Legacy IT has become the dirty little secret of digital transformation. These systems, which include servers, OSes, and applications, are relied on by almost every organization for business-critical activities – and many CISOs struggle to protect them from attackers.
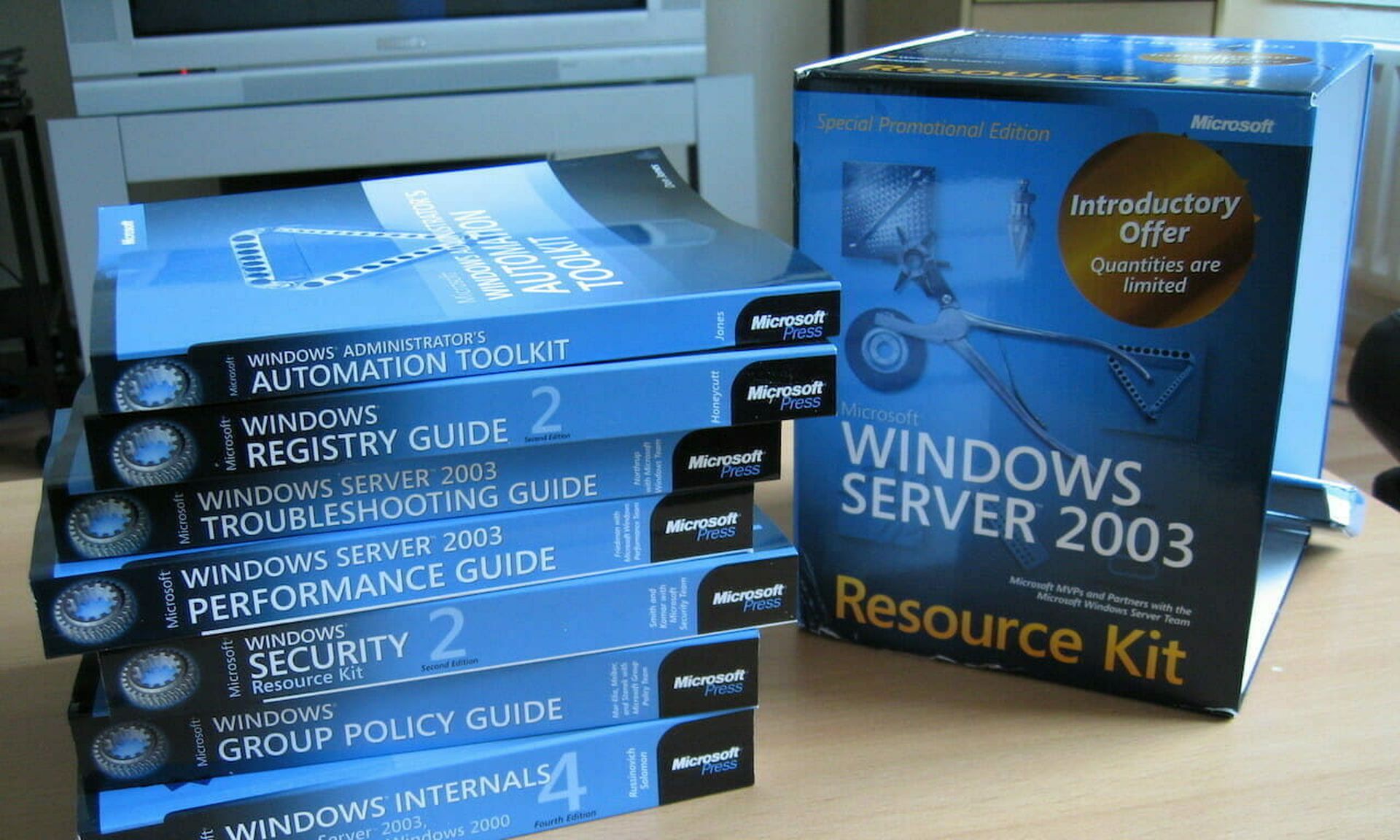
During my time as CISO for a public company, I got a first-hand look at the depth of the legacy challenge. We had more than 1,000 servers in use that were built in 2003 but no longer supported by vendors, and more than 200 legacy servers were designated for business-critical activity that drove significant annual revenue. It’s a non-starter to take these servers offline, and protecting them comes at a significant cost.
The cost and complexity of protecting legacy systems
The complexity of the legacy system lies in the IT team’s inability to update and maintain them. Many of these systems and apps have been used for multiple years and may have millions of lines of code written in them. Changing or altering the code could impact one of the revenue-generating applications that keeps the business running.
On top of this, legacy systems are near impossible to patch. This makes them incredibly vulnerable and a target for attack. So how can organizations protect the systems that serve as the core of their business?
Legacy security can’t protect legacy systems
Companies have to absorb the cost of protecting legacy systems within current cybersecurity spending. As such, organizations try to retrofit existing solutions like firewalls and endpoint protection.
Digital transformation has made this approach obsolete. Modern infrastructure, data centers, and the move to hybrid clouds give attackers more pathways to target these vulnerable systems.
Legacy systems that were once used by a handful of on-premise applications can now get used by hundreds of applications both on-prem and in the cloud. Containers may even interact with the mainframe. These are connections that firewalls were simply not built to secure. Many firewalls are also legacy devices and don’t integrate with modern applications and environments. Using them to secure legacy systems against outside intrusion simply increases the total cost of ownership without actually securing the systems against modern threats.
CISOs require a convergence of security approaches that protect legacy assets, while also minimizing threats across modern assets. The approach we evaluated and trusted was based on the core principles of Zero Trust.
Improve legacy systems with Zero Trust
Establishing Zero Trust around legacy systems and applications requires four critical components: visibility of legacy assets, micro-segmentation, identity management and continuous monitoring.
- Identify legacy assets.
Companies find it challenging to obtain the proper view of existing legacy assets, but it’s vital to ensuring the security of the organization. It’s not enough to secure “most” assets – it only takes one overlooked server that attackers find to breach the organization.
After an acquisition the first step we took was to create a full view of the entire ecosystem and map everything from legacy systems to cloud environments, containers, and applications. By understanding which workloads present the most risk, we could deduce the prime starting points for enforcing Zero Trust.
It’s a recipe for inconsistent policy and blind spots to start on the path to Zero Trust with anything less than a holistic view of the entire network. Taking a holistic view empowers the security teams to identify the critical areas to start the second step: implementing micro-segmentation.
- Segment everything.
While firewalls have been the traditional choice for segmenting assets from networks, they’re not built to protect legacy and unpatched assets at such a granular level. Older techniques such as firewalls and VLANs are costly to own and maintain, and they frequently place similar legacy systems in a single silo. For an attacker, it’s like shooting fish in a barrel – a single intrusion can lead to multiple critical systems being exploited.
In addition, security and operations teams need to constantly update rules and policies between the firewalls and the applications and assets they’re supposed to protect. This leads to overly permissive policies that may improve workflow, but significantly undermines the security posture the organization will try to build.
We used micro-segmentation technology Guardicore Centra, which let us build tight, granular security policies to prevent lateral movement. In addition, security teams can deploy micro-segmentation across the entire infrastructure and workloads of all types, including data centers, cloud and modern applications. This eliminates high-risk gaps in the security across infrastructure.
- Leverage identity management.
It’s very important to enhance the organization’s identity and access management platform. Proper user identity management plays a critical role in the Zero Trust principle. Users need access to systems and applications. Security teams must grant access based on each individual user’s role and automate to verify before granting access to minimize the operational burden and enable to scale.
- Trust no one without verifying.
Micro-segmentation technology offers deep visualization capabilities that make policy management easier and provide capabilities to manage segmentation based on application usage. Applying micro-segmentation across production infrastructure helps to minimize the risks with proper visualization of modern and legacy workloads. This enables the enforcement of server-level policy, which allows only specific workflows between legacy systems and between modern environments and applications to and from the legacy systems.
Legacy systems and applications continue to present a tough challenge for organizations. They’re business critical, but incredibly hard to maintain and properly secure. As organizations embark on digital transformation and introduce hybrid cloud, new applications and data centers, the problem becomes exacerbated.
Securing the business starts with securing the critical assets that make the business run. Visibility of the infrastructure, combined with micro-segmentation and continuous monitoring, controls the risk of legacy systems by building tight segmentation policy that attackers can’t exploit. And don’t neglect enforcing the basic security hygiene across enterprise.
Hemanta Swain, senior independent consultant, former chief information security officer, TiVo