In recent weeks, the U.S. student loan market has been in the spotlight — not just for the much-discussed loan forgiveness plan launched by the Biden administration, but also for the segment’s growing position as a target for financial fraud.
Indeed, just two weeks ago, it was reported widely that more than 2.5 million student loan borrowers were the victims of a massive data breach that affected both EdFinancial and Oklahoma Student Loan Authority accounts. As with many recent financial institution breaches, this particular attack emanated initially from Nelnet Servicing, a large technology services vendor to student lenders. Unknown bad actors may have gained access to a wide range of account-holder information, including names, home and email addresses, phone numbers and Social Security numbers during June and July of this year. (Nelnet has insisted that financial account information was not compromised in this attack.)
As with the recent KeyBank mortgage account breach, news of the massive compromise of student loan accounts was met with relatively swift legal action. Last Wednesday, a class-action lawsuit citing “breach of contract” was filed in the Nebraska district court against Nelnet Servicing, which is based in that state. The plaintiffs were student loan borrowers who said they were impacted by the incident. Similar to the KeyBank breach and subsequent legal action, the suit has honed in on the apparent delay of more than one month between the third-party service provider (in this case, Nelnet Servicing) finding the unauthorized access and notifying the student lenders that their borrower-customers might be affected.
“When an organization discovers a vulnerability for specific accounts or data, it is most likely related to infrastructure or systems that were misconfigured or not fully patched,” said James McQuiggan, security awareness advocate at KnowBe4. “Cybercriminals search for those weaknesses and attack the systems to gain access quickly. When patches and updates are available for critical systems, it is crucial that organizations quickly remediate the risk or patch the system.”
Opportunistic scams emerge after newsworthy events
However, various issues can challenge the risk reduction and patch process — among one of the most significant is the pressure to respond to regulatory or market requirements. And here is where the student loan industry and its third-party vendors are likely to face new challenges.
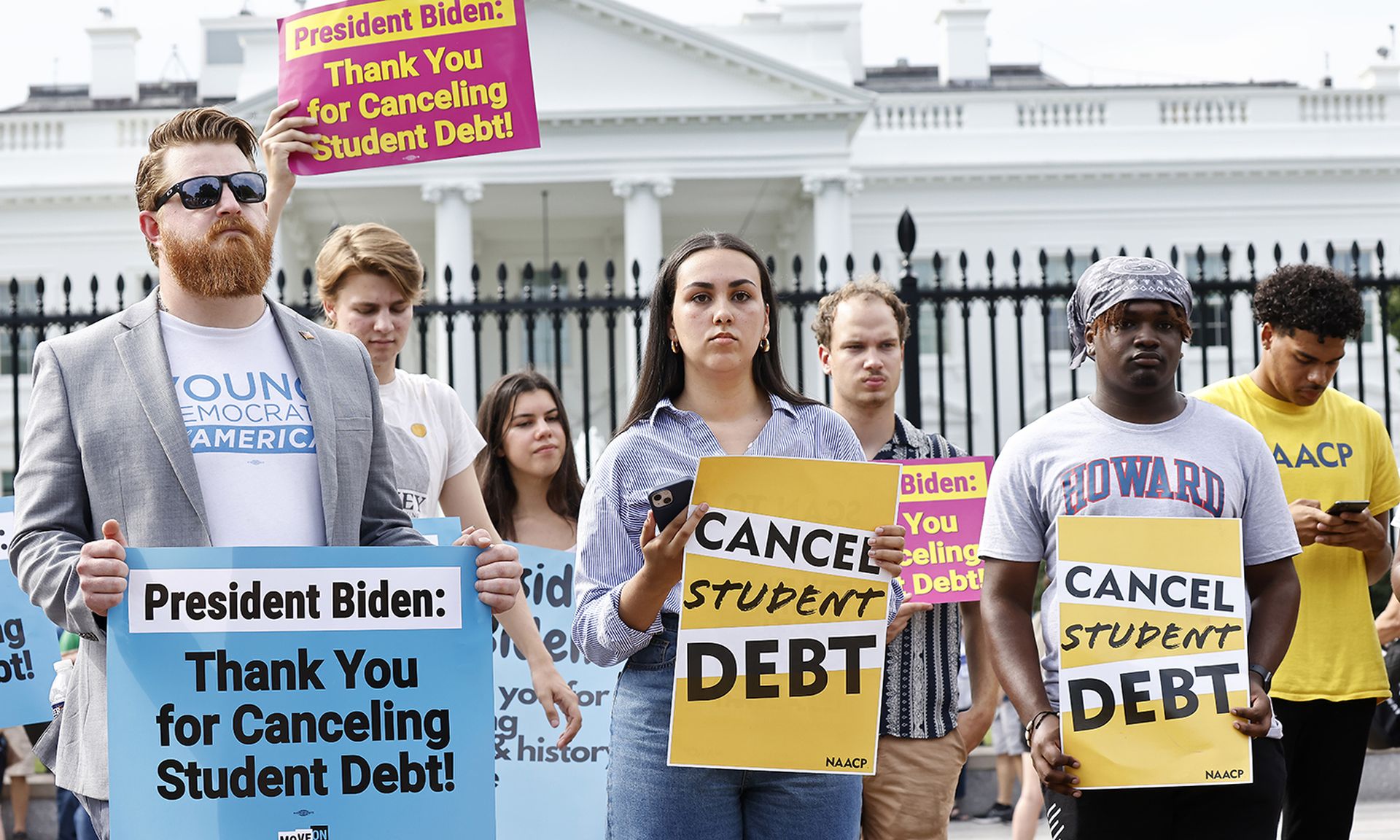
The recent (and some would say, controversial) new student loan forgiveness program has catapulted this segment of the U.S. financial services market front and center, creating confusion for some borrowers and pressure for lenders and hence, new opportunities for shrewd cybercriminals who realize this may have created a near-perfect environment for them to slip into systems and cash in on old and new streams of funds flowing back and forth between borrowers, lenders, the government and other parties.
When significant and newsworthy events occur, in this case the student loan forgiveness, “certain kinds of opportunists almost always show up to build scams to capitalize on the attention,” according to Tim Helming, cybersecurity evangelist with DomainTools.
“A lot of these scams will involve phishing, and one of the key ways to avoid getting caught by a phishing attack is to be aware of look-alike domains and websites,” Helming added. “Threat actors are good at creating domain names that can fool a lot of users by looking very similar to legitimate domains.”
On Sept. 14, the Department of Education announced that as many as 9 million student loan borrowers who made at least one debt payment during the pandemic (between April 2020 and March of this year) are due for a refund. That wrinkle alone — while a financial benefit to student borrowers — could create a substantial opening for wily cybercriminals to more easily ply their trade here with related phishing emails and social engineering scams, or stealthy ransomware or other types of malware exploits, which leverage these huge shifts in the student loan market.
Helming pointed out that while “ransomware makes news, the losses from phishing are still considerably higher, according to the FBI ... It’s important to keep vigilant about phishing and its 'cousins' such as smishing [text-based phishing].”



