emails, we also saw an increase in phishes attempting to trick employees into coughing up credentials for ZoomInfo, a SaaS-based B2B database provider focused on delivering actionable sales and marketing data.
We have encountered a variety of ZoomInfo phishes. Some spoof high-level executives and simply request employees to hand over login credentials for ZoomInfo...
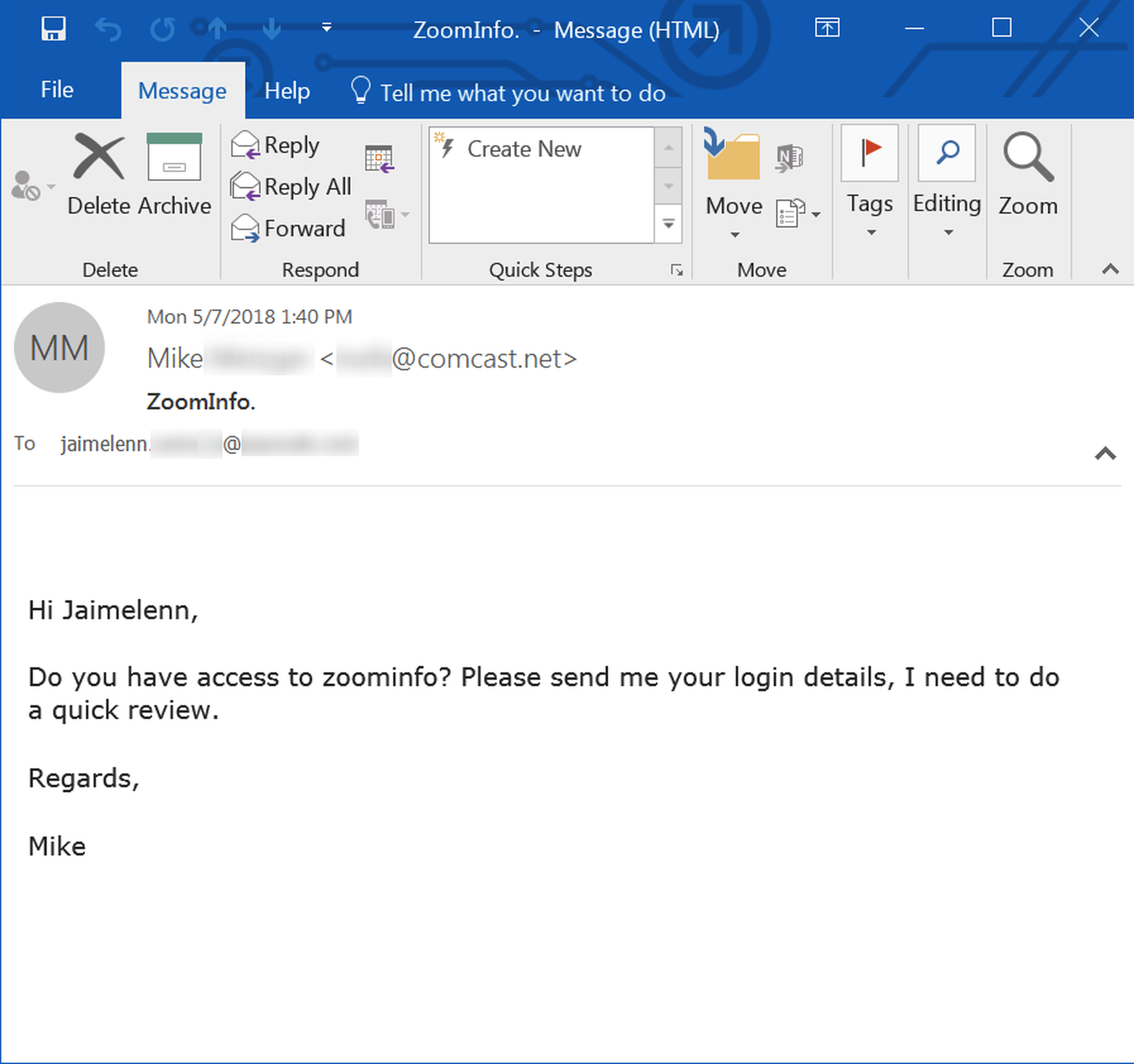
Interestingly, this email hails from an oddball Comcast.net email address very similar to the ones used in the pay stub phishes discussed above, suggesting that the same group may be responsible for this campaign as well.
Other ZoomInfo phishes use different social engineering schemes derived from the familiar range of credentials phishes:
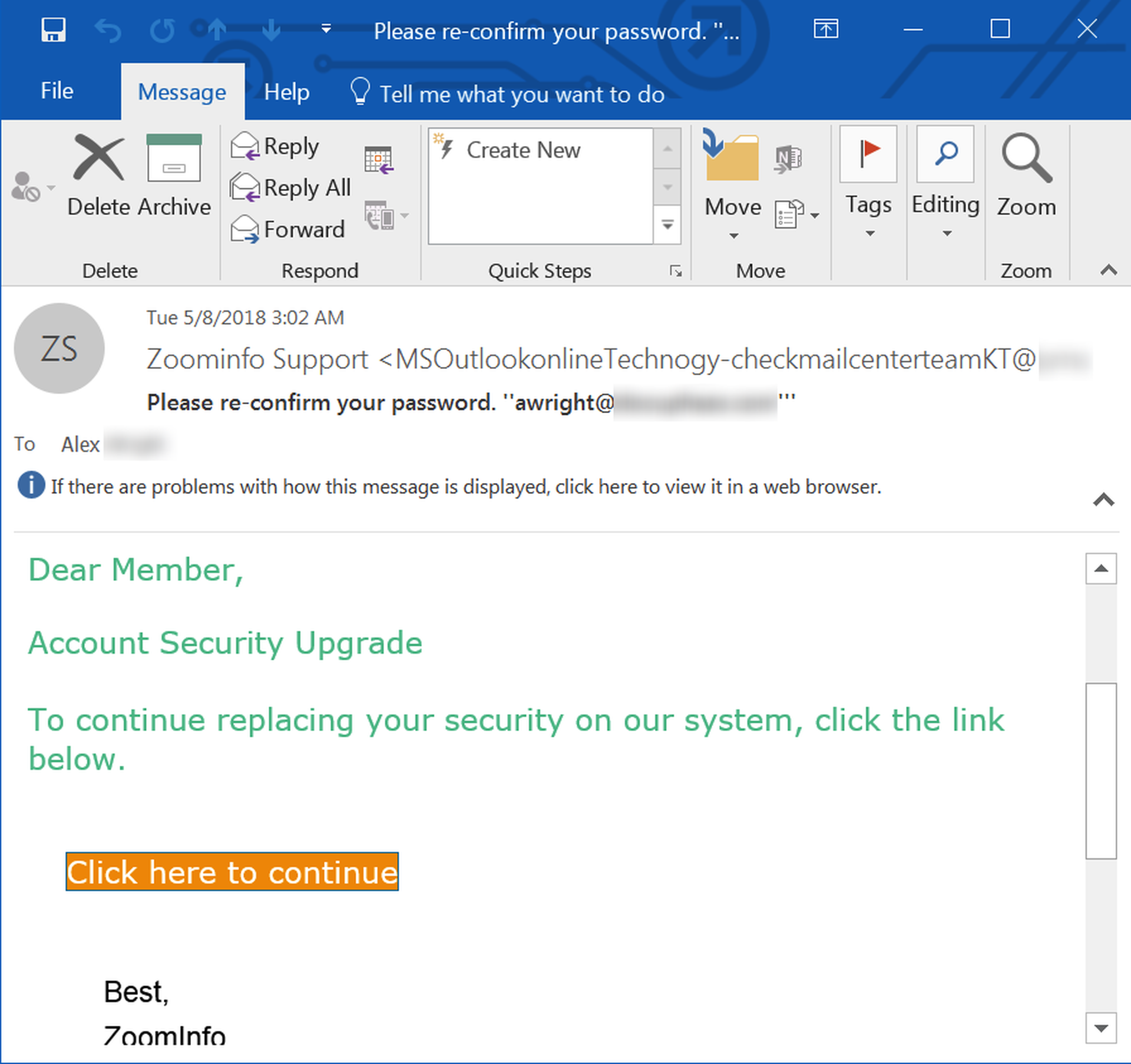
Whatever the approach, they all lead to web pages established to harvest ZoomInfo login credentials:
Most credentials phishes that we're familiar with seek credentials for employee email accounts (which can be leveraged to further exploit organizations as well as their customers, partners, and clients), bank accounts (which is where the money is, obviously), or online accounts for other financial services.
Malicious actors behind ZoomInfo phishing campaigns, however, are seeking to gain access to commercially valuable contact data that can be exploited to facilitate highly targeted phishing attacks against a range of potential victims.
Consider what ZoomInfo offers subscribers (according to its web site):
- Get access to direct dial phone numbers and email addresses.
- Designed for sales, marketing, and recruiting professionals.
- Search a range of accounts or narrow your results to find specific personas.
- Build targeted lists of contacts within your territory, key accounts and target industries.
- Use advanced account targeting capabilities to develop a list of key accounts within your territory or industry.
- Stay informed with account targeting watch lists that provide up-to-date insights and personnel changes within your target accounts.
- Access the right contacts within your accounts to connect, engage, and win more business using an account targeting strategy.
Just as ZoomInfo's data can be valuable to organizations looking to target particular individuals, organizations, and industries for sales and marketing purposes, so, too, can that data be exploited to leverage sophisticated phishing campaigns.
And, it's important to note, that data provides the bad guys the wherewithal to target their phishing campaigns based not just on the contact data for others but on the curated lists your own organization has developed and stored within ZoomInfo. Those lists could very well provide malicious actors an invaluable map of your clients, customers, and partners -- a map such actors would not hesitate to leverage in order to exploit the trust your organization has built with those clients, customers, and partners.
These ZoomInfo phishing campaigns should alert IT staff that it's not just the valuable data stored in-house that must be protected, but the data your company might have access to via SaaS-based subscriptions offered by companies like ZoomInfo. The lowly credentials phish may not be as spectacular and attention-getting as a ransomware attack, but it has the potential to bleed out your organization while your attention is focused elsewhere.
Even Bad Guys Can Jump the Shark
The last phishing email we shall look at is one of the more puzzling attempts to strong-arm money out of potential victims.
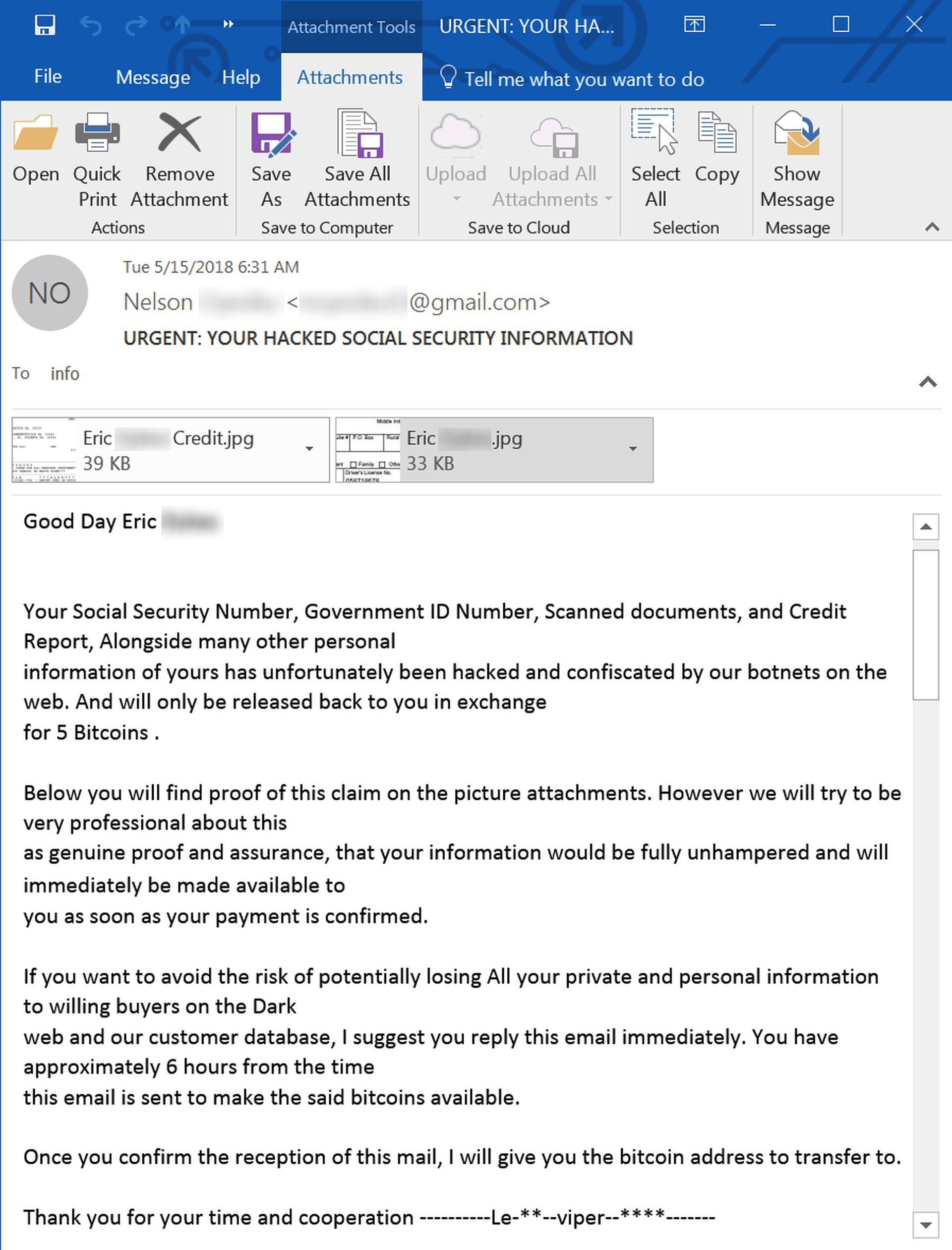
Accompanying this rather windy phishing email is a collection of rather convincing-looking financial documents and forms (which we've obscured just in case they are, indeed, the real thing):

As ransom demands go, this one is a head-scratcher. Not only is the ransom price exorbitant (five Bitcoins = approximately $34,000 at the exchange rate current at the time of writing), but the malicious actors behind this phish seem to be unaware of the most salient fact concerning the data they seem to think is so valuable. Put simply, the data they're attempting to hold for ransom has already been commoditized.
The sheer number of data breaches at financial institutions, payment processors, retailers, and government entities over the past ten years means that only a fool would pay five Bitcoins to keep this data ("Social Security Number, Government ID Number, Scanned documents, and Credit Report") private.
Unsurprisingly, this phish doesn't seem to have acquired legs. It does stand, however, as a bitterly ironic demonstration of the sad state of data privacy and security. I mean, what has the world come to when a poor thief can't even make a dishonest buck off of illegally purloined data?
Conclusion
Bad guys love data. Data is money. Data is opportunity. Data is power. Data means the difference between malicious actors having to rely on spray-and-pray phishing campaigns that churn through the same old social engineering schemes ("Please re-confirm your password;" "Dave has shared a confidential file with you," etc.) and the ability to push sophisticated spear-phishing campaigns that hook unsuspecting users into coughing up the organization's crown jewels, to say nothing of the CEO's or president's crown jewels.
With the bad guys increasingly leveraging commercial-grade data to craft convincing, sophisticated phishing emails targeting your users by name and position, those users need all the help they can get. That means stepping your users through New-school Security Awareness Training so that they can see through the increasingly dangerous emails landing in their inboxes and you can test and verify their journey to becoming "woke" to the threats you know they will encounter every day.



