
While encryption will deter data breaches, it comes with its own baggage — and keys
It is not a question of if the bad actors will access confidential or highly classified data, rather it is a question of can attackers read and use confidential and classified data after they access it. Many experts believe the assumption that attackers eventually will get inside your network and reach private data, but whether they can exfiltrate data or even read it is quite another question.
Data encryption for years has been the go-to security technology to protect the most sensitive data in an organization because it is so effective at stopping cybercriminals from exploiting information assets.
With so much data moving to and from the cloud, a growing number of increasingly sophisticated threats, and new data privacy regulations taking hold, encryption can be found virtually everywhere at many organizations. Today, encryption still holds an honored position as an essential security technology, but as with all such technologies, it is only a matter of time before it becomes as obsolete as the password.
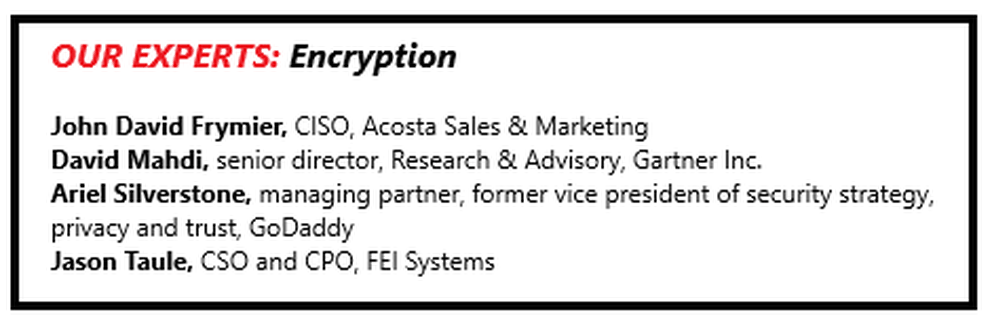
“Encryption has generally been viewed as a foundational technology for protecting sensitive data,” says David Mahdi, senior director, research and advisory, at Gartner Inc. “As such, many industry experts recommend encryption and other data protection technologies to ensure that risk and regulations are accounted for.”
A key question for IT and security executives as they look to bolster defenses with more encryption tools: What impact is the encryption technology having on systems performance and user experience and productivity?
This is not a trivial question. For years, business executives have wondered whether cybersecurity tools would slow down the performance of vital systems and end users have complained about the intrusiveness of these tools as they try to get their work done.

With encryption, companies ideally want to use the technology on data while it is at rest, in transit, and in memory. But with so much encryption technology in place, there is the potential for it to backfire because of the unintended consequences.
So far, security executives and industry experts say, that has not been the case because the technology has advanced over the years. But that is not to say the encryption everywhere approach is devoid of challenges. Perhaps the most common challenge is the management of keys, which can grow more complex as companies use encryption more broadly.
Building an encrypted infrastructure
“We use encryption pretty much wherever we can because of its ‘get out of jail’ benefit,” says Jason Taule, chief security officer and chief privacy officer at FEI Systems, a company that provides healthcare information services for federal, state, and local governments.
“It basically allows us to make the case that the data was not exposed to risk of harm,” Taule says.
Specifically, FEI Systems uses Transport Layer Security (TLS), a cryptographic protocol designed to provide data privacy and integrity over networks, wherever possible. That includes email exchanges, all data at rest, and as an I/O function of its storage network.
All endpoint devices are whole-disk encrypted, and the company uses BitLocker, a full-volume encryption feature included with Microsoft Windows, to encrypt all removable media devices such as USB drives before any data can be written to these devices.
As a government contractor operating in the healthcare IT industry and subject to many regulations including the Federal Information Security Management Act (FISMA) and the Health Insurance Portability and Accountability Act (HIPAA), FEI Systems has been obligated to implement encryption controls since its inception, Taule says.
Acosta Sales and Marketing Co., a full-service sales, marketing and services business, uses encryption everywhere except in legacy applications, according to John David Frymier, Acosta’s CISO.
That includes in the companies network-attached storage (NAS) and storagearea network (SAN) systems, as well as in all data center servers. In addition, the mobile device management (MDM) platform Acosta uses encrypts all the contents of mobile devices, and the company uses BitLocker whole-disk encryption on its PCs.
The company’s web sites and its remote access system use SSL (Secure Socket Layer) to encrypt communications. “Everything going to and from and stored with our cloud service providers is encrypted,” Frymier says.
Acosta has steadily increased its use of encryption over the past 10 or so years, ue to a combination of contributing factors.
Privacy laws
One of the biggest factors, as with FEI Systems, is the increase in data privacy laws. For example, data privacy legislation passed in Massachusetts in 2009, 201 CMR 17.00, made mandatory the encryption of in-storage personal data about state residents.
The company also needed to comply with industry-specific security regulations such as Graham-Leach-Bliley Act (also known as the Financial Modernization Act of 1999) and HIPAA, as well as contractual requirements such as the Payment Card Industry Data Security Standard (PCI DSS) rules. These laws and regulations have not only driven adoption of encryption within organizations, but encouraged hardware and software vendors to embed encryption in their products, Frymier says.

Another factor in the rise of encryption use was the implementation of encryption algorithms in chips, which made it more cost effective to use encryption and removed much of the performance impact, Frymier says.
Acosta’s use of encryption is not having any ill effects on systems performance or user experience, Frymier says. “It used to, but these days with hardware support, generally faster CPUs, and networks all around, the performance impact is not human noticeable,” he notes. “From an end-user perspective, most of them don’t even realize it’s there.”
More and more organizations are relying on a zero trust model in which the “encrypt everything” approach is used to verify identities, provision entitlements to services, and protect data stored in and moving to and from the cloud, says Ariel Silverstone, managing partner and former vice president of security strategy, privacy and trust at GoDaddy, an Internet domain registrar and web-hosting company. Silverstone is also a member of the SC Media Editorial Advisory Board.
Regulations, especially those that address data breaches, make the use of encryption a “no-brainer,” Silverstone says. “Often that is the only option above liability when an organization is breached,” he says.
Go Daddy increased its use of encryption throughout the organization, especially for the transmission of sensitive and personal data, but also to “pre-expire” datasets. “We do that so on a specific date the data stored will become irretrievable,” and therefore no longer subject to data protection requirements of regulations such as the European Union’s General Data Protection Regulation (GDPR) and other laws, Silverstone says.

former vice president of security strategy,
privacy and trust, GoDaddy
The technology is nothing like it was years ago in terms of affecting system performance, Silverstone says. “About 30 years ago, when I designed client systems, encryption used to have up to 75 percent cost of CPU and of memory time,” he says. “Nowadays, we are approaching 0.5 percent and thus, not material.”
Dealing with challenges
User experience is not really effected by encryption either, Silverstone says. Encryption, and in particular digital certificates, “remain one of the only technologies out there which allow truly massive deployment, authentication, and authorization resources,” he says. While the growing use of encryption might not be having an adverse impact on system performance or worker productivity, it is not without challenges. One of the biggest is managing keys.
“I don’t mean to trivialize the algorithmic side of cryptology, but at the end of the day it’s just a repetitive dance with a bunch of bits,” Frymier says. What is operationally difficult about encryption is managing the keys, he says.
Consider this scenario: A company has an encrypted database sitting on an encrypted SAN, which is backed up by an encrypted archive system. If this database contains financial information that is used to file tax returns, for example, the company needs to hang onto it for seven years.

Acosta Sales & Marketing
“That’s three sets of keys and three different management systems you have to keep straight for that period of time,” Frymier says. The company also needs to keep the keys secure. And while commercially available encryption has made general adoption much easier, each vendor has its own key management system.
“So people have to be trained, well trained, in how to do that,” Frymier says. “Otherwise, you can lose control of your own data.”
Key generation and use also need to be non-trivial. For instance, if a company’s web presence involves hundreds of internet-facing servers performing a variety of tasks, it might seem operationally efficient for them to all have the same SSL key.
“However, if one of those servers gets compromised and the private key exposed, the traffic to all the rest could be in jeopardy,” Frymier says. Each organization needs to find its happy medium in key management, which balances the risk of compromise against the cost of operations.
FEI Systems also has found key management to be a hurdle, including the creation, maintenance, and recovery of keys, as well as password and key communication for encrypted attachments.
For instance, to decrypt an encrypted disk when a user leaves the company or if a password/key is lost, FEI needs to create and store a recovery key. Backup compatibility is another issue. Backups of data that is already encrypted at rest requires backups of keys, Taule says. This is more complex than backing up unencrypted data and then encrypting it with the backup software, he says.
Then there is also the challenge of managing keys for cloud encryption, which some vendors do not provide.
To address these issues, the company relies on centralized key administration and is increasingly leveraging the encryption capabilities of the underlying operating systems it uses, Taule says.
Another challenge is that encryption can affect different applications, such as databases, in different ways.
“The affect varies based on the nature, platform, architecture, and design of the application, which is why whenever possible we seek to implement encryption in the underlying infrastructure rather than solely within the application/ database,” Taule says.

Research & Advisory, Gartner Inc.
In a database, encrypting the entire platform is substantially different than encrypting certain cells, Silverstone adds. “Similar differences occur with other use cases,” he says. “Encryption used properly is a useful tool. Used improperly, it can present enormous costs and even prevent a system from operating.”
Some applications cannot handle encrypted data, since encryption changes the format of the data, Mahdi says. For example, credit cards use mostly numbers, and the process of encryption turns the data into long strings of text. In many cases, applications that rely on this data, such as databases and customer resource management (CRM), cannot store the encrypted data.
Furthermore, data cannot be encrypted at all times, which leaves it exposed. When organizations want to analyze their sensitive data, they have to unencrypt it, Mahdi says. As a result, the data is exposed for the duration of the analysis.
“This can problematic, as in today’s environment a number of analytic and business intelligence tools are spread across a number of silos,” including cloud services, Mahdi says. The time spent encrypting and unencrypting can add a lot of processing time, and potentially unintended exposure of data.
Organizations can help address this by deploying a layered security approach using a number of security tools such as encryption key management products that offer lifecycle management of the encryption keys; data access governance products that bring a layer of management down to the data itself by allowing security leaders to build policies around unstructured files and folders; and identity and access management software that manage the accounts and access of users.
A Growing Market
One question certainly on the minds of security executives is how well current encryption technology will deal with emerging security threats and those forms of attack that still lurk in the imagination of cybercriminals but have yet to become a reality.
To be sure, there is still plenty of demand for encryption technologies and likely will be for years to come.
Gartner has seen an uptick in inquiries from organizations about encryption, including where and when it should be applied. “In fact, we are starting to hear more clients use the term ‘data-centric security,’” Mahdi says.
The firm’s research identifies a number of factors that are creating a groundswell of activity in the market, he continues. One of these is ongoing migrations to cloud computing services.
“Clients are now moving to the cloud much more aggressively” to ensure business agility, among a variety of other reasons, Mahdi says.
Another big driver, as cited by the organizations using encryption broadly, are data privacy regulations. In particular, GDPR continues to cause many organizations to re-evaluate their stance on data security and whether they need to encrypt more data.
“Larger regulations, such as GDPR, have had a substantial impact on the behavior of not only organizations, but also service providers and vendors,” Mahdi says.
While GDPR is focused on the European Union (EU) citizens and companies outside of Europe that handle the personal information of EU citizens, a lot of vendors and service providers recognize that the EU is a large market. “As such, many have or are in the process of adjusting their product roadmaps to account for data and privacy protection technologies and techniques that allow them to adhere to GDPR,” Mahdi says.
The reality is that GDPR will have a global impact and will influence other countries and jurisdictions with respect to data and privacy protection, according to Mahdi.
And a third key factor is that breaches and cybersecurity are now board-level issues at a lot of organizations. Senior executives appear far more willing to spend more on data protection, including encryption. This likely is due, in part, to recent laws that make board members and senior executives potentially liable in cases of data breaches.
As a result of all of this, Gartner predicts that through 2024 more than 60 percent of enterprises will purchase enterprisewide encryption products, up from the fewer than 20 percent in 2018.
Like other aspects of data security, the market has experienced new entrants promising superior ways of encryption using alternate or newer technologies. Examples of such technologies include keyless encryption, hardware-based runtime encryption using the enclave model, multi-party compute, or blockchain.
On the Horizon
Looking ahead toward future challenges, the advent of quantum computing threatens to defeat current encryption methodologies, Taule says. Because of this, his company is investing in privileged account management tools that allow it to use encryption keys with greater bit lengths and increased entropy. It plans to deploy those by next year.
Eventually, FEI Systems will need to start thinking about elliptic-curve cryptography (ECC), Taule says. ECC is an approach to public-key encryption based on the algebraic structure of elliptic curves over finite fields. It requires smaller keys compared with cryptography that does not involve elliptic curves to provide equivalent security.
Elliptic curves can be used for key agreement, digital signatures, and other tasks, and can be used for encryption by combining a key agreement with a symmetric encryption scheme. But Taule says the use ECC for encryption is still years away.
For his part, Frymier is not concerned about encryption’s inability to take on the latest security threats and those that will emerge in the future. “If you have a properly implemented encryption system and you keep your keys secure, it’s pretty immune to compromise — from new or old security threats,” he says.
Modern public key encryption derives its security from the difficulty of factoring a large number into two prime numbers, Frymier says. Some conspiracy theorists think the U.S. National Security Administration (NSA) has solved this problem and can break any encryption.
“Personally, I don’t believe that,” Frymier says. “Others argue that quantum computers will make short work of our ‘modern encryption.’ I’ll start worrying about that when quantum computers become more than a gleam in a theorist’s eye.”



