
Cloud-based IAM puts authentication to the test
Traditional brick-and-mortar organizations with on-premise servers are striving every day to keep pace with cloud-driven digital enterprises that are untethered by physical restraints, enabling employees to work from anywhere, accessing applications, services and mobile devices as regular parts of their flexible workdays.
However, much like ducks on the surface of a pond, the challenges inherent in migrating from traditional, on-premise operations to transformed, cloud-driven services is generating a frenzy of activity just beneath the surface.
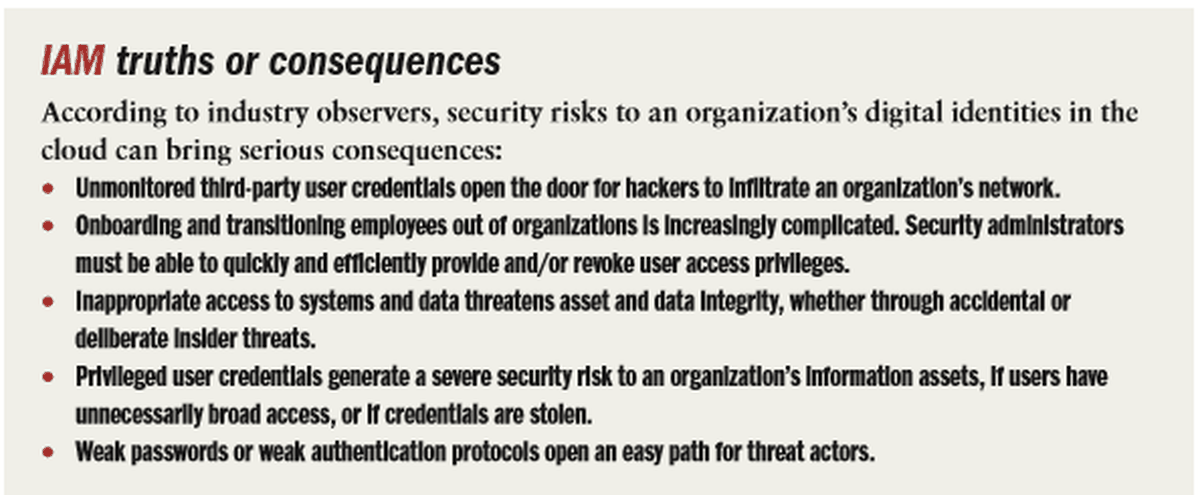
For most organizations, migrating to cloud services is still heavily labor and resource-intensive, and can create serious operational deficiencies if not properly implemented with security protections built-in from the start. And those ongoing operational deficiencies only widen the attack surface, threatening to harm an organization’s bottom line.
This is why organizations must focus on reducing complexities and strengthen security protections, especially identity and access management (IAM). Finding ways to make IAM simpler and more informative can help reduce operational risks, although it remains a daunting challenge for most organizations today.
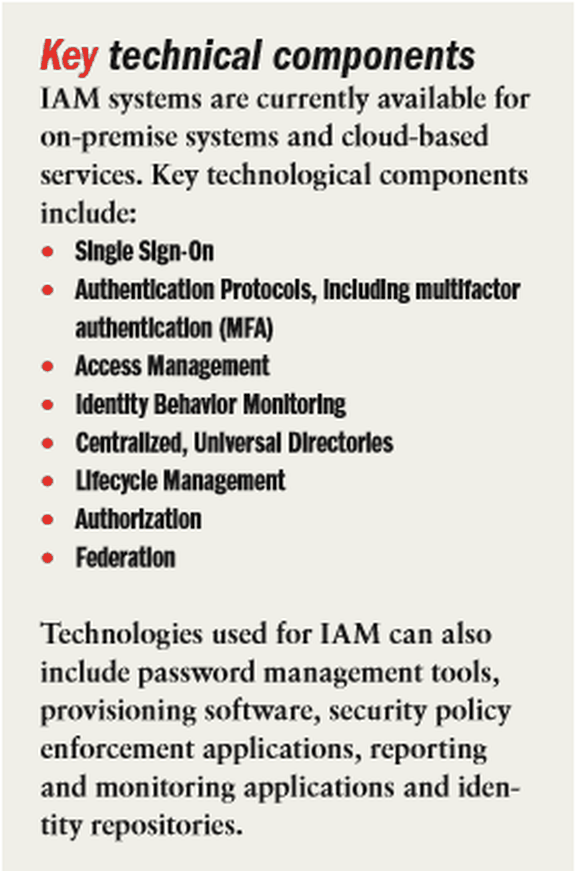
IAM is used in both traditional and cloud-based organizations to protect assets, ensure user identities, achieve regulatory compliance and deliver friendlier customer experiences in an agile, efficient way. Access Management-as-a-Service (AMaaS) offerings are growing increasingly popular. Gartner Inc., estimates that 75 percent or more of clients based in North America and approximately 50 percent in Europe, and some APAC region countries are seeking Identity-as-a-Service (IDaaS) delivery models for new access management purchases.
Most companies today fully recognize the need to protect identities and manage access to corporate resources. But “they often fall short when it comes to planning for and investing in necessary security mechanisms such as IAM, to help ensure strong asset protection,” says Michael Osterman, president of Osterman Research, Inc.
To shrink a company’s attack surface, Osterman recommends that organizations use a centralized repository “to create, authenticate, and save user identities in a single, ‘federated’ identity database.”
Critical operational systems require higher levels of authentication, he adds. And “behavioral analytics can help an organization establish what actions constitute normal behavior and what other actions might be problematic,” he explains.
But while executives grasp the concepts involved in IAM, “they typically don’t invest until something bad happens,” he adds.
Traditional IAM tools are often cumbersome and complex to deploy and maintain, and many cloud services do not deploy automatically with strong IAM security mechanisms in place. This means, as organizations migrate more of their infrastructure to the cloud, the need to address complex authorization controls for cloud-based resources will only grow. Policy-driven, attribute-based access controls (ABAC) for IAM can help provide fast, dynamic authorization to cloud services, Osterman says, enabling secure access to services, along with other critical assets, such as applications and data stored in the cloud.

president, Osterman Research
Managing identities and access
IAM is used to manage the roles and access privileges of individual users and the circumstances by which users are granted (or denied) access privileges. Users can include everyone from customers to suppliers to partners and employees. IAM creates one digital identity per individual. Once a digital identity has been established, it must be maintained, modified and monitored throughout each user’s access lifecycle.
IAM is considered crucial to controlling access to enterprise resources, by the right users, in the right context, from the time a user joins an organization and gains permission to access certain resources to that user’s departure and timely de-authorization. Security administrators use IAM tools and technologies to change a user’s role, track user activities, create reports about user activities, and continuously enforce access control policies.
Designed originally to provide a means for administering and controlling employee access, either to applications or to physical buildings across an organization, IAM tools also help ensure compliance with corporate policies and government regulations, says Bill Newhouse, deputy director of the National Initiative for Cybersecurity Education (NICE) and senior security engineer at the National Cybersecurity Center of Excellence (NCCoE), both based out of the National Institute of Science and Technology (NIST) offices in Gaithersburg, Md.
There are two basic security elements required to control access to systems and data: authentication and authorization. Authentication is the process required to sign into an application or log in to a computer. The entire purpose of authentication, including multi-factor authentication (MFA), is to enable security functions to complete authorization, Newhouse explains.
Authorization determines which buttons a user can click, which accounts he or she may edit, and even which files or databases each user is allowed to access.
MFA has grown to become an essential element of cloud-based IAM, to ensure user identities no matter where they are working from on any given day. There are some weaknesses, however, says Adrian Lane, security analyst and CTO for Securosis in Phoenix. “There have been SMS messages advances such as behavioral analytics for both the user and devices, to authenticate users.
“Cloud security providers typically use multiple attributes and can adjust access policies for any user or role, which dramatically improves identity and access control,” Lane explains. In too many cases, however, “organizations have yet to take full advantage of the more granular, attribute-based, policy-driven IAM services available from cloud security providers,” he adds.
Understanding cloud IAM
Cloud-based IAM security services are considered next-generation tools, combining concepts of Identity-as-a-Service (IaaS) and enterprise mobility management (EMM).
While traditional or legacy IAM products were designed to handle logins and user activities from a centralized location, for a specific enterprise, or for proprietary applications and known endpoints, cloud identity management is optimized for integration across devices, operating systems, applications and resources.

This is essential because migration to the cloud opens access to endpoints that are typically outside of brick and mortar buildings and spread across multiple locations, Lane explains.
Industry observers maintain cloud IAM services can manage user access to Wi-Fi networks, connect cloud servers, and facilitate authentication. Properly implemented, it can prevent outside threat actors from reaching corporate databases and in a “least privileges” security model, it also keeps insider threats at bay.
As organizations modernize, some are finding cloud-based IAM is often not well suited for accessing on-premises applications. Authentication protocols must expand and scale as an organization’s IT environment scales, to provide necessary security protections, while balancing employee and customer needs for access to resources. As organizations embrace cloud services, they need stronger, all-around governance across all platforms. This creates an operational challenge with underlying technical difficulties, according to Gartner Research Vice President Lori Robinson.
Gartner analysts maintain cloud IAM that leverages SAML-based (Security Assertion Markup Language) authentication and multifactor authentication can help IT security teams manage the challenges involved with decentralized user accounts. According to Gartner, “access to cloud databases and assets must be tightly monitored, especially during employee onboarding and off-boarding processes. Cloud IAM services can also track which users are accessing which resources and when, which is vital information for security and regulatory compliance.”
As organizations migrate to cloud services they must focus on how cloud services are accessed, along with the speed and pace of migrating additional apps and services. The trouble is, many organizations today still struggle to properly implement traditional on-premise IAM, says NIST’s Newhouse.
Each organization’s security teams must gain a clear understanding of whether current IAM platforms will also protect cloud storage. If not, it is time to evaluate cloud-based IAM alternatives. “Employees, customers and the organization’s reputation are at stake without proper IAM security protections in place,” says Newhouse.

Ultimately, every organization needs strong IAM to protect cloud and on-premise resources. A recent Forrester Research report says cloud-based IAM has “completely transformed the IAM market landscape,” by delivering identity and access management at a reduced cost and with less complexity, adding cloud scalability and elasticity advantages. Analysts Andras Cser and Merritt Maxim describe the current IAM market as currently “divided between established vendors with ‘on-premise pedigree’ who are making the switch to the cloud, and those ‘born in the cloud.’”
While legacy systems and security vendors provide robust IAM capabilities, Forrester analysts warn those platforms can be difficult to implement and maintain. In some cases, industry analysts report IAM platforms have failed to live up to expectations because of their cost and increasing complexity. Many organizations face difficulties integrating access control between older on-premise servers and cloud services.
“While extending IAM to the cloud in hybrid environments isn’t an insurmountable challenge, it’s no easy task, and many organizations end up opting to outsource this task,” says Lane.
One cloud IAM challenge occurs in identity provisioning — the secure and timely management of on-boarding and off-boarding users in the cloud. “It takes careful planning to ensure system resources are properly allocated so performance doesn’t degrade drastically when more users than expected login to access those resources,” Lane explains. According to Forrester’s Cser and Maxim, cloud-native providers deliver IAM features that are easier to implement and use, but which “may not offer the same depth of policy management capabilities that some on-premise pedigree vendors do.”
Choosing the right IAM platform is largely dependent on each organization’s priorities. One organization might choose to focus on securing super user accounts for privileged access management (PAM), while another in a more contentious regulatory arena might focus instead on the management of digital roles or identity governance and administration (IGA). Still other enterprises could opt for modern biometric authentication (BA).
“Only by comparing IAM platforms can an organization determine what will work best to properly secure digital identities,” says Osterman.
Overcoming challenges
Organizations must alter their deployment methods, and the ways they use security tools to effectively manage IAM across multiple cloud services. “There’s a steep learning curve and education required to gain a better understanding of how to manage identities in the cloud,” says Lane.
Another challenge involves managing identities across multiple organizations. Advances such as federated identity management (FIM) can help here, according to Newhouse. FIM enables organizations to authenticate users of cloud services, using the organization’s chosen identity provider. For example, a user with a Google account identity can add various applications provided by external providers. The user logs on using his or her Google account ID to access any applications, and is authenticated and authorized as needed.

security analyst and CTO, Securosis
Those just starting the process of purchasing IAM, or in search of a new cloud-based IAM platform, must properly compare current IAM platforms and services. While it is possible to control access manually to organizational resources, manually controlling privileges is often unreliable and inflexible. Ultimately, specialized tools are still needed to ensure the organization’s security team can properly manage identities and access to resources. As companies strive to modernize, automate and streamline operations, Gartner recommends organizations examine leading cloud IAM alternatives to achieve greater security, privacy and regulatory compliance.
Gartner recommends that organizations “craft a robust cloud IAM strategy. Automate and simplify IAM processes for agility and efficiency. Meet changing customer needs with consumer IAM. Protect APIs and ramp up fraud protection.”
Tips and best practices
Gartner recommends organizations focus on “careful” scaling — too narrow creates inconsistent enforcement, too broad will only increase complexity. And the stakes are high. Gartner predicts that by 2021, enterprises with IAM tools will be at a 50 percent lower risk of advanced threat impacts compared to their peers.
Gartner recommends organizations hone in on ways to reduce: Reduce the number of permanent privileged accounts. Reduce the number of shared accounts. Reduce the duration of temporary privileges. Reduce the entitlements of each account. Embracing a principle of least privilege, in which each account has as few entitlements as possible, should be the rule.
Industry observers also stress that organizations must embrace greater governance, especially IGA. Without IGA, organizations risk excess privileges, orphaned accounts, and ownership conflicts that will plague the organization. IGA can aid compliance efforts, audit privileged accounts, and enable access certification. Integrating IAM with IGA can provide the most comprehensive identity and access management available.
Organizations leveraging social media to interact with customers and increase brand awareness need strong IAM in place to protect corporate accounts. Using MFA to alert users of multiple failed login attempts, and educating employees on social media security is crucial to reducing the risk of social identity breaches, according to Lane.
Organizations with many on-premise servers should consider issuing SAML tokens or other assertions that focus on creating roles users can assume to reduce the potential for propagating tens of thousands of orphaned user accounts in the cloud. “When security administrators propagate roles linked to specific job requirements, they can easily add SAML tokens to give users resource access. And when a user leaves, the role remains, Lane explains.
To simplify IAM in hybrid cloud environments, it is important to also focus on ways to reduce access latency to cloud services. Organizations must reduce the latency caused by sending authentication and local authorization requests from the cloud back to on-premise servers, says Lane.
Futures
Industry observers expect organizations will start to embrace greater identity governance elements as they work to better manage identities and access to valuable information and personal identity resources, across everything from mobile devices to cloud services.
Looking ahead, those observers expect growing interest in the ways that IAM fits into the internet of things, or more appropriately, the identity of things. As the number of intelligent things skyrockets, Osterman says, “it’s not difficult to imagine scenarios in which a refrigerator or other smart home technology could be compromised, enabling a hacker to access a consumer’s home network. Because IoT technologies have been rushed to market without a clear focus on security, including IAM, the potential for breaches is enormous.”
Gartner’s Robinson expects artificial intelligence-driven analytics will improve IAM efficiency, especially in reducing bloated administrative procedures, or fraud prevention. Cloud IAM providers can help organizations enable adaptive authentication, analyzing both positive and negative signals of trust to look for ‘normal’ patterns from individual users or types of users.
As organizations increasingly embrace cloud services to achieve digital transformation, they hopefully are starting to realize that their success will depend on IAM.



