In the wake of the Stuxnet worm, lawmakers are considering whether the Department of Homeland Security should have increased authority to protect the nation's critical infrastructure and whether private sector organizations should be required to report attacks.
During a U.S. Senate Homeland Security and Governmental Affairs Committee hearing this week, Chairman Joe Lieberman, I-Conn., asked representatives from industry and government whether they believe the security of the nation's critical infrastructure can be increased through voluntary measures alone or whether the DHS should be granted enhanced authority.
Michael Assante, former CSO of the North American Electric Reliability Corp. (NERC), said he believes that bestowing the DHS with additional authority is “necessary.”
Doing so would allow the agency to better protect critical infrastructure systems and effectively gather the resources within government and industry to deal with cyberthreats, he said. Moreover, Assante said he is in favor of mandating that private sector organizations report attacks.
“It's critical that organizations can't suffer in silence,” Assante said. “If an advanced threat is on our shores, impacting our systems, that should be required thing to report.”
However, Mark Gandy, global manager of IT security and information asset management at Dow Corning, a provider of silicon technology for the chemical industry, said he believes companies are already working productively on their own to address threats.
The Stuxnet worm is the first known threat to target industrial control systems and grant attackers control over critical infrastructures, such as power plants and chemical facilities, said Dean Turner, a Symantec Security Response director.
“Stuxnet has highlighted that direct attacks to control critical infrastructure are possible and not necessarily spy novel fictions,” Truner said. “The real-world implications of Stuxnet are beyond any threat we have seen in the past.”
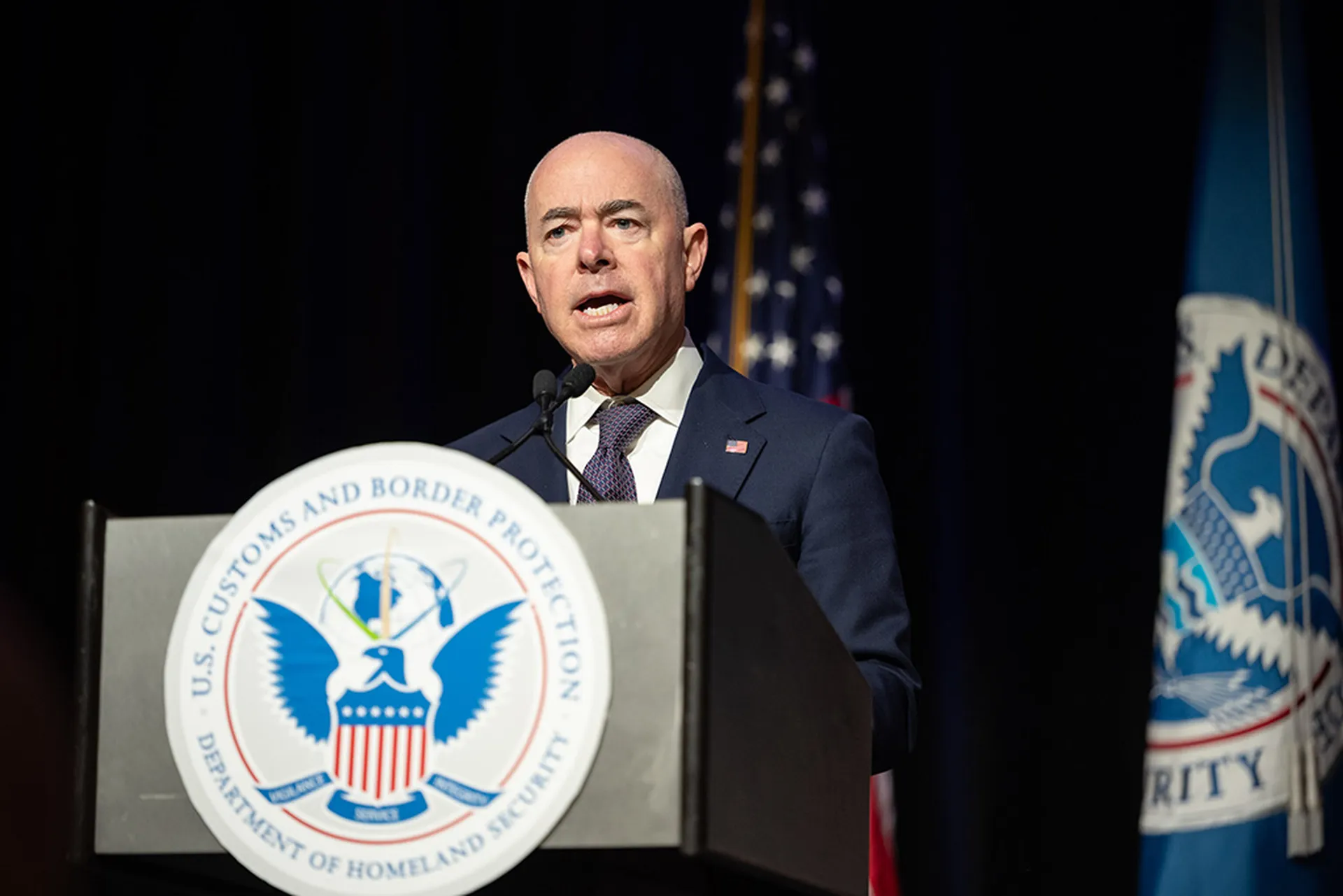
Sean McGurk, acting director of the National Cybersecurity and Communications Integration Center of the DHS, said his agency would not oppose additional authority but also is not asking for it.
The DHS is working to assist private-sector critical infrastructure companies with cybersecurity training, risk management and incident response capabilities, he said. However, organizations may choose to ignore these resources.
“We only respond when requested from the private sector,” McGurk said.