From the outset of the Russia-Ukraine war, the global cybersecurity community has debated why we haven’t seen the sort of regular, spectacular cyberattacks that many were predicting.
The possible explanations were numerous. Some have cited the maturity of Ukraine’s cybersecurity. Others have offered reminders that public visibility around such attacks is always poor in the immediate aftermath, particularly in the midst of a war zone, or attempted to tie the lack of observable activity to more general criticisms of Russian military incompetence.
The director of the NSA’s cybersecurity wing has a different view: there’s been a boatload of cyber action between the two countries.
Click here for all the coverage coming out of RSAC.
“Russia is in a hybrid war with Ukraine. No surprise [we’ve seen] a lot of kinetic action, but in addition to that kinetic action, what we’ve seen is an enormous amount of cyber activity,” Rob Joyce said Wednesday while speaking at the RSA Conference in San Francisco. “People’s eyebrows will go up and say ‘well, I thought there was supposed to be a bunch of hacks but we’re still waiting on those hacks.' I would argue there’s a significant amount of activity and if you...look at the timeline, it was a multi-pronged-attack and threats.”
To prove it, Joyce laid out a timeline of attacks carried out by Russia against Ukraine in the months leading up to and through the war, ranging from website defacements and DDoS attacks to the deployment of damaging wiper malware and a major hack of satellite provider Viasat right before the invasion started, something Victor Zhora, deputy head of Ukraine’s State Special Communications Service told reporters caused significant damage to Ukrainian communications infrastructure.
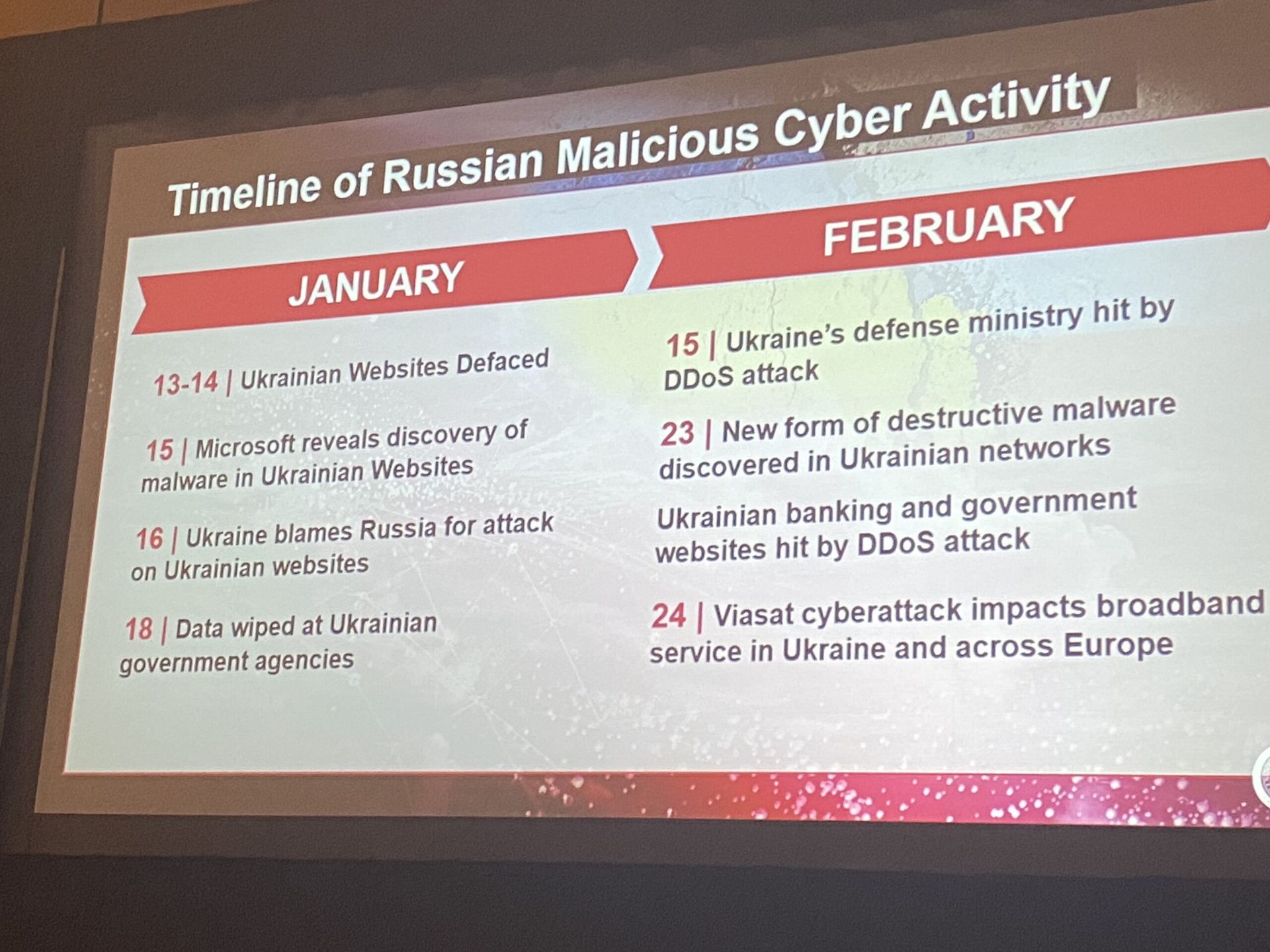
If you go back further, Ukraine’s Security Service suffered a multi-day DDoS attack against its website February 2021, and beat back an effort to hack their classified military systems in March of the same year. Both campaigns were attributed to the Russian government. (Hat tip to the Center for Strategic and International Studies)
Throw in the operations of “vigilante” hacking groups working on behalf of both Ukraine (the IT Army) and Russia (where Joyce and other officials worry ransomware gangs will soon be co-opted for state-directed hacks if they haven’t been already), the level of hacking leading up to and throughout the war has lived up to the billing.
Zhora said recently that his country’s work building up digital resilience in the face of relentless Russian cyberattacks in prior years has positioned them well to beat back many attempted hacks. Joyce largely agreed with that view, saying the excellence of Ukraine’s defensive posture was likely “a contributing factor” to initial impressions that predictions of cyberwar were overblown.
On the prospects of Russia drafting ransomware gangs into the war effort, Joyce said global economic sanctions imposed on Moscow led by the U.S. Treasury Department and European allies have made it harder for these criminal hacking groups to extract ransom payments from victims and purchase command and control infrastructure to carry out their attacks.
“People were asking ‘Well you know, I’m not sure we’re seeing a dip in ransomware, how do you know this; can you show me?' I would just say: how did we know? Really? We’re NSA,” said Joyce, alluding to the agency’s core mission of collecting signals intelligence. “We heard them say they can’t get their money out. We heard them say that they can’t buy infrastructure.”
Those successes are likely temporary, he said, but it does demonstrate that it is possible to make life harder for the criminal gangs that have been extorting and terrorizing businesses and governments from the safety of Russia.
“Like all of us, they will adapt, they’ll find new ways and we are seeing an uptick in some areas as they solve these problems, but it does show that there are levers that can be applied to this problem,” he said.




