The chair of the Cyber Safety Review Board said its initial review of the Log4j vulnerability “proved the concept” behind the board’s work and promised more action in the coming months. However, he also declined to directly address questions about whether there are any plans to investigate the SolarWinds campaign that led to its creation.
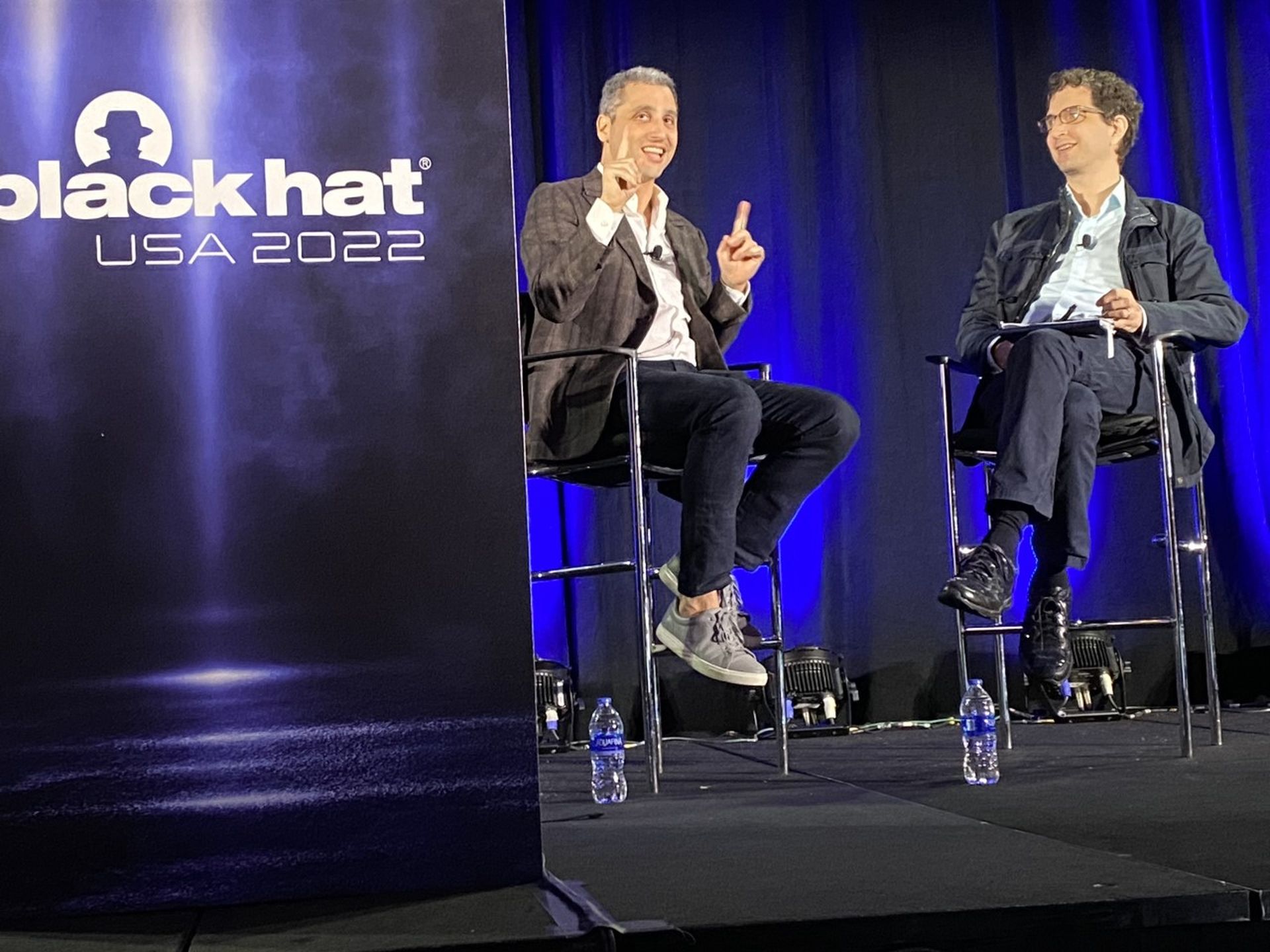
While speaking at the Black Hat cybersecurity conference in Las Vegas on Wednesday, Rob Silvers, undersecretary of Homeland Security for strategy, policy and plans, and chair of the CSRB, said that following their initial report on Log4j released last month, the board is spending its “offseason” building up permanent staffing and infrastructure. It’s also further refining and maturing its process using lessons drawn from the initial investigation.
Part of that work will include continuing to build on ideas that were executed in the wake of Log4j’s disclosure, like creating crowdsourced lists on GitHub of all the known products that contain the vulnerable code.
While the board will further refine its process over the coming months, Silvers cast the initial investigation and report as a success that brought together both government and industry experts around one of the most widespread and dangerous vulnerabilities in recent memory.
“I will tell you this: I believe that the first review proved this concept,” said Silvers. “There is nobody out there that thinks this is the wrong idea. This is — it’s pretty clear to me — going to be an enduring institution in the cybersecurity ecosystem.”
Following the panel, Silvers told reporters that the agency was already conducting follow up work on some of the recommendations, like directing DHS to allow its IT personnel to spend some work hours maintaining open-source software projects and engaging with academic institutions to make cybersecurity a more central component of their computer science degree programs.
“Companies and big government consumers that use a lot of open-source need to give back, they need to devote resources towards helping maintain open-source code and maintaining the security of open-source code … and we’re calling on big corporate consumers to do the same,” said.
Silvers told SC Media that there’s currently nothing to announce in terms of new investigations around other incidents but that they intend to go back to work “soon.” He also said in his panel remarks that the board was committed to releasing public versions of future reports.
“We’re committed to that. This needs to be transparent for the benefit of the community,” he said.
Log4j proved review board's concept, but what about SolarWinds?
However, he was also asked on three separate occasions — once by moderator and Black Hat organizer Jeff Moss and twice by reporters — what plans, if any, the board had to eventually investigate the SolarWinds campaign. The breach was specifically referenced in a White House executive order issued last year as the first order of business for the review board.
Each time, Silvers gave a variation of the same answer, indicating the pivot to Log4j came after discussions with the White House.
“We felt together with the White House that the best use of the board when we launched in February was to review Log4j. It was fresh, it was an extremely broad and wide impact and I think the report bears that out,” he told SC Media when asked directly if the board intended to investigate the SolarWinds Orion breach.
The Log4j report issued by the board does describe it as an “endemic vulnerability” that will “remain in systems for many years to come.” But it also notes that while there is no authoritative source of compromises related to the code, “generally speaking, exploitation of Log4j occurred at lower levels than many experts predicted, given the severity of the vulnerability.”
The impact of the SolarWinds campaign, by comparison, is clearer. Russian hackers compromised at least nine federal agencies (including the Department of Homeland Security) along with approximately 100 entities and private companies, including major tech companies like Nvidia, Cisco, Intel, VMWare and Belkin International, according to the Wall Street Journal.
The same day, two information security professionals, Tarah Wheeler and Victoria Ontiveros, gave a separate presentation on guidance for state and local governments around setting up their own cyber incident review process. At one point, Wheeler noted that “after more than a year and a half, we don’t have a coherent government report about what happened [with SolarWinds], where, why and how,” something that can allow rumors or opinions to supplant a fact-based analysis of the root causes. Without such an investigation, it can be difficult to hone in on the “multiple reasons why there are process failures, and multiple places that you can fix that process failure for the future.”
During the panel, Heather Adkins, vice president of security engineering at Google and deputy chair of the review board, suggested that while the board did not conduct a specific review of the SolarWinds campaign, many of the same lessons drawn from the Log4j investigation would apply to the Orion breach.
“I think another thing to keep in mind is that when we talk about software ecosystems, a lot of these events start to look the same, so while we didn’t look at SolarWinds as an incident specifically, we ended up touching on a lot of the things that would have come up with a review on SolarWinds about how secure software is built, the kinds of tools and the kinds of capabilities we need in the ecosystem,” said Adkins. “And throughout the report, we do make footnote references to areas of recommendations and findings that actually can relate to SolarWinds, so think we still got the benefit of looking at software through the lens of SolarWinds through that experience, but … I think Log4j was a big moment for all of us and it was the right thing to do at the time.”



