Security practitioners face so many trials and tribulations as they protect and defend their organizations. In order to seek the best possible protection, they need to have an understanding of the threats which pose the greatest risk and how to address them proactively. This will enable a quicker and more cohesive response to incidents.

The State of the SOC report found that security practitioners are overwhelmed by the sheer volume of alerts and investigations that require their attention. 83 percent of surveyed companies do not even triage half of their alerts per day. Pair that with a landscape of increasingly targeted threats, not enough skilled SOC analysts, and daily news of breaches, it should come as no surprise that security teams are feeling taxed. This is where threat intelligence can help.
The term “threat intelligence” has been used in many different contexts and continues to mature. So first we must agree on what it really means. Then we can understand how organizations use it to inform and protect themselves, with more personalized, and faster insights.
Intelligence 101
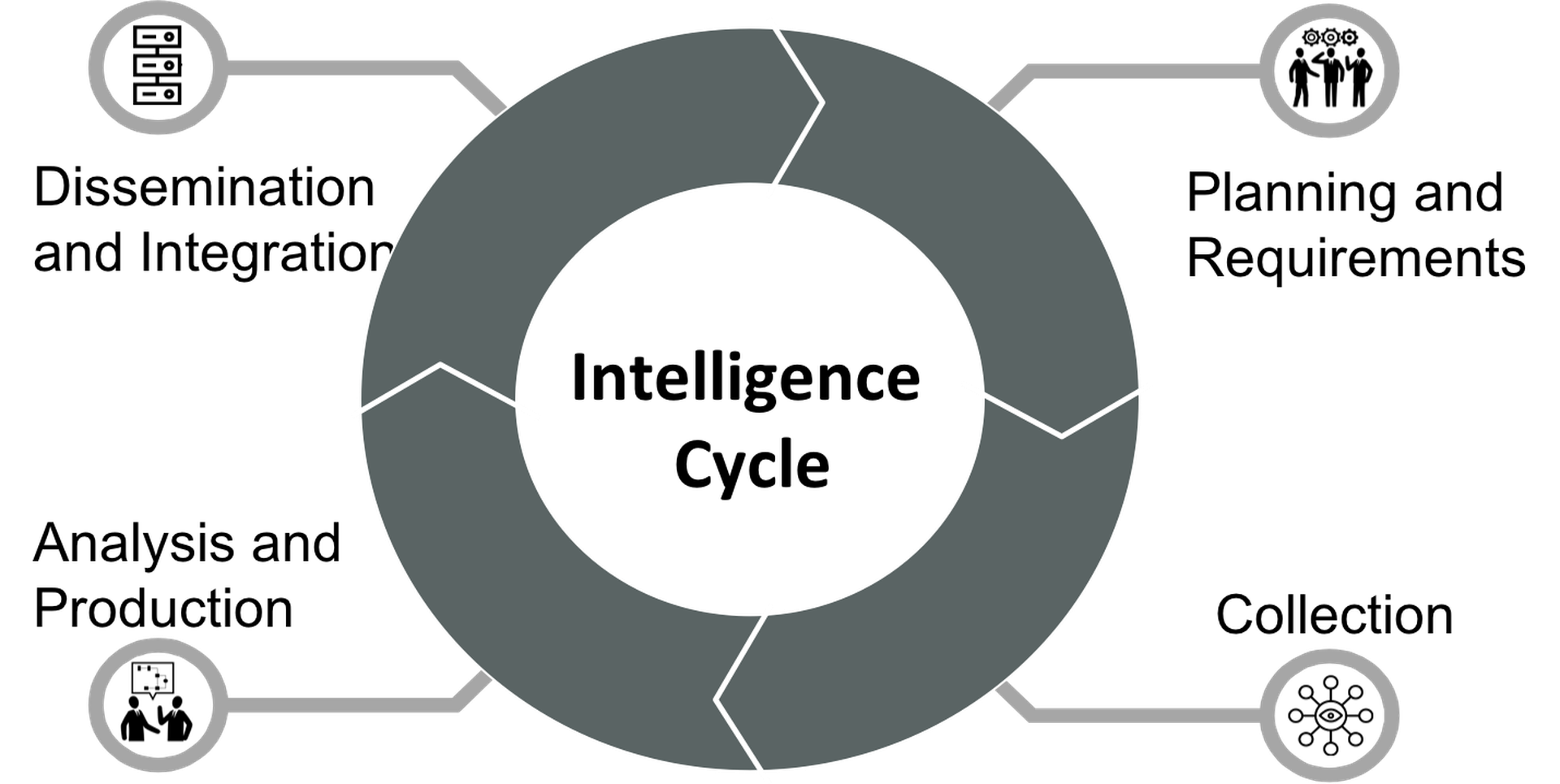
Fundamentally, threat intelligence
involves the planning, collection, analysis and dissemination of information
and countermeasures concerning threats and vulnerabilities to enhance the
decision-making process.
‘Basic Intelligence’ largely deals with past events and brings them to present. ‘Current Intelligence’ is situationally designed to get relevant intelligence outbound to decision makers. While ‘Estimative Intelligence’ is predictive in nature, and used to prepare decision makers for future threats to assist strategic planning.
Intelligence should be utilized broadly to provide a better understanding of the threat landscape an organization faces. It provides support to stay on top of incoming alerts, protect valuable infrastructure and assets by determining top threats facing the organization, and ensure the best security posture.
At its highest impact, threat intelligence can provide indications and warnings of potential attacks, and can be used to identify and prevent vulnerabilities from being exploited.
Intelligence in the wild
Let’s bring this to life. The healthcare industry once again was in the lead for cybersecurity breaches in 2018, claiming a quarter of the more than 750 incidents reported. Healthcare security teams are eager to put a security program in place that can determine when someone in their organization is on a target list to better detect when they could be phished, so they can provide extra security and lower the risk of a successful intrusion.
By bringing threat intelligence analysis into this, the team would’ve analyzed questions including: Which threat actors target the healthcare sector within our geographical area? What are their tools, tactics and courses of action?
At an even more advanced level, threat intelligence could determine the composition and strength of the threat actor – for example, if the threat agent is a group or individual, and, if a group, do we have association?
Using this information – drawing from historical patterns, and actor means and intent – the threat modeler can develop templates for anticipated threat actor courses of action. These actions, described as attack patterns or kill chains, are undertaken to meet the attacker’s objective. The finished piece of intelligence will detail actor history and known courses of action and provide courses of action to be taken to protect.
Adoption Barriers
Threat intelligence offers many benefits, but most organizations don’t have the right teams or skills in place to provide it. As the cybersecurity skills shortage grows worse, oorganizations will continue to struggle to find the right type of talent for getting the full value of threat intelligence. Even if they had the skills, security teams have little time or resources to conduct the in-depth research and additional analysis to produce intelligence reporting, analyse or reverse malware samples and produce countermeasures necessary to detect and stop adversary attacks and exploitation.
As a result, it’s becoming increasingly common for organizations to opt for a partial or complete outsourced model. Partnering with a third-party provider who can assist with parts of security such as threat intelligence, and general threat detection and response, can offer a cost-effective way to allow security professionals to focus on their day job, while threats are identified as quickly as possible prior to or quickly after the point of compromise, by an external team or collaboratively, along with suggested actions for remediation.
As threats increasingly advance, security teams must adopt a ‘lean-forward’ approach. Proactive threat detection methods must be considered, and backed by well-implemented threat intelligence. Only then can organizations learn from the cybersecurity mistakes of the past, truly understand their current security health, and anticipate and mitigate the threats of tomorrow.
Danny Pickens, director of threat research, Fidelis Cybersecurity



