Vendor: Smokescreen
Price: $7,750 per year
Contact: www.smokescreen.io
Quick Read
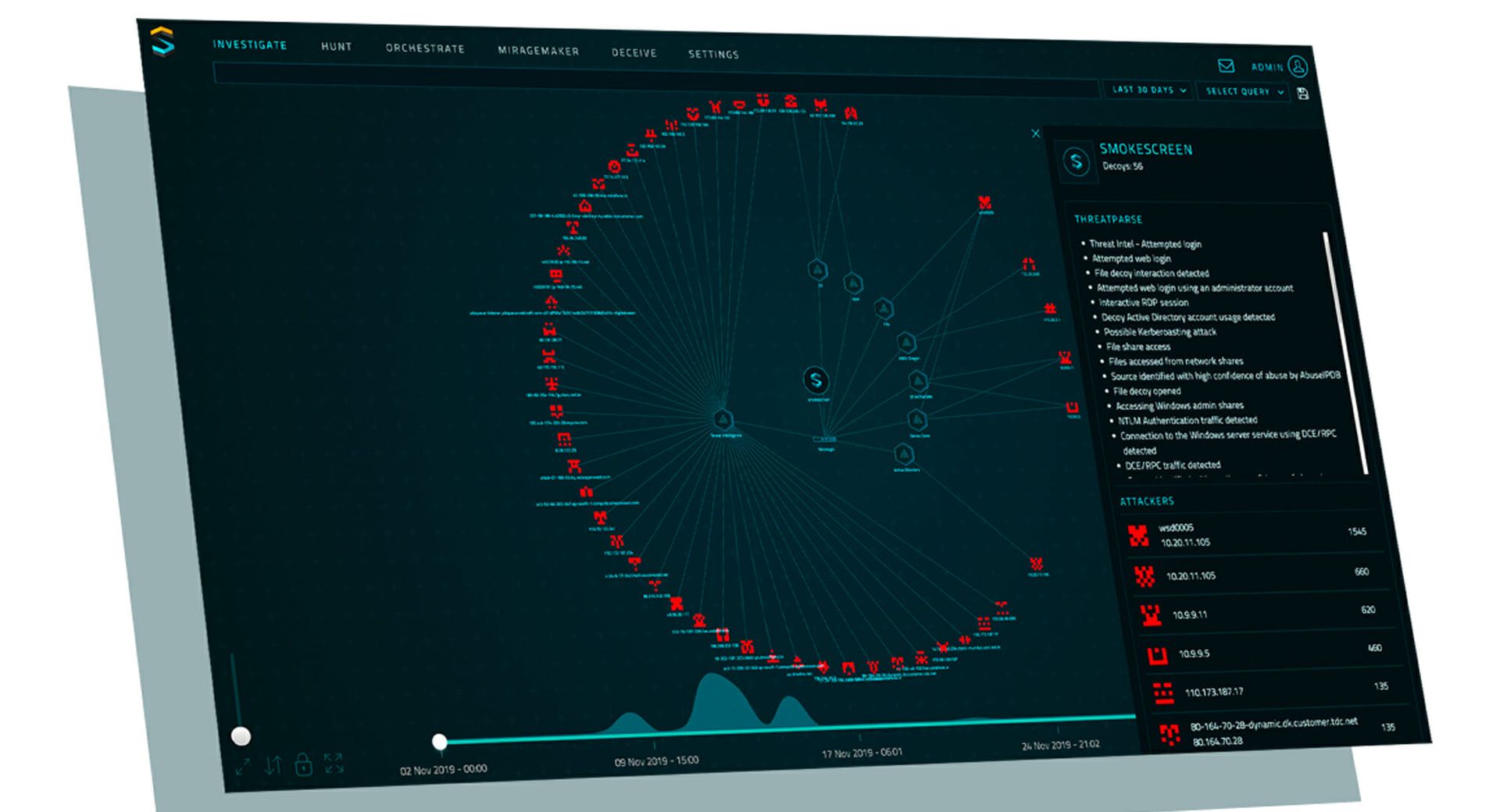
What it does: Smokescreen IllusionBLACK uses believable decoys to detect targeted threats accurately, efficiently, and in real-time.
What we liked: MirageMaker simplifies deception design immensely. We also really like ThreatParse and its ability to conduct natural language reconstruction of attacks, summarizing log information and translating it into plain English to make it as readily digestible for analysts as possible.
Security pros will find Smokescreen IllusionBLACK an architecturally flexible, deception-based threat defense platform that uses believable decoys to detect targeted threats accurately, efficiently, and in real-time. Most security and deception solutions are challenging to deploy, tune, and use and the early versions of IllusionBLACK were similarly complex. The platform has since undergone several successful revisions that have simplified and eased the feel of it, making it now a tool security teams look forward to using.
Smokescreen has unique, private threat intelligence, composed of honey pots, that it publishes on the internet and decoys that it deploys on subdomains. These deceptions actively engage with targeted threats and record all the events that occur during their interactions. The information collected during these interactions gets compiled as threat intelligence and becomes part of the private threat intelligence Smokescreen uses.
MirageMaker runs as the decoy design component of the platform that drastically simplifies deception deployment. It takes keyword inputs from analysts and automatically selects decoys relevant to the layout of their network environment, culling from a library of decoys which it updates every time it detects a new system. There are numerous Active Directory deceptions geared towards protecting the phonebook of the internet. These deceptions are loaded directly into the real Active Directory and have several capabilities to detect adversarial behaviors and engagements. Autonomous deception creation reduces complexity and the time to deployment, thereby increasing the value of the product. However, analysts may also create their own highly flexible, custom decoys that are fully configurable.
IllusionBLACK has self-protection capabilities and countermeasures in place to combat adversarial attempts to detect or bypass deceptions. There’s no way an attacker can differentiate between a decoy and a legitimate asset. Once an adversary interacts with a decoy, IllusionBLACK raises a silent alarm and collects information on the attacker’s actions and intentions. Counter-deception abilities impair an attacker’s network performance and detect all fingerprinting attempts.
Available integrations work seamlessly with several SOAR platforms, while this platform has its own orchestration capabilities with simple rule configurations that initiate customizable threat responses in real time. The orchestration in this platform lets it issue automatic responses and adapt to customizable workflows so analysts may focus on threats that demand human investigation.
The dashboard has a valuable and intuitive Investigative View that displays all the logged forensics and attacker information an analyst needs, drastically reducing the mean time-to-detect and time-to-know and driving security efficiency. ThreatParse is a proprietary technology built into the dashboard that conducts natural language reconstruction of attacks, summarizing log information and translating it into plain English to make it as readily digestible for analysts as possible. It also links this information to the MITRE ATT&CK framework and includes the risk scores assigned to adversaries, enabling security teams to prioritize the most pressing threats first.
Overall, security pros will find Smokescreen IllusionBLACK an effective deception solution. There are numerous decoy types available, each with powerful capabilities, including perimeter-facing, private threat intelligence and the proprietary natural language attack reconstruction. This powerful and easy-to-use deception platform especially supports ultra large enterprises.
Pricing starts at $7,750 per year and includes support with all subscription options. Additional training and support options are available for a fee.



