Here’s how the healthcare industry can protect itself during the busy holiday hacking season
The healthcare ransomware conundrum
When ransomware hits a hospital, lives are on the line. Ed Tittel looks at how to deal with cyberattacks when lives are at stake

The medical services industry is in a uniquely vulnerable position when it comes to ransomware. It literally can be a question of life and death. If a company falls prey to ransomware, those in most non-medical industries can pick and choose possible responses. They might even refuse to pay, as did the City of Atlanta, and attempt to restore backups to foil an attack. That sometimes is not an option for hospitals and other acute medical care providers.
The February 5, 2016 Locky attack on Hollywood Presbyterian Medical Center proved that conclusively. The hospital found itself forced to pay 40 bitcoins, roughly a $17,000 ransom at the then-current exchange rate, and had to steer clear of all computing gear for a full week after the attack until normal services could resume.
About a month later, Ottawa Hospital fell victim to WinPlock virus, a variation on CryptoLocker, but was able to defeat that attack. The ransomware was unable to breach the network and infect other computers, but did lock out the systems of four employees after they clicked on a phishing email. A hospital spokeswoman says no patient records were compromised and no ransom was paid, although several hard drives were destroyed.
Healthcare’s vulnerabilities to ransomware are many and widespread, in fact. Hospitals and first responders, for example, use a profusion of internet of things (IoT) sensors and mobile devices of all kinds. This makes them susceptible to mobile or IoT attacks, because such devices are not secured very well, if at all.
Add to this the busy season during the end-of-year holidays, when patient traffic increases for medical professionals, just as in other walks of life. Acute care providers of all kinds, where the biggest threats to life and limb are present, should take preemptive and proactive action as soon as possible to reduce the odds that a ransomware attack might succeed. After all, the holidays are just around the corner.
Understanding the threat and consequences
By definition,ransomware is a variety of malware that seeks out and then encrypts key files on the computers it effects, possibly moving them to a different on-disk location. Then it announces its presence and offers to decrypt those files and restore access in exchange for payment. Typically, such payments are made using anonymous digital currencies, most commonly, bitcoin (BTC).
When a ransomware attack occurs, computer users often cannot access infected systems at all. Sometimes, they might be able to use certain limited parts of the system, but normally users will be unable to access key files and applications by design.That is what provides the impetus to pay a ransom, after all.
In 2016, not only did Hollywood Presbyterian and Ottawa Hospital suffer ransomware attacks, so did Methodist Hospital (Henderson, Ky.), numerous hospitals in the MedStar Health chain (Maryland and Washington, D.C.), plus a cluster of inland California hospitals. In all cases save for the aforementioned Ottawa Hospital breach, doctors and medical staff lost access to key systems used for patient intake and management; some lost certain treatment systems used to administer and monitor patient care, and diagnostic equipment.
Without normal patient handling, records access, or use of specialized diagnostic or treatment equipment, healthcare providers operate at reduced functionality, if they can operate at all. That is what makes ransomware devastating in this industry. It also heightens the temptation to pay a ransom quickly, so as to return to work as soon as possible. In reality, ransomware recovery is never fast or easy, even if a ransom is paid.
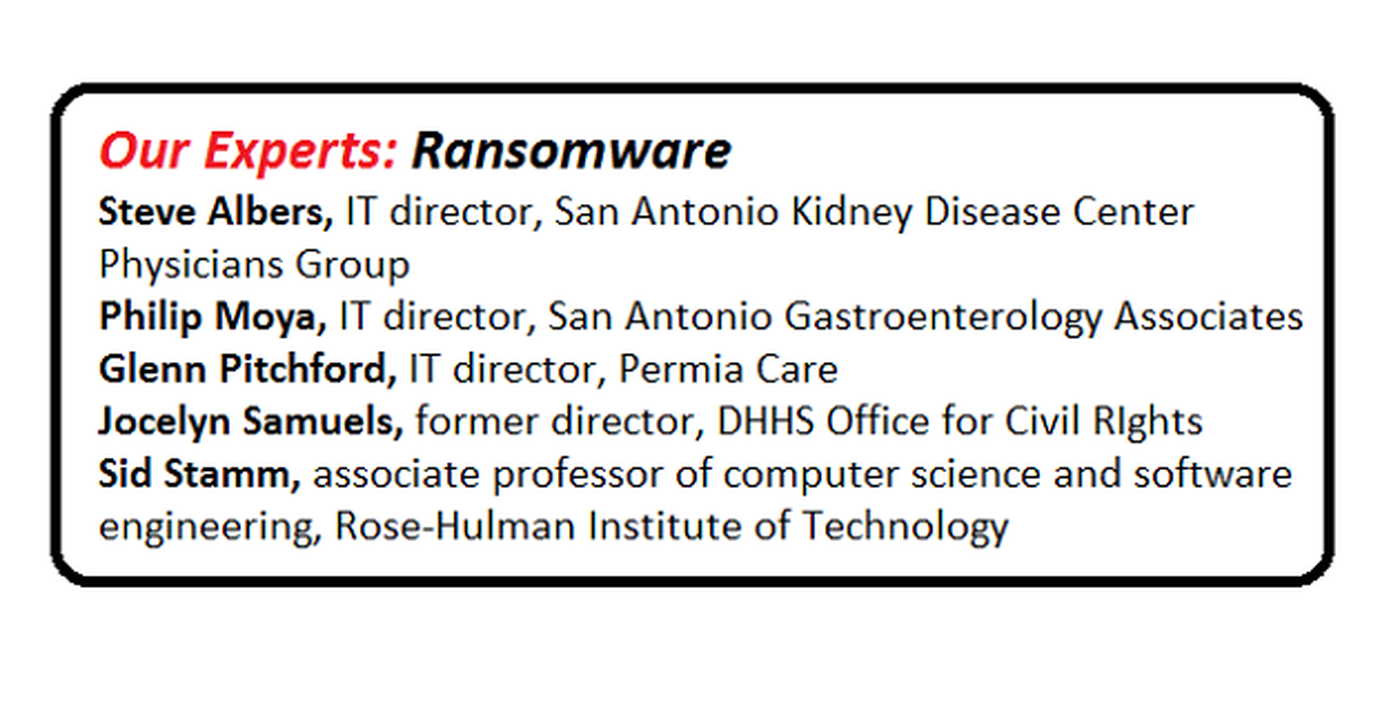
In a prepared statement at the time of the events in 2016, Jocelyn Samuels, then the director of the U.S. Department of Health and Human Services (DHHS, or more simply, HHS) Office for Civil Rights, said: “One of the biggest current threats to health information privacy is the serious compromise of the integrity and availability of data caused by malicious cyberattacks on electronic health information systems, such as through ransomware”
Proactive preparation preempts ransom payment
HHS published an eight-page fact sheet entitled Ransomware and HIPAA (Health Insurance Portability and Accountability Act). This document provides information that is not only useful and actionable, it is also required by the HIPAA Security Rule. In order to maintain compliance and protect themselves from ransomware, healthcare providers should consider the following recommendations:
• Backups:Ransomware denies access to data and applications, so making frequent backups and ensuring they can be restored is essential to recovering from such an attack. A best practice is to test restore procedures periodically. This helps build confidence and familiarity in conducting restore operations, and provides important opportunities to verify backup integrity. Further best practices are to store backups offline, unavailable from networks to which they apply. Many organization choose to store backups offsite at regular intervals as well.
The HIPAA Security Rule requires covered entities and business associates to implement a backup plan as part of an overall contingency plan. This contingency plan likewise includes disaster recovery planning, emergency operations planning,and analyzing criticality of application and data so that all necessary applications and data are accounted for. As with the backup itself, contingency plans must themselves be tested periodically to demonstrate that the organization is ready and able to execute them, and it is shown to be effective.
• Security Incident Procedures: HIPAA also requires procedures for responding to and reporting security incidents (45 C.F.R. 164.308(a)(6)). The organization’s security incident procedures enable it to respond to a range of security incidents, including ransomware attacks. According to the HHS Fact Sheet, proper incident response procedures for ransomware should include:
• Detect and conduct initial ransomware analysis
• Contain impact and prevent propagation of the ransomware
• Eradicate ransomware instances; mitigate or remediate vulnerabilities that enabled or assisted the attack and propagation
• Restore lost data and return to “Business as usual” operations
• Perform post-mortem analysis, which might include a determination if the organization has incurred contractual,regulatory, or other obligations stemming from the incident (for example, HIPAA requires a breach of personal health information (PHI) to be disclosed). Organizations should also incorporate “lessons learned” from an incident and its management process to boost response effectiveness for future incidents.
Potential indicators that a ransomware attack might be underway include:
• User realizes he or she clicked on a link,opened a file or visited a website, any or all of which might have been malicious
• Increase in processing (CPU) and disk activity for no apparent reason (happens when ransomware searches for,encrypts, then deletes original files)
• Inability to access various files while the ransomware is preparing its ransom package
• Suspicious network communications between ransomware and attacker’s command-and-control servers (often detected by IT personnel using intrusion detection products)
For healthcare providers not already in the know, National Institute of Standards and Technology’s (NIST’s) 2012 document Computer Security Incident Handling Guide also provides useful information for medical IT professional.
Best practices in avoiding attacks
In talking to IT professional and security experts, one can gather some useful advice and actions to avoid in pondering and possibility implementing security practices to help to fend off or deal with ransomware. All parties are unanimous about the value of creating backup and testing restores in order for organizations to shake off ransomware attacks.
Glenn Pitchford,IT director at Permia Care in Midland, Texas, says, “We don’t worry overmuch about ransomware. All our critical systems, including email, accounting, and patient information systems, get a nightly incremental, with a full backup on weekends. We also back up end user PCs and workstations no less than every three days.”
He says the firm conducts quarterly backup checks in which random machines are targeted for restore, and annual disaster recovery drills where the entire infrastructure is rebuilt from scratch. “That’s the right way to do it,” he concludes. “We know we can restore.”
Sometimes, the issues that medical service providers encounter in seeking to implement ransomware protection are more personal or political than technical. Apparently, this is not uncommon when working in physician-owned and -run facilities where the users might also be executives or owners of the company.
Pitchford recounts that he used to shame users who fell prey to phishing attacks, but that changed when ransomware came along. He notes, “One response to shaming is to duck your head and stay quiet. That does not work if ransomware is spreading in the organization. I elected to roll out user awareness training across the board, with follow-up and counseling for those who still succumb to monthly simulated phishing and other attacks. My employees have told me I’m a kinder, gentler guy now that I simply email them and their bosses when they screw up. Thanks to the training, the failure rate for monthly tests is under 5 percent.”
Indeed, most of the IT professionals interviewed for this story agree that user awareness training, if included in employee onboarding, repeated annually for all hands, and tested monthly,significantly diminishes the human attack surface in their organizations.
Balancing risks and rewards
Sid Stamm,associate professor of computer science and software engineering at the Rose-Hulman Institute of Technology in Terre Haute, Ind., offers some interesting approaches to help medical professionals, and their operations, stay secure. He notes that making security decisions is all about understanding risks, and balancing convenience and ease of use against security and integrity.
Stamm observes that most physicians understand risk very well, because they deal with risk assessment routinely as part of their jobs in making diagnoses and treating illnesses or conditions.
“If you put it to them in terms of risk, they should be able to understand that attaching the MRI (magnetic resonance imaging), the Bayer Medrad machine, or some other piece of computer-based medical equipment to the internet is a bad idea. Ask them to consider the hourly income the machine produces, then remind them that it falls to zero when it’s locked up by ransomware.”
He goes on to observe that it is cheaper to equip doctors with mobile tablets or laptops they can use for email, web access, or whatever they need, than to try to restore a major medical device made unusable by malware.
This same risk management argument might also work with physicians or executives who insist they be granted administrative rights to entire systems, including their own. IT professionals readily admit this can be a challenge.
Steve Albers, IT director at the San Antonio Kidney Disease Center Physicians Group in New Braunfels, Tex., puts it this way: “If I have to field a call at 10:30 p.m.from work, I’d much rather have it be to ask me to install an application for somebody than for them to tell me ‘We’ve been hacked!’”
Albers admits it is an uphill slog to get physicians to buy into restricting their own access rights and ability to install whatever programs they want. But when he tells them what could and sometimes does happen to medical practices that allow that kind of thing, they usually stop fighting. “I might get two or three of those calls a year, but I’m happy to get to work and help my doctors out when they need it after hours because I know it’s saving me and everybody else potential heartache and business losses.”
Some preventive techniques sound good but…
According to numerous resources on ransomware, one strong and effective technique for dealing with end-user equipment is to implement application whitelisting. This draws on the traditional and well-respected principle of least privilege. It is easily restated as “Deny everything; permit access only by explicit exception.”
In the case of running applications, that means the operating system checks before launching applications if they are on a whitelist or not. If they are on the list, they can run; if not, they cannot.This is indeed an extremely effective technique for controlling what software can run on any computer. It will stop ransomware and nearly all other malware dead in its tracks.
Philip Moya, IT director at the San Antonio Gastroenterology Associates, a multi-office practice with dozens of physicians and hundreds of staff in Texas, actually tried whitelisting to see what it would take to implement this technique. He observes that “It’s completely particular to each individual. You have to somehow collect data on all the applications they use and put them on their specific whitelist. Then you have to be quick when they discover one they overlooked, or want to add a new one.”
He says a monitoring tool that could report on a week’s worth of activity on a per-user basis would probably capture 80-90 percent of what each user’s whitelist would need to contain. But without helpful automation, the amount of time and effort involved in whitelisting makes it impractical and infeasible.
Another interesting lesson can be gleaned from one of Moya’s former employers. The company had been hit three times by ransomware, he says; at least one attack was successful because an accounting employee broke protocol and saved important data files to her local drive rather than to a better-protected server, he says.
Even though the server was unaffected by the ransomware attack, the company ended up having to pay the ransom because the latest backup of the employee’s laptop did not have a copy of the all-important current invoices file. The moral of the story, he says, is to make sure that employee security awareness training also extends to teaching those employees whose files are important to their jobs, and what steps they must take to keep them safe from attack.
All of the IT pros and security experts agree that whenever a ransomware attack succeeds,careful investigation usually reveals that somewhere in the fracas an employee did not follow existing policy or the rules for what can be accessed, how, and when. Whenever a phishing message, a drive-by download, a malicious email attachment, or a Trojan horse shows up inside unauthorized and perhaps even unwanted software, it is because somebody did not follow the policies and procedures. More than anything else, that is why security awareness training is a linchpin for good organizational security, and why regular re-training and subsequent testing through simulated phishing emails, mock sites, and so forth are absolutely essential, the experts say.
While technology is great at finding and stopping many attacks, it still falls to the individual not to click on links they do not recognize, load files or pictures from unknown sources, and, generally speaking, take part in unsafe computing practices. A little education, experts agree, goes a long way to stop the problem. A lot of education does an even more effective job.



