Google rolled out a new, consolidated, cloud-based suite of software security solutions Tuesday, merging existing cloud security offerings and integrating threat intelligence and detection tools and services gained through acquisitions of companies like Mandiant and Siemplify.
The move crystalizes what many in the security market hypothesized during the last six months: A plan by Google to create a cloud offering more suitable for the enterprise, harnessing the vast resources and scale that the company dedicates to securing its own environment to deliver a managed service to smaller entities around the globe.
“Nation state actors are increasingly spending more time not just on governments but on enterprises of all sizes, from big banks to the small credit unions,” said Sunil Potti, general manager and vice president of cloud security at Google Cloud. “Ultimately when you take a step back, only companies like Google or maybe an Amazon or Apple who have invested in protecting themselves at scale can maybe thwart that; but if there’s an opportunity for companies of all sizes to inhale the capabilities that Google has built to protect themselves, to protect their own customers, then there’s a real opportunity to structurally solve this problem.”
Introducing Chronicle Security Operations
The suite, called Chronicle Security Operations, will combine security capabilities from Google Cloud, Chronicle’s security information and event management (SIEM) technology and software gained through Google’s $500 million purchase of Israeli security orchestration, automation and response firm Siemplify. It will also place much of that data under a consolidated display, pulling information and context in from other sources like VirusTotal and Google Cloud Threat Intelligence. At the head of processing all that security data will be Mandiant, another recent acquisition.
Google is also introducing two new security products.
The first, Confidential Space, is a trusted execution environment that uses a container optimized operating system to offer a secure, controlled place for multiple organizations to collaborate on projects and share sensitive data with each other. It builds off previous efforts by Google like Confidential Computing and Confidential Virtual Machines and is meant to support things like joint data analysis, machine learning modeling and projects where organizations wish to collaborate and share data but maintain control of the information and prevent appropriation or misuse.
The use cases Google offered include scenarios like banks and insurance agencies sharing joint customer data to root out fraud, healthcare and medical technology companies sharing information to speed up drug development cycles without exposing patient data and Web3 companies using remote attestation to buy or exchange assets.
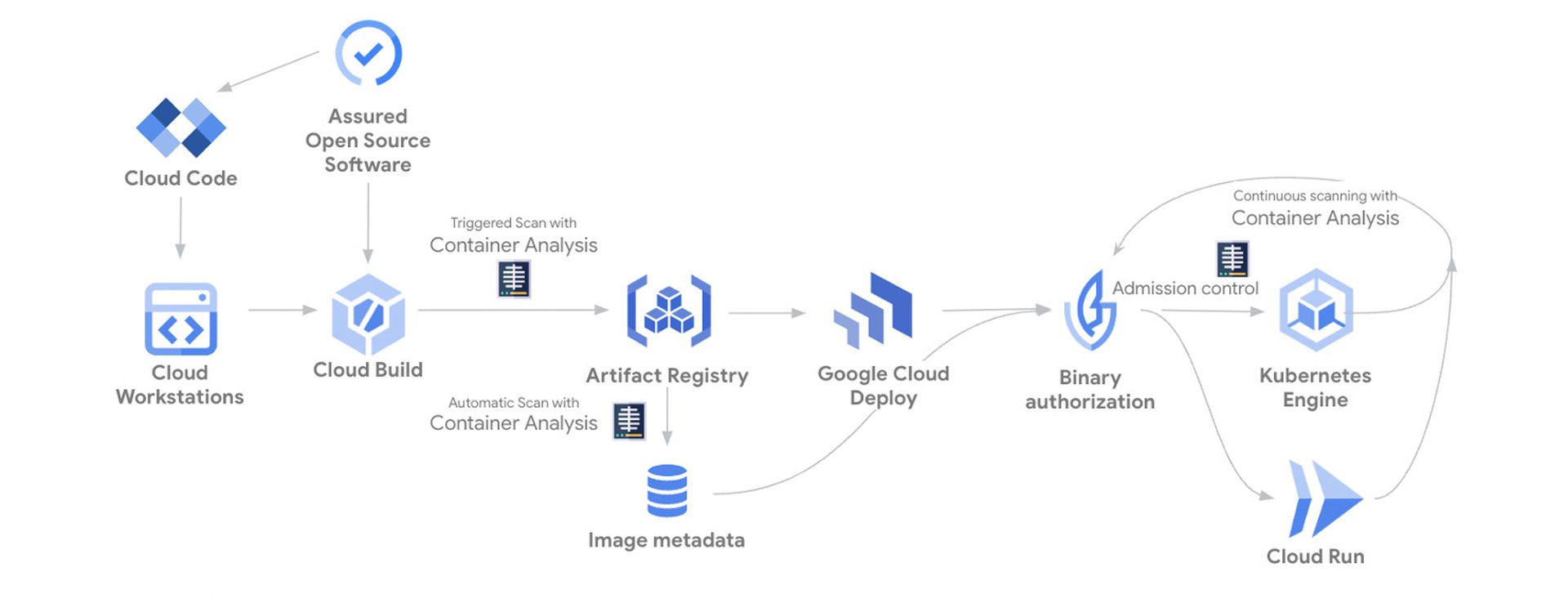
The second, called Software Security Shield, is a managed security solution that offers managed software development environments via Google Cloud, approved lists of open source software code packages that are regularly vetted for security by Google through scanning, fuzz-testing, analysis and other forms of curation, managed platforms for continuous development/continuous integration of applications and a policy engine for verifying the integrity of software code throughout the development and production lifecycle.
Sunil Potti, general manager and vice president of cloud security at Google Cloud, said the moves represent an effort to harness the vast resources and scale that Google dedicates to securing its own enterprise and push them out to smaller organizations as a managed service.
“Fundamentally we’re in this accelerating cyber situation where nation state actors, for example, are increasingly spending more time not just on governments but on enterprises of all sizes, from big banks to the small credit unions,” said Potti. “Ultimately when you take a step back, only companies like Google or maybe an Amazon or Apple who have invested in protecting themselves at scale can maybe thwart that; but if there’s an opportunity for most of these companies of all sizes to inhale the capabilities that Google has built to protect themselves, to protect their own customers, then there’s a real opportunity to structurally solve this problem.”
Mandiant: The brains of the operation
The announcements also doubled as an opportunity to discuss the $5.4 billion acquisition of Mandiant, which Google finalized in September.
Google chief information security officer Phil Venables said the pairing of Mandiant with Google Cloud “combines what we’re both good at”: Google’s SIEM and SOAR tech focusing on reactive defensive security tasks like event monitoring, logging analysis and digital forensics, and Mandiant’s offerings providing more “proactive” capabilities, that provide visibility into an organization’s overall attack surface and validate their existing security tools and processes.
“We’ve already got excellent security information and event management and SOAR capabilities with things like Chronicle and Siemplify. With Mandiant, we can take all of that threat intelligence and incident response capability and align it with that and so it’s a really great natural and complimentary combination,” Venables told reporters.
Google will retain Mandiant’s name and brand, and founder Kevin Mandia said his organization is “still do[ing] the work we’ve always done.” He predicted the integration of Mandiant into Google Cloud will “amplify” the impact of Mandiant intelligence by leveraging Google’s vast ecosystem of software and integration partners to reach a wider audience.
Google’s purchase of Mandiant came a little more than a year after the threat intelligence firm split with FireEye (now Trellix) after seven years of partnership. At the time, Mandia spoke about the need to decouple Mandiant’s intelligence from FireEye security controls and products in order to present insights and analysis free from bias.
Now the company will be tied to Google and its products, but Mandia told SC Media that he does not view the two situations as analogous. While part of FireEye, Mandiant’s analysis was restricted to telemetry from FireEye endpoints, firewalls and network security monitoring tools. Google’s portfolio is not reliant on those products or controls, and maintains integration partnerships with other threat intelligence firms like CrowdStrike, Cybereason and Fortinet that will still allow Mandiant to incorporate telemetry from a wide variety of sources.

“As we respond to breaches and get to a mastery of here’s is what bad looks on a network, this is what unauthorized or unlawful or simply unacceptable behavior looks like and all this different telemetry, Google is best suited to bring that to market,” Mandia said. “So when I said we needed to be controls agnostic, that’s what I meant. At Mandiant we know what bad looks like, whether you’re using [endpoints from] Sentinel One, CrowdStrike’s, Symanetc, McAfee, Carbon Black…we want to work with Microsoft Defender, we want to work with all of them and impose security automation on top of all these control products that create the telemetry, so it’s still a perfect fit.”
He analogized Mandiant’s role in the Google Cloud security ecosystem to that of a higher intelligence sitting on top of a broader security operation, culling and organizing data from disparate technologies and sources and then using them to inform strategy and decision-making.
“When I think about it, I think of a physical world analogy: there’s going to be a thousand companies that make cameras, but there would need a brain for all the cameras to say there’s an intruder coming in the house or there’s something else happening…I see one of the things we can do best at Mandiant combined with Google is be that brain, be the hub for all the spokes,” he said.
What's next? Google needs to get out of its own way
The moves announced by Google represent an attempt to stitch together many of the company’s core security offerings – some developed in-house, others added via acquisition – into a unified, cohesive managed service that is relevant to customers large and small as it seeks to compete with Amazon and other major cloud security providers.
But experts told SC Media it will take more than throwing cash around to make Google a major player in the security space.
Allie Mellen, an analyst at Forrester, called the news the most significant move for Google’s security analytics portfolio since the merging Google Cloud and Chronicle in 2019. Up until now, she said Chronicle has lacked critical enterprise features, like SOAR, that are often a requirement in a security analytics platform market that is trending towards consolidated toolsets.
The unification of Google’s Chronicle’s SIEM with Siemplify’s SOAR and Mandiant's threat intelligence helps in “bridging the gap for Google to an enterprise offering.”
“Mandiant’s quality security services on top of Chronicle’s storage, querying, and SOAR capabilities are a powerful combination, especially since very few competitors in the Security Analytics Platform market can offer the same with the same level of cohesion and partnership,” “However, some of the features need to mature before the product alone will be a robust SIEM offering, such as the analytics capabilities,” said Mellen.
Google’s success may also depend as much on how successfully it leverages the human expertise it has inherited as it does the technology. Mellen cited the addition of a known and trusted security brand in Mandiant as a real difference maker, a question that others raised as well.
Adrian Sanabria, director of product management at Tenchi Security and host of the Enterprise Security Weekly Podcast, told SC Media that while Google has thrown a lot of money and resources into its cloud security program and brought in smart people like Mandia, it’s not yet clear how influential they will be in steering the company’s decision-making. For example, lessons gleaned from incident response engagements carried out by Mandiant can offer a “strong feedback loop” to Google’s product team that will allow them to adjust and keep their technologies relevant for the latest threats.
He compared the situation to Cisco purchasing SourceFire in 2013 and giving founder Martin Roesch wide latitude to reshape their broader security program. Google’s success in this area may depend on taking a similar tack by empowering experts like Mandia.
“Like Cisco in the early 2010s, Google currently isn't taken seriously as a security company," Sanabria said. The company "clearly has the resources to build an impressive security offering and has a ton of smart people. They keep getting in their own way, need to collaborate more internally, and are sorely in need of effective leadership and marketing.”




