A phishing attack on ClearBalance, a loan provider of patient financing, potentially compromised the data of 209,719 patients in March. The health care business associate did not detect the intrusion until more than a month later, when the attacker unsuccessfully attempted to wire transfer funds from the impacted accounts.
ClearBalance prevented the wire transfer on April 26 and launched an investigation with assistance from a forensics investigator. The FBI was also contacted. The analysis found that multiple email accounts and the data they contained were accessed on several occasions between March 8 and April 26, when the attack was discovered.
The investigation also confirmed the actor also accessed the data stored in the emails, including protected health information.
The compromised data varied by patient and could involve names, tax identification, Social Security numbers, dates of birth, government-issued IDs, contact information, health account numbers and balances, dates of service, ClearBalance loan numbers, and other highly sensitive information. All patients will receive two years of credit monitoring and identity theft protection services.
Research shows these types of information are commonly used in fraud and other related schemes that directly target the patient. In April 2020, the Department of Health and Human Services Office of the Inspector General warned that stolen data could be used to bill for services never delivered to the patient, cyber scams, and even medical identity theft.
In response, ClearBalance issued a system-wide password reset and secured the network the same day the incident was detected, ensuring the threat was eliminated. Officials said they’ve also enhanced security measures to prevent a recurrence, including enhancing network access controls and updating procedures for reporting suspicious activity.
Florida Heart Associates cyberattack leads to 10-day intrusion
Just over 45,000 Florida Health Associates were recently notified that their data may have been taken after a cyberattack led to a 10-day hack of the network. Officials said they detected unusual activity on a number of computers within its network on May 19 and contacted law enforcement.
An investigation found threat actors gained access to the network on May 9. While existing security controls limited the impact of the attack, the attackers were still able to access company servers and possibly obtained data stored in the network.
The impacted data could involve patient information, such as SSNs, member identification numbers, dates of birth, and a range of health information. An investigation into the incident is ongoing. Florida Heart has since enhanced its safeguards, including the implementation of an endpoint detection and response tool. Officials said they’re also reviewing their privacy and security policies and procedures.
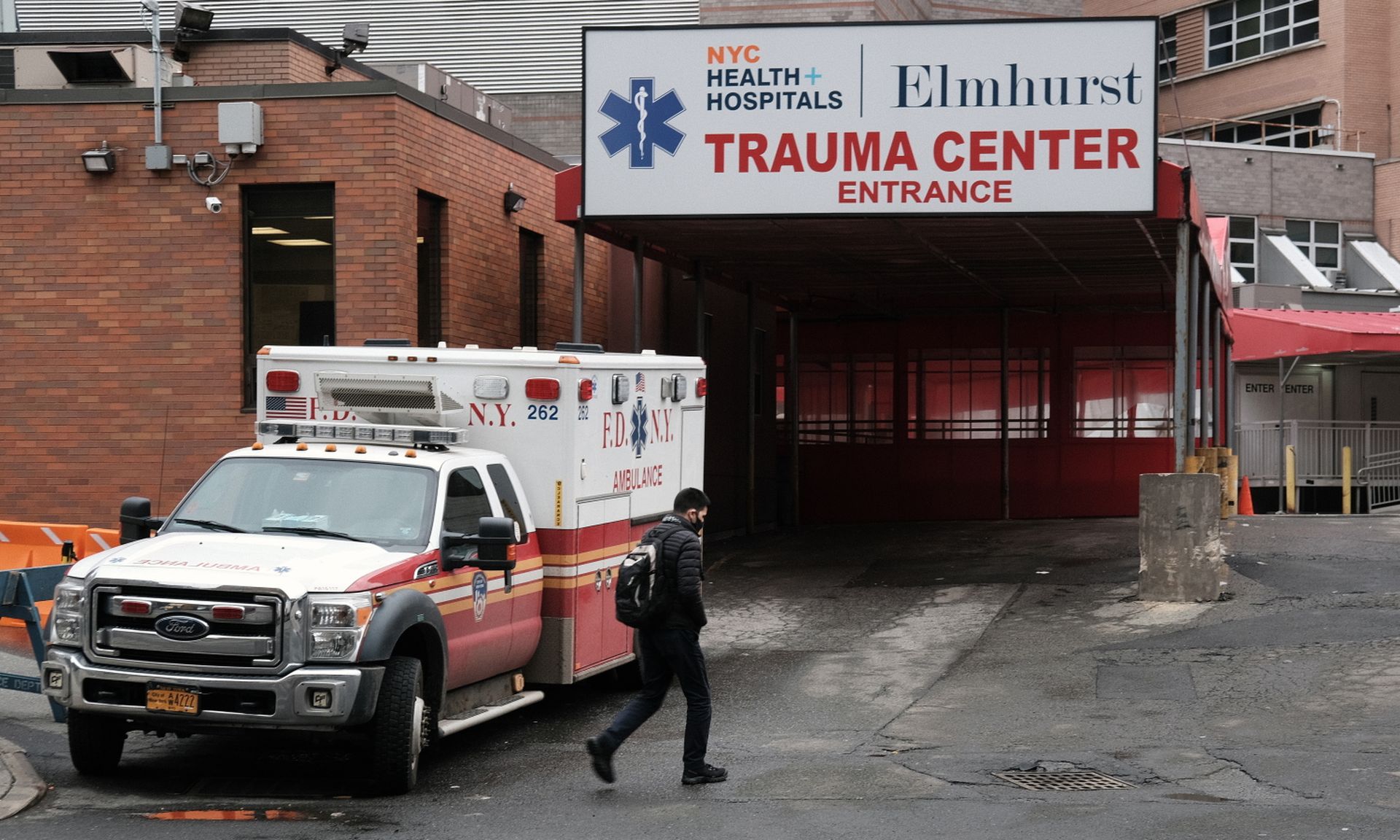
NYC Health + Hospitals added to CaptureRx breach victim tally
NYC Health + Hospitals reported the data of more than 43,000 of its patients was among the information accessed and/or exfiltrated during a ransomware attack on its health IT vendor CaptureRx, a business associate under the Health Insurance Portability and Accountability Act.
On Feb. 19, CaptureRx began investigating a ransomware attack on its systems, which found the attackers stole data belonging to a number of its clients.
The initial estimates showed 1.2 million patients were affected by the incident. But the latest tally shows there are 2.42 million breach victims from well over 200 covered entities. Capture RX has a running list of victims discovered during its ongoing investigation.
Notably, despite the massive victim count, it’s just the fourth-largest health care data breach reported this year. It’s also among three vendor-related incidents that compromised the data from multiple providers that includes Accellion and NetGain.
NYC Health discovered their patient data was exfiltrated on May 14, which included only patient names, dates of birth, and prescription information. No financial data or other identifiers were taken by the attackers. Capture Rx previously hired a third-party forensic firm to monitor the dark web for the stolen information. To date, there’s been no evidence the stolen PHI has been leaked on the dark web or public websites.
The attacker also purportedly returned the stolen data to Capture Rx with evidence it had been destroyed. As noted, security researchers warn against trusting the word of attackers, who’ve been observed falsifying evidence that they’ve destroyed stolen data.
Accellion adds the University of Maryland, Baltimore patients to breach victims
The data of 30,468 patients tied to the University of Maryland, Baltimore have been added to the Accellion breach tally, which already includes well over 3.5 million patients from about 11 health care covered entities.
Clop ransomware actors exploited several unpatched vulnerabilities in Accellion’s File Transfer Appliance (FTA) and exfiltrated the data belonging to more than 100 U.S. companies in an effort to directly extort the victims. Many of the impacted entities reported that the Clop group began contacting them via email, threatening to release the stolen data if a payment was not made.
Clop leaked the data of some of the victims from the U.S., Canada, the Netherlands, and Singapore. At the time of the initial discovery, UMB was told by Accellion that its data was not among the exfiltrated information.
However, UMB discovered certain data from the FTA was leaked on the dark web by the Clop group. Officials said they immediately contacted the FBI and contracted with a third-party cybersecurity firm to investigate the full scope of the incident.
Although the investigation is ongoing, UMB has determined that the impacted data varied by individual and could include a range of data, such as names, SSNs, demographic details, birthdates, diagnoses, driver’s license, provider names, health information, and related benefits. UMB is providing the affected individuals identity theft monitoring services.
Florida Blue reports spoofing-related data breach
On June 8, the security team of Florida Blue discovered multiple, unauthorized attempts to log into the Florida online membership portal, which was later determined to be part of a sophisticated cyber-spoofing campaign.
“The excessive number of login failures strongly indicates that the ID and password combinations used during the incident did not come from Florida Blue systems, but rather were compiled from third-party websites where ID and password information were previously compromised,” officials explained.
Upon discovery, the security team blocked the internet addresses used by the attacker to hack the member portal.
Florida Blue’s investigation revealed an attacker leveraged a large database of usernames and passwords available on the internet to impersonate members and gain access to the member portal. The campaign enabled the actor to gain access to some online member accounts. The HHS breach reporting tools shows 30,063 patients were affected by the hack.
The attacker accessed the information stored in the accounts, which included contact information, claims data, payment details, health insurance policy information, and a host of other personal information. It does not appear the attacker exfiltrated the information.
Florida Blue plans to deploy a range of technical controls to improve the security of its web portal. All affected patients will receive two years of free identity theft protection, detection, and resolution services.