Ransomware has long been among the most significant threats to the modern enterprise. First with encrypting data and extorting a fee for the key – where the term “ransomware” comes from – to now double and triple extortions becoming increasingly common. These changes have driven the rise in ransom demands to an average of over $800,000 according to Sophos data and contributed to the more than 1,100 attacks that LookingGlass tracked in the first half of 2022.
Most concerning in this current environment, however, is that ransomware gangs themselves are becoming more professional. You need look no further than the Conti Leaks from February 2022. Following the invasion of Ukraine by Russia, the Conti ransomware gang declared its support for the Russian government and threatened that they would target anyone who entered the conflict on Ukraine’s side.
By itself this declaration of support was unique. Most ransomware gangs avoid aligning themselves too explicitly with national governments. The exception of course being North Korea, where ransomware activity tends to be leveraged to fund the regime. The Conti Leaks wasn’t only interesting because of what precipitated the event, but rather also for the window it gave into the structure of a leading ransomware group.
The New Professional Ransomware Gang
The media perception of ransomware groups is often one of a lone wolf hacker creating software that encrypts data and forces payment to provide the encryption key. The reality that Conti Leaks shared shows how far from the truth that perception is.
The Twitter account, aptly named ContiLeaks, showed that Conti had the kind of infrastructure you expect from a traditional business. When Cyberint analyzed the leaks (after the translation from Russian), they created the below chart to showcase the presumed organization of Conti’s operations. This is the kind of flowchart you’d expect from a legitimate business offering software of any kind to the business community or consumers. Except obviously for finance having a team focused on money laundering but ignore that part in the analogy.
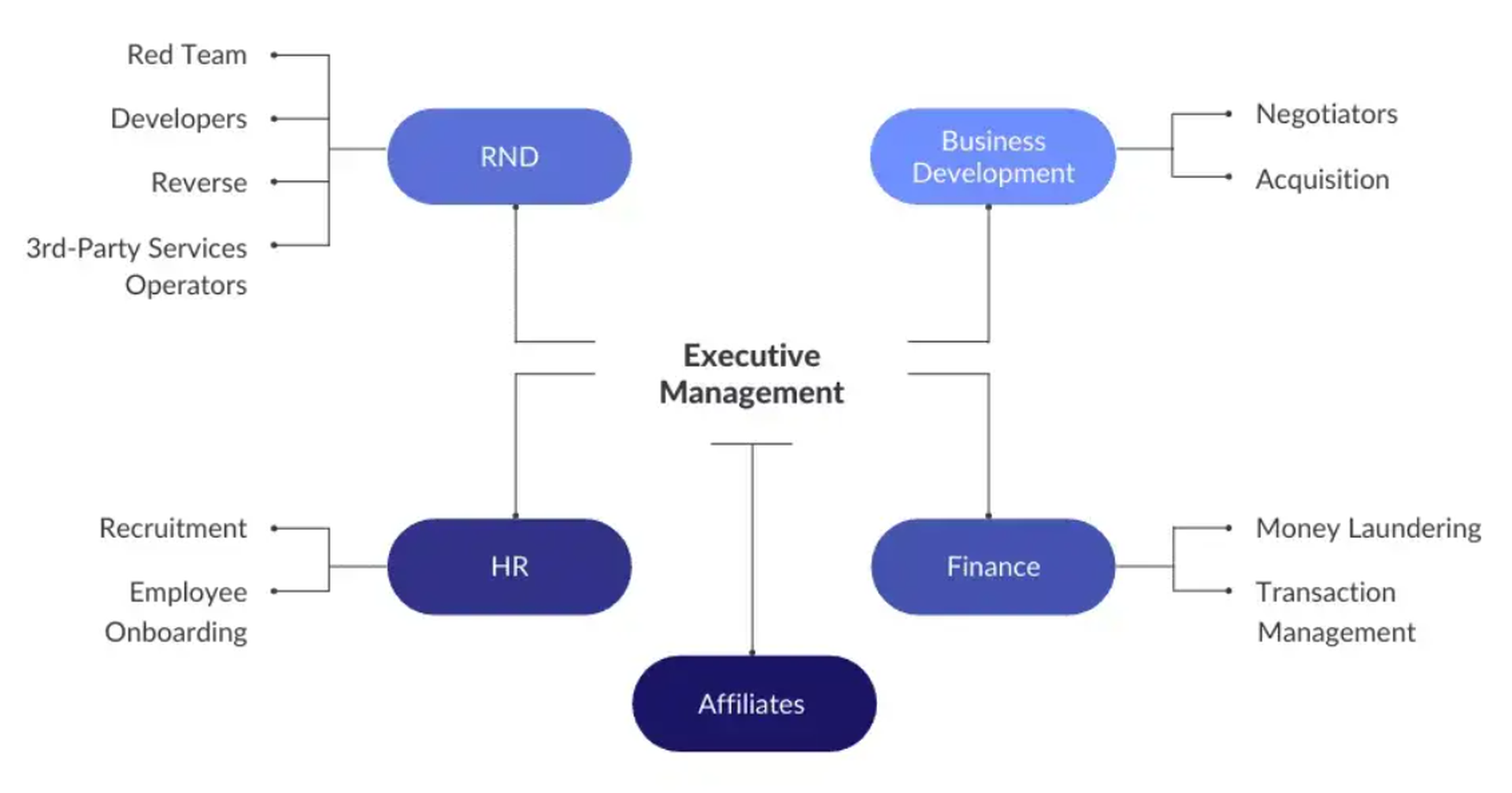
Conti’s organizational structure is a far cry from the loosely affiliated ransomware groups of the past. It’s also indicative of the growing professionalization among financially motivated ransomware gangs. Gone are the days of lone wolf ransomware creators who leveraged automated generic targeting to potentially breach an organization. Today’s ransomware gangs are business ventures with salaried employees and quarterly revenue goals; precisely the same metrics that a legitimate company is concerned with.
In addition to serving their customers, ransomware organizations want to make profit, just like any other business. Ransomware enterprises have been known to set up payment plans and other arrangements to ensure the ransom is paid. They also want to ensure and convince victims that paying up is their best option in the first place. They even have bug bounty programs to point out errors in their code; Lockbit launched the first one in June 2022 and paid out a bounty of $50,000 to a researcher in September.
Ransomware-as-a-Service: The SaaS of the Criminal Underground
Ransomware as-a-Service (RaaS) has also emerged as a common tactic for cybercriminals. RaaS has allows nearly anyone with basic technical skills to become a ransomware threat actor. In the past, it was considered challenging for criminals to develop their own ransomware programs because the tools were complex and expensive. Nowadays, RaaS allows almost anyone to run their own cybercrime operation, easier and more accessible than ever before.
The RaaS model has been around for years. But recently, it has grown significantly due to increased customer and vendor demand. The customer base typically purchasing RaaS products consists of those looking for “off-the-shelf” malware that can be used in their attacks. These purchases also provide vendors access to readymade tools that allow these customers to instantly launch attacks without having diverse technical skills or knowledge about cryptography or cybersecurity best practices.
Since its initial known launch in 2016, RaaS has grown into a highly lucrative business model and expanded to include a wide range of malicious tools—including banking Trojans, spyware, and crypto miners. The most popular RaaS platforms are advertised on dark web forums and have thousands of registered users who pay monthly subscription fees in exchange for access to their toolkits. These services offer several benefits to would-be attackers such as:
- Establishing a framework to launch attacks
- Benefiting from other users testing and improving tooling code
- Leveraging others’ servers to avoid the need to build new infrastructure.
Money is paid through the affiliate model, with ransomware creators taking a percentage of the revenue that their licensees make. This approach is like how SaaS companies use channel partners to resell their software. It’s not surprising that ransomware operators would take this approach, given that it allows them to capture more revenue with less work.
Expect Ransomware’s Professionalization to Continue
Gone are the days of the lone wolf cybercriminal or loosely affiliated groups with high barriers to entry. Ransomware is big business. Groups like Lockbit and Conti (before they disbanded) regularly have revenue numbers in the hundreds of millions between their affiliates and direct attacks perpetrated by the company. Ultimately, this professionalization of ransomware as an attack vector is likely to continue and even accelerate. Welcome to the new world of the professional ransomware gang.
By Matthew Delman





