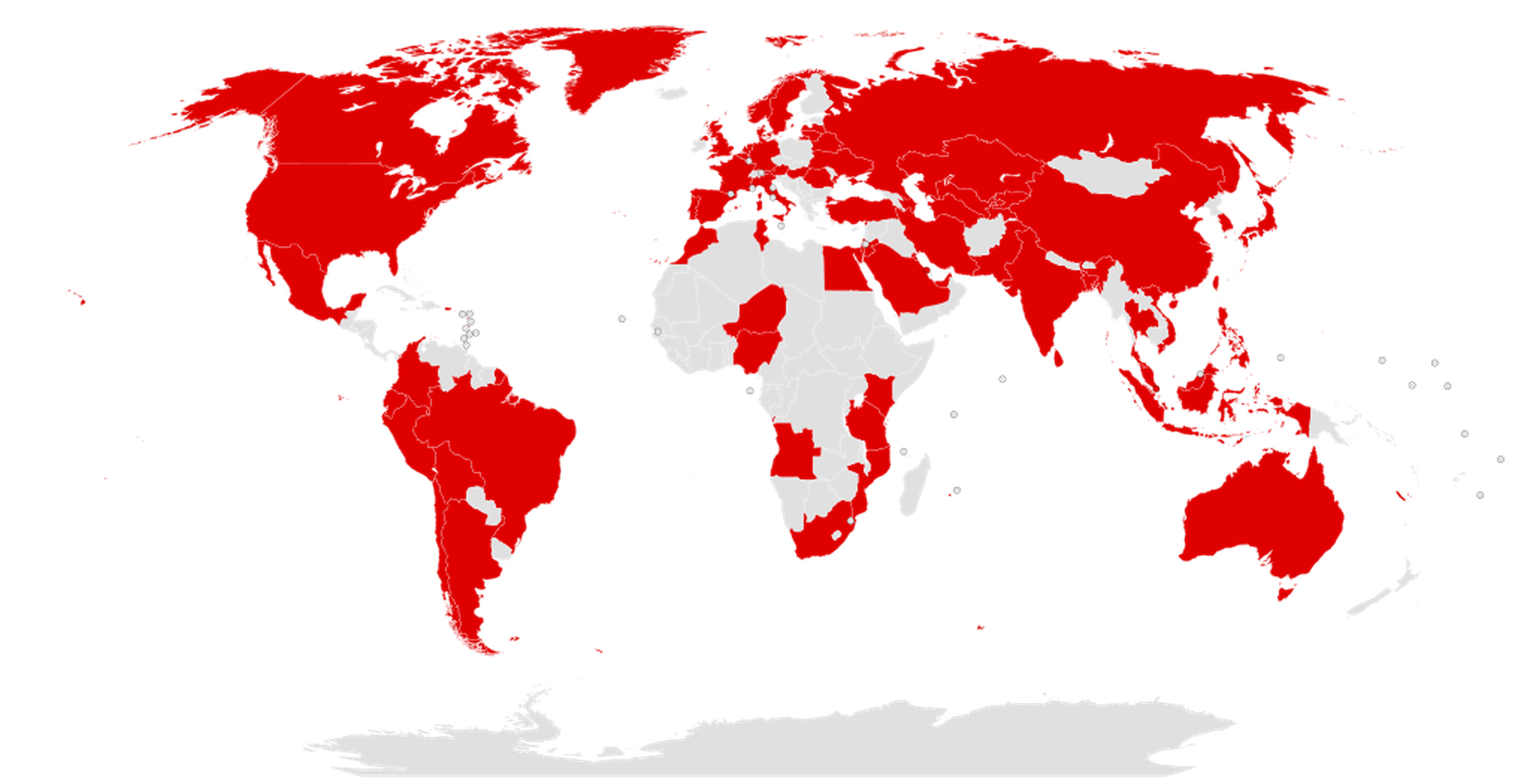
Ransomware has emerged as a particularly insidious form of cyberattack that doesn’t necessarily infiltrate IT infrastructures and networks to steal data. Once inside, attackers hold data and operations “hostage” – often threatening to sell data or go public if the ransom isn’t paid – adding complexity to an already destructive breach.
It’s critical for an organization to prepare for a ransomware attack, now more than ever as reports about ransomware attacks on hospitals have dominated the tech news. They need to fuse roles between threat intelligence, the incident commander, as well as legal and compliance to manage a potential crisis. And in today's environment, much of this work gets done remotely, necessitating primary and secondary methods of communication.
Ransomware kits and services are abundant and inexpensive on the dark web, enabling even novice cybercriminals. Making matters more complicated, sophisticated actors are evolving. Sodin, for example, exploits known Oracle, Windows and managed service provider vulnerabilities to encrypt data and destroy shadow backups. Several ransomware groups have also made good on their threats to publicly release the data of organizations that do not pay up. REvil/Sodinokibi, DoppelPaymer, Clop, LockBit, and Maze are among the first to court media attention for its tactics.
COVID-19 compounds the challenge
The global remote work environment created by the COVID-19 pandemic has intensified the threat environment. A recent Newsweek Vantage survey of executives of critical infrastructure organizations revealed over half (52 percent) cited employees as the greatest threat to cybersecurity. This concern intensifies as employees are now more likely to log into work accounts outside the office. Employees working from home may also have less rigorous cyber hygiene, such as not proactively connecting to VPNs or installing security updates. Plus, isolated remote workers are increasingly susceptible to social engineering attacks.
Cybercriminals have learned to exploit these vulnerabilities by launching COVID-19-themed malware and phishing attacks in the form of video messaging and remote collaboration software. In this environment, power comes from preparation. There are three critical steps to remaining resilient in this complex threat environment:
- Deploy a multifaceted strategy. When dealing with a ransomware attack, it’s essential to understand how the actors initiating the attack may operate. Most actors allot a certain amount of time to make contact. Organizations should use this time to activate their response team to understand the situation, evaluate, and determine how to recover strategically. What are the business implications of possibly lost data, exposing sensitive information? Would the cost of paying the ransom outweigh the cost of restoration, damage to the brand, and business interruption? Because these questions are essential to an organization's negotiation strategy, answer them before a ransomware attack occurs.
Preparing beforehand and understanding the potential impacts will identify areas to invest in, like data backup and cyber insurance, often used to pay the ransom. In addition to a strategy, organizations should have a ransomware team ready in advance: the incident commander, threat intelligence, risk management, legal and compliance, outside forensic and negotiation provider, and outside counsel.
Once the company activates the team and roles are assigned, take steps to ensure the team can function remotely: install permissions and authorizations for remote access; set regular schedules for briefings and communications, since critical players are no longer able to walk down the hall to chat; and, install multiple forms of secure communication, such as chats, voice, and video.
- Know the attacker and environment. Ransomware attackers often “hide below the noise floor” before an attack by gathering information, communicating on the company’s network, and leaving malware. Understanding how attackers operate serves as the best defense. Consider the following when developing an internal and external and a proactive hunt program: What are the common tactics and technologies used by ransomware attackers in the industry the company operates in? Is there any unusual activity on the corporate network, for example, atypical activity tickets or unfamiliar devices? What are the environment’s vulnerabilities? Don't assume that everything is safe and business as usual on your network.
- Have a plan. A written response plan ensures the right information gets disseminated to the appropriate parties—from incident command to front-line response, across legal, to leadership, and to the public if required. Most importantly, it increases the odds of making strategic and well-informed decisions throughout the event. This plan should also address negotiations. Conventional wisdom says never to pay a ransom to bad actors, but it’s an individual business decision unique to each victim company based upon multiple variables. Questions to consider include the following: Has the company prepared for this type of attack? How quickly can it recover? How much money does the organization stand to lose from a shutdown of business operations? Would paying the ransom violate any laws or regulations? And, does the company have a robust data backup plan, and how quickly can it restore from those backups?
Ultimately, organizations that have invested in a thorough incident response plan before an attack happens are in a more resilient position when they actually face a real ransomware attack.
The work must continue once these critical plans are in place; it’s essential to train and test elements of the plan. Organizations should test their response plans and playbooks through simulated scenarios practiced by conducting tabletop exercises and wargaming to identify and discuss weaknesses and ways to address them. At a minimum, companies should review and test their plan annually to ensure that the plan and playbooks evolve with the ever-changing ransomware landscape.
Jerry Bessette, senior vice president, Cyber Incident Response Program, Booz Allen Hamilton