The private encryption key used by Chinese hackers to break into the email accounts of high-level U.S. government officials disclosed last week also gave them access to a vast array of other Microsoft products, according to new research from cloud security firm Wiz.
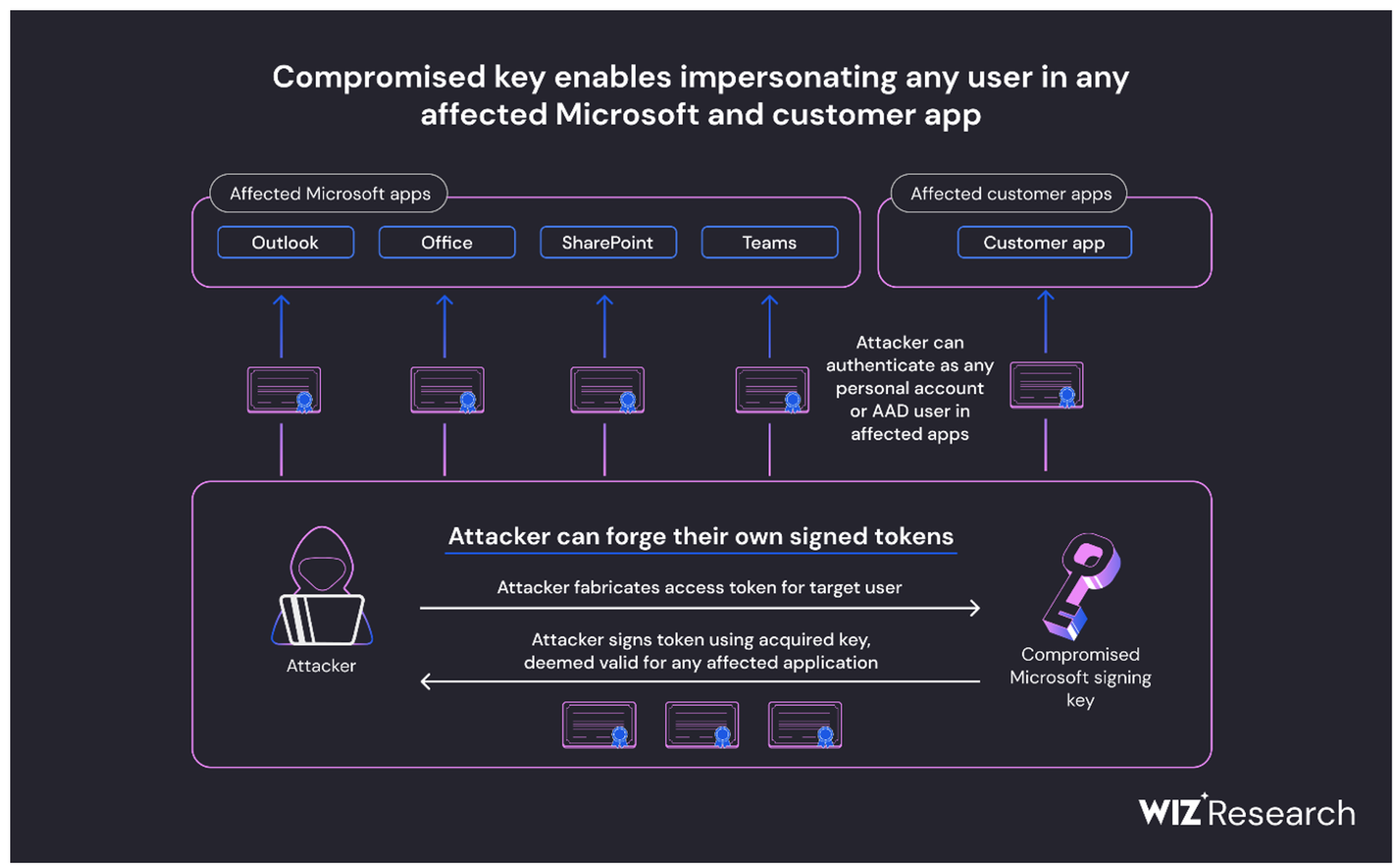
On July 11, the Redmond-based tech giant disclosed that a threat actor linked to the Chinese government had — through an acquired Microsoft private encryption key — forged authentication tokens that gave them access to Exchange Online Outlook email accounts for more than 25 organizations, including government agencies.
In a blog post published Friday, Shir Tamari, head of research at Wiz, said further investigation has revealed the compromised key would have given the hacking group, which Microsoft calls Storm-0558, access to far more than Outlook, spanning many other Microsoft services that uses the same authentication process.
“Our researchers concluded that the compromised MSA key could have allowed the threat actor to forge access tokens for multiple types of Azure Active Directory applications, including every application that supports personal account authentication, such as SharePoint, Teams, OneDrive, customers’ applications that support the 'login with Microsoft' functionality, and multi-tenant applications in certain conditions,” Tamari wrote.
Wiz said they worked closely with Microsoft in advance to ensure the technical accuracy of their findings.
Another issue flagged in the research: while Microsoft revoked the key and gave detection guidance to organizations, the lack of logging it provides around the token authentication process could make it “difficult” for customers to detect if forged tokens were used against their applications.
“Unfortunately, there is a lack of standardized practices when it comes to application-specific logging. Therefore, in most cases, application owners do not have detailed logs containing the raw access token or its signing key,” wrote Tamari. “As a result, identifying and investigating such events can prove exceedingly challenging for app owners.”
The type of key stolen by the hacking group is among the most powerful in modern IT and the flaws it exploits are not unique to Microsoft. It has been used for numerous Microsoft products, including Azure personal accounts and Azure multi-tenant applications, since April 2016 and the public certificate for it expired on April 4, 2021.
Acquiring it would have allowed the actor to stealthily gain “immediate single hop access to everything, any email box, file service or cloud account” without the need to impersonate a victim’s server. According to Wiz, Microsoft replaced the key sometime between June 27 and July 5, 2023.
The analysis indicates that the key’s access for Azure Active Directory affected applications that worked with version 2.0 of Microsoft’s OpenID and were set to support “Personal Microsoft accounts only” as well as “mixed audience” and other personal Microsoft accounts on services like Skype and Xbox. Multi-tenant Azure AD applications that used “common” version 2.0 key endpoints were also affected. Single tenant applications were not.
While Microsoft developed an extension to limit the ability of these types of keys to gain broad-based access, it placed responsibility for implementing that extension on the shoulders of its users.
Microsoft revoked the affected key, but Wiz warned that a sophisticated APT could have used the access and time to build in backdoors or other forms of persistence into victim systems and accounts. Further, any applications that rely on local certificate stores or cached keys may still be using the corrupted key and would be vulnerable to continued exploitation.
The end result is that the impact from the compromise may be far broader than what Microsoft has disclosed thus far. The pool of Microsoft and customer applications affected number in the millions, and the lack of logging around authentication means many organizations will be in the dark about whether they were compromised through the breach.
"The full impact of this incident is much larger than is being widely reported and understood. We believe this event will have long lasting implications on our trust of the cloud and the core components that support it, above all, the identity layer which is the basic fabric of everything we do in cloud,” Tamari wrote. “We must learn from it and improve.”




