One of five newly disclosed vulnerabilities found in certain Contec Health patient monitor medical devices could cause a “mass DDoS attack on all CME8000 devices connected to the same network,” according to a Cybersecurity and Infrastructure Security Agency alert.
The security firm Level Nine reported the vulnerabilities to CISA. However, “Contec Health has not responded to requests to work with CISA to mitigate these vulnerabilities.”
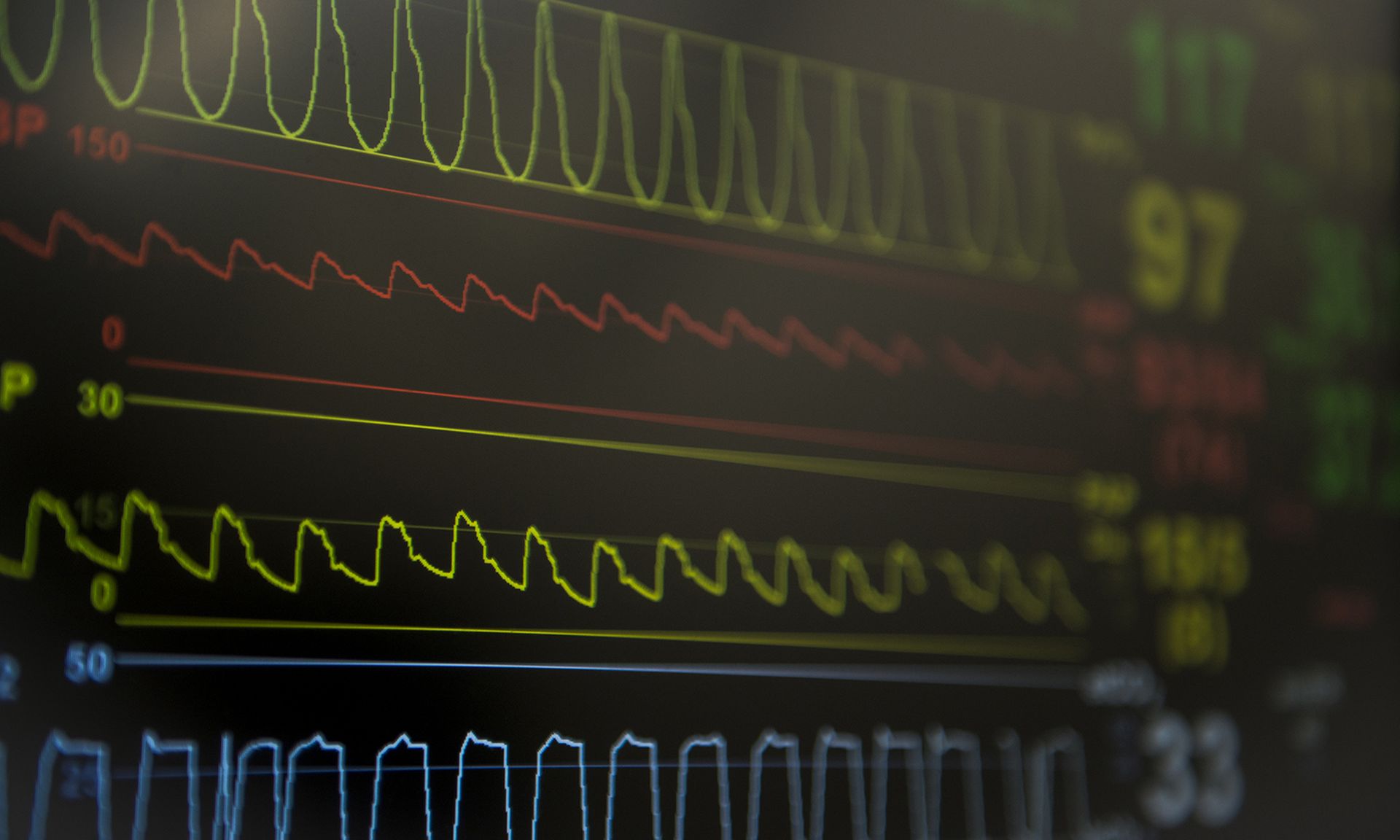
The flaws are found in Contec CMS8000 ICU Vital Signs, two of which pose serious risk to the device and the healthcare network. The most critical of the vulnerabilities is an uncontrolled resource consumption in the CMS800 device, which “fails while attempting to parse malformed network data sent by a threat actor.”
As a result, an attacker with network access would be able to “remotely issue a specially formatted UDP request that will cause the entire device to crash and require a physical reboot.” If the actor then sent a UDP broadcast request, it would cause a DDoS attack.
The second most pressing bug is caused by improper access controls, which would enable an attacker “with momentary access to the device” to plug in a USB drive and install a malicious firmware update, which could cause permanent changes to the functionality of the device.
The device lacks authentication or controls that would prevent a threat actor from performing the “drive-by attack” on any CMS800 device.
The other three flaws rank between 3.0 and 5.7 in severity and are tied to the use of hard-coded credentials, active debug code, and improper access control where the device fails to “properly control or sanitize the SSID name of a new Wi-Fi access point.”
“A threat actor could create an SSID with a malicious name, including non-standard characters that, when the device attempts connecting to the malicious SSID, the device can be exploited to write arbitrary files or display incorrect information,” according to the alert.
CISA warned that a successful exploit of these flaws could enable access to a root shell, or use hard-coded credentials to make configuration changes. An attacker with privileged credential access could also allow for the extraction of patient data or the modification of device parameters.
Fortunately, there have been no known public exploits that specifically target these flaws, nor are they remotely exploitable.
The alert provides entities with recommended mitigations to reduce the risk of exploit, which include disabling the UART function at the CPU level, leveraging unique device authentication prior to enabling access to the terminal or bootloader, enforcing secure boot when possible, and placing tamper stickers on the impacted device case to note when a device has been opened.
CISA also provided general network mitigations to further protect vulnerable devices and shared best practice resources to bolster the overall healthcare network.
As the vendor has not responded to CISA’s requests to work together on a fix for the vulnerabilities, healthcare provider organizations are being urged to contact Contec Health for additional details on these affected products.
As previously reported, vulnerability disclosures are crucial in healthcare to support providers with remediating known flaws. Vendors should work closely with entities when security bugs are found to prevent exploitation.