One day after Twilio announced a breach after an attacker successfully stole employee credentials in a phishing scam, Cloudflare posted on its blog Tuesday that it believes its employees were targeted in a similar attack.
While confirming that three of its employees entered their credentials into the phishing site set up by the attackers, Cloudflare said it was able to thwart the attack through its Cloudforce One threat operations team and physical security keys issued to all employees who are required to access the company’s applications.
Cloudflare shared its experience given the fact that the attacker is apparently targeting multiple organizations.
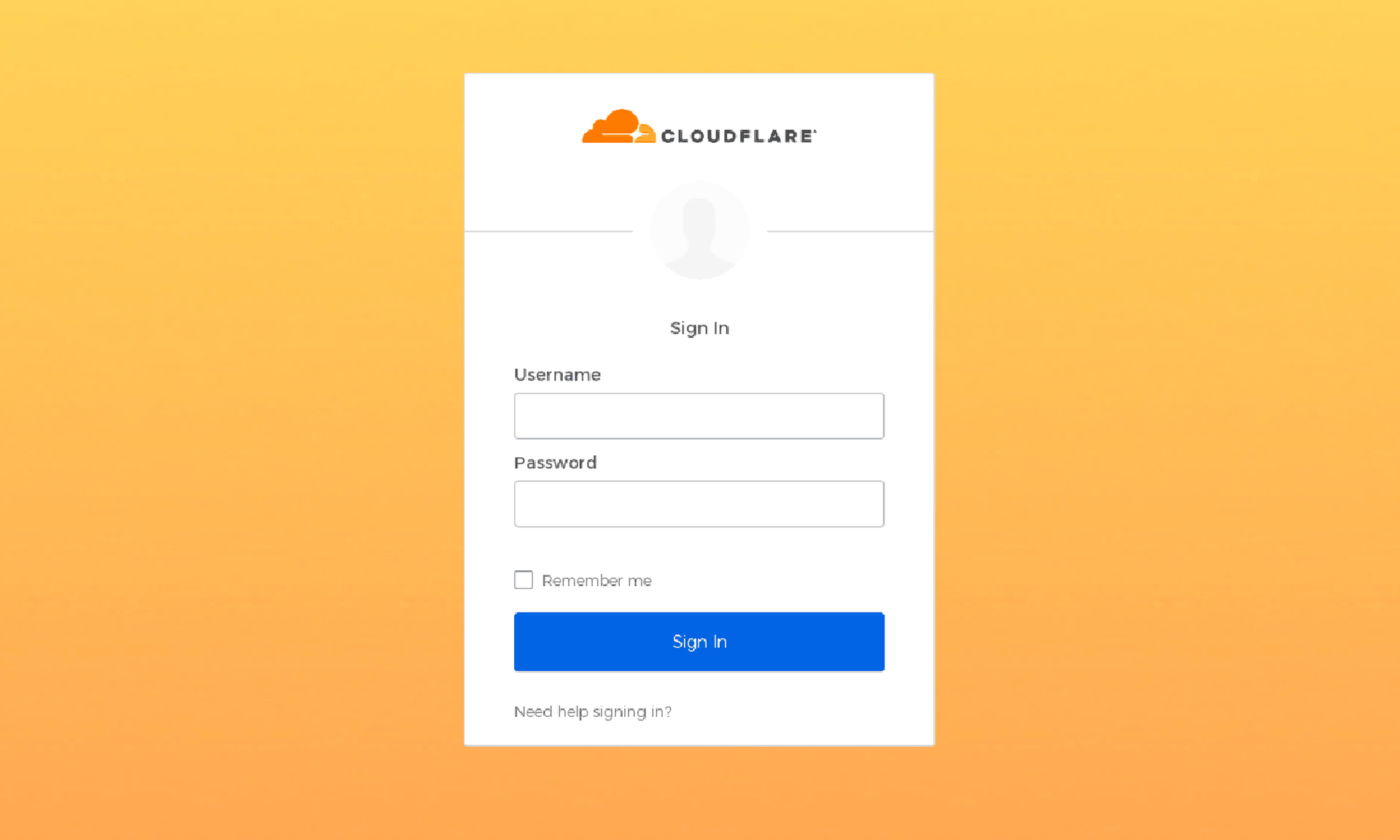
At least 76 employees received legitimate-looking text messages within a minute of each other on personal and work phones on July 20. The text said their schedule was updated and linked to what appeared to be a Cloudflare Okta login page from an official-looking domain: cloudflare-okta.com. The four phone numbers used to send the texts came from T-Mobile SIM cards and the domain was registered less than 40 minutes before the phishing campaign began, according to the blog post.
The credentials were relayed immediately to the attacker via messaging service Telegram when an employee filled out the fake login page. However, since Cloudflare uses FIDO-compliant security keys, the attacker was not able to access their systems.
The firm’s security team was able to determine that remote access software would have been delivered if the attackers were somehow successful in making it onto its systems.
The San Francisco-based company blocked the phishing domain, reset the credentials for the compromised employees, identified and took down the attackers’ infrastructure and updated its detections to identify subsequent attack attempts (no more were detected).



