Mobile device management is a crucial component of maintaining a stable security posture, but mobile device management and unified endpoint management tools, one of the more difficult areas of cybersecurity is one of the most difficult areas of cybersecurity. The everchanging and growing threat landscape makes security difficult enough, while the lack of control surrounding mobile devices poses an additional challenge for security teams and administrators.
Mobile devices come in various shapes in sizes with equally varying operating systems, further complicating administrator management. For example, most OS allow for remote control capabilities, while Apple only permits remote view.
The most effective way to manage mobile devices and keep networks secure, while avoiding productivity impediments, is to implement an MDM-UEM solution.
The solutions not only help ensure security and meet compliance requirements, but in some cases, they may increase productivity with roles-based access and automation capabilities. These tools help administrators maintain their workloads and let end-users freely use their devices while keeping corporate data within the network secure.
The products we tested this month successfully balance productivity with compliance and security by leveraging functionalities such as geo-fencing and remote view and control. Once one of these solutions has been deployed into your environment, end-users will be able to use their devices without introducing unnecessary risk into your environment.
Mobile device management and unified endpoint management
The main lesson we learned from the mobile device management and unified endpoint management (MDM UEM) tools we reviewed is that mobile device management is a crucial component of maintaining a stable security posture. Everchanging and growing threat landscapes make security difficult enough but being unable to control surrounding mobile devices poses an additional challenge for security teams and administrators.
A properly configured mobile device/endpoint management tool will not only help ensure security and meet compliance requirements, but in some cases, it may also increase productivity through roles-based access and automation capabilities that minimize manual overhead. The tools we reviewed assist with MDM-UEM, allowing administrators and employees to use their devices freely and safely, but still maintain the security of corporate data.
There are many items to consider when it comes to managing mobile devices and unified endpoints, including installing applications, geo-tracking and geo-fencing. Securing devices is, quite literally, like trying to secure and manage a moving target. End users obviously transport their devices from home to work, sometimes traveling a considerable distance and administrators can’t control the networks to which the devices connect. Therefore, it is crucial to protect data with encryption and containerization.
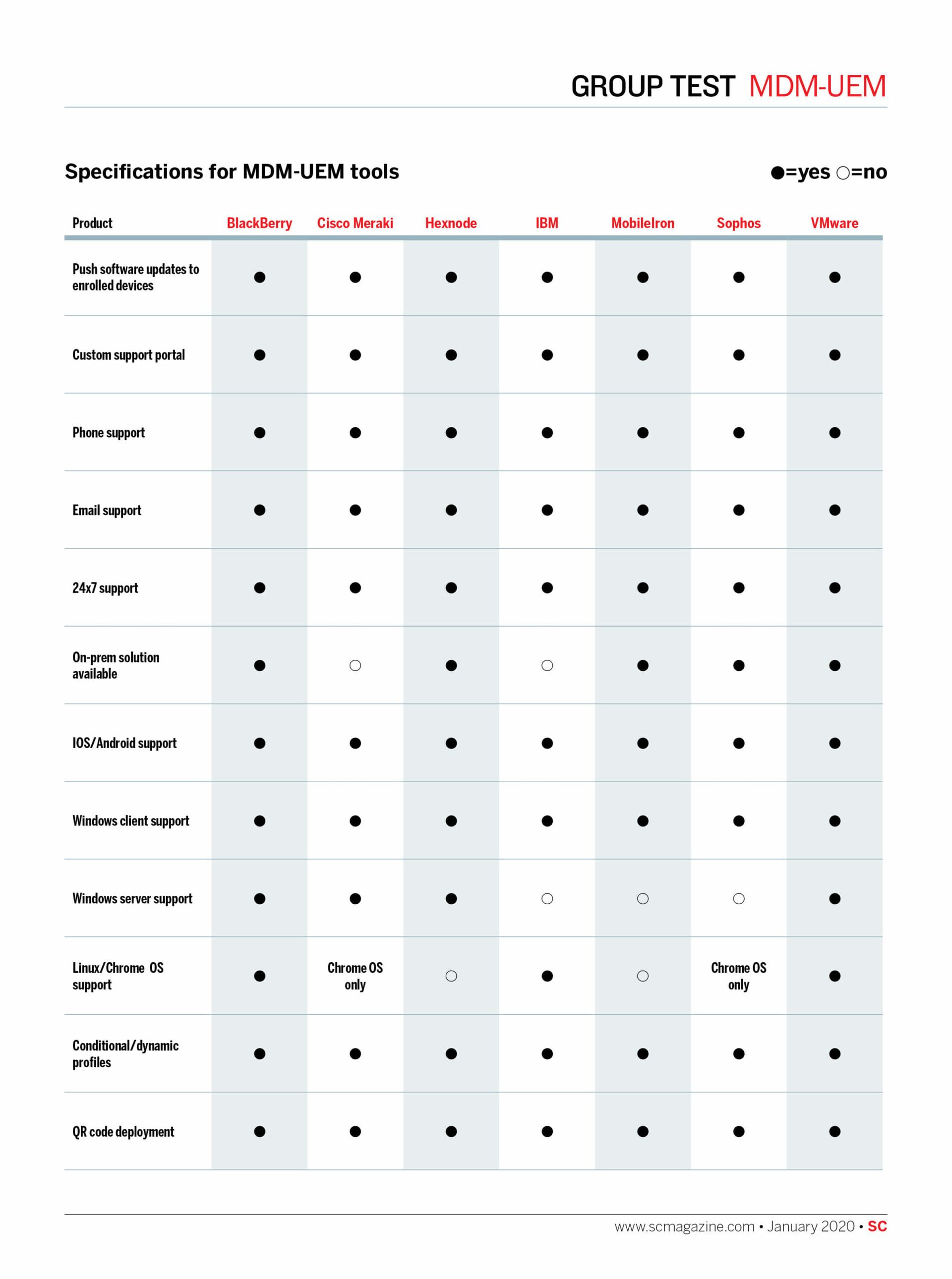
Device management is further complicated by the variety of operating systems. And administrators must control corporate-owned devices to protect them when lost or stolen. The proliferation of IoT and mobile devices in the workplace has birthed an information security niche that the MDM-UEM solutions we tested this month all seek to address.
Overall, tools have adapted well to the increase in the number of workplace mobile devices. End users need to be able to complete work tasks securely, but that security should never impede productivity. Administrators must be able to manage corporate-owned devices and containerize personal devices to ensure that these devices never threaten corporate data. The following MDM-UEM solutions successfully balance productivity with security. In some cases, they even enhance the productivity of both administrators and end-users with features like roles-based access, automation, artificial intelligence and geo-tracking.
Pick of the Litter
VMWare offers several unique features such as: Intelligent hub; role-based access, sandboxing and more. This robust feature-set, overall product performance and free 24/7 support combined in one very competitively priced solution makes VMWare Workspace ONE an SC Labs Best Buy.
The incorporation of Watson, a question-and-answer system backed by machine learning technology, and the vastness of features and configuration options offered makes MaaS360 with Watson our SC Labs Recommended product for this month’s round of reviews.
Check out all the reviews below:
BlackBerry Unified Endpoint Management Q-Series
Hexnode 8.2
IBM MaaS360 with Watson 10.74
Meraki Systems Manager SaaS
MobileIron UEM R64
Sophos Mobile 9.0
VMWare Workspace ONE UEM 1907