

Not since the Beatles has a Top 10 chart been dominated like this. According to Cofense Intelligence, the subject “Invoice” appears in 6 of the 10 most effective phishing campaigns in 2018. Not only that, “Customer Invoice” snags the #7 spot. The other 3 winners also pose as financial transactions: “Payment Remittance”, “Statement”, and “Payment”.
It’s a powerful reminder that hackers stick with techniques that work – and that organizations should focus their defenses on threats they actually face, instead of asking employees to become experts on everything. Employees in finance and accounting should train repeatedly for these scams, plus anyone else authorized to spend the company’s money.
In any business, invoices are as common as email itself. People receiving them have access to the information hackers want. If infected, financial employees’ machines are potential goldmines. No wonder “Invoice” is the lure de jour.
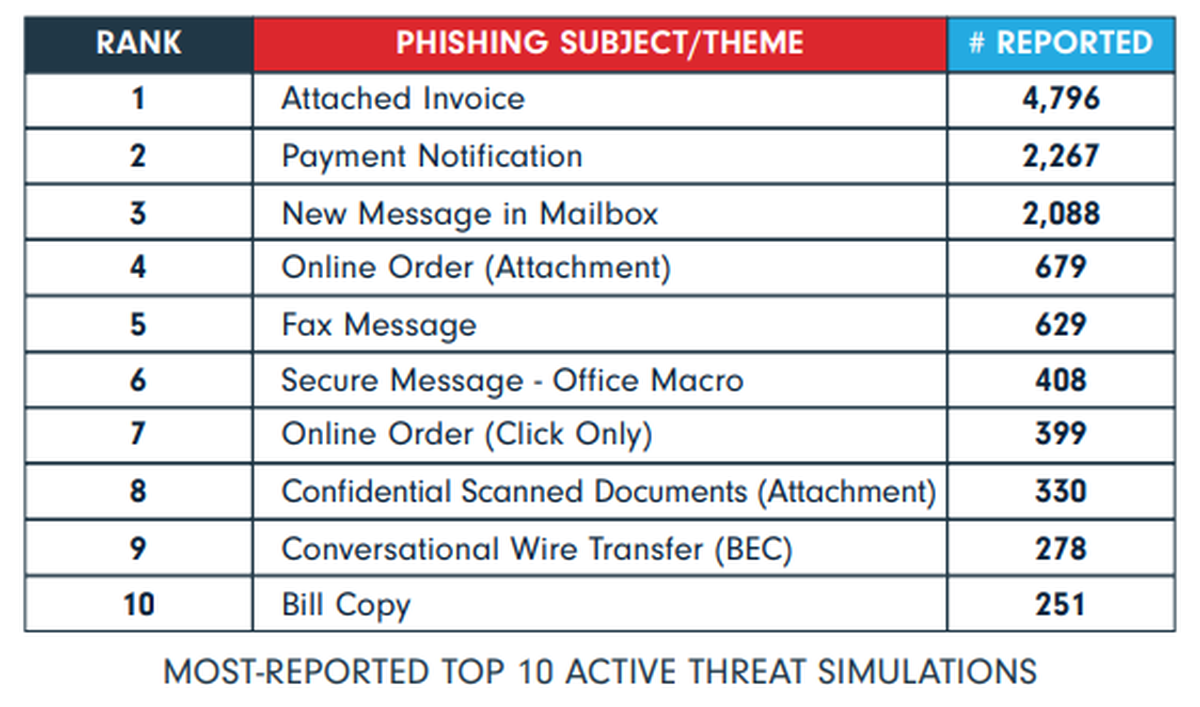
It’s not even close. By more than 2 to 1, “Attached Invoice” is the active threat users report most often. Two other attachment-based threats made this Top 10, “Online Order” at #4 and “Confidential Scanned Documents” at #8.
Organizations need to train users to view attachments suspiciously, especially invoices, online orders, and anything with macros. Also, it’s not a bad idea to send a gentle reminder: even though online shopping and BYOD are facts of life, users should be careful before opening messages from Internet retailers, even favorite brands.
Another tip: be mindful of the financial calendar. End of month, end of quarter, and end of year are ripe for phishing attacks disguised as financial messages. When it’s heads-down processing time, give employees a heads-up.
Many of the most-reported emails have to do with money, something to drive home in security training. If you’re unsure of the active threats your organization faces, this list is a good place to start when launching an awareness program.
For more information about the state of phishing defense, see the full whitepaper from Cofense here.
By: Cofense




