Despite best cybersecurity efforts, small- and mid sized businesses (SMBs) continue to struggle to thwart attacks and harden defenses. Exploits, trojans and backdoors continue to plague SMBs in 2023, with no perceptible change in frequency of attacks from 2022.
The data comes from researchers who warn that SMB business are struggling to gain an edge on their cybersecurity needs as they juggle 2023 challenges such as remote workforces, fighting inflation, tackling supply chain issues and investing in new revenue streams.
The report titled Cyber-resilience During a Crisis is authored by Kaspersky and looks at the biggest threats facing SMBs within the first five months of 2023.
"The vulnerabilities faced by SMBs are not to be underestimated,” said Vasily Kolesnikov, a security expert at Kaspersky in a press statement announcing the report. “As these businesses are the backbone of most countries' economies, it is crucial that governments and organizations alike step up their efforts to safeguard these enterprises. Awareness and investment in robust cybersecurity solutions must become a top priority to protect SMBs from evolving cyber threats."
Key finding of the report
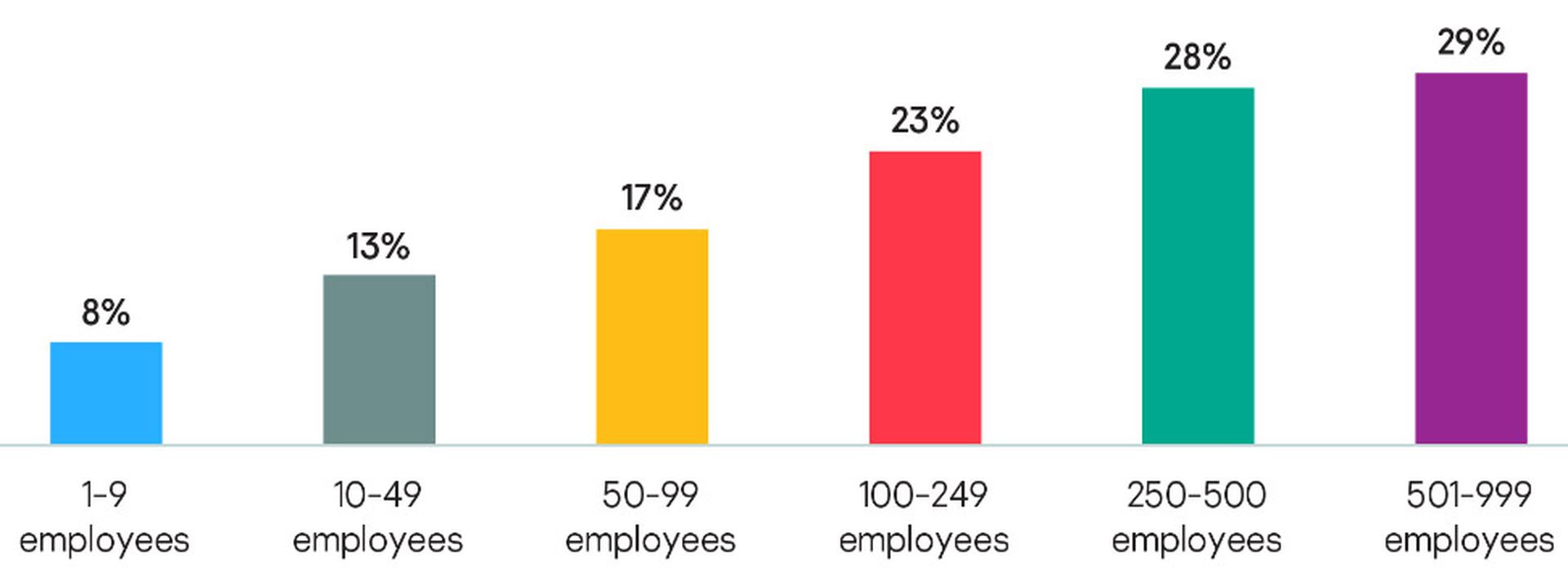
Attacks on SMBs have been a concern for the past couple of years as security researchers have said companies with fewer than 100 workers are vulnerable to social engineering attacks. A Kaspersky study from last year found that four in 10 SMB employers admitted that a cybersecurity incident would be a major crisis for their business, superseded only by a slump in sales or a natural disaster.
Kaspersky conducted the most recent study by collecting data from SMB clients and the use of software applications such as Microsoft Office, Teams and Skype. It then ran these software names againstits telemetry to find out how much malware and unwanted software was distributed by these apps.
Between January 1 and May 18 of this year, 2,392 SMB employees in the Kaspersky network encountered malware or unwanted software disguised as business apps, with 2,478 unique files distributed in this way. The total number of detections totaled 764,015.
The researchers found that exploits accounted for 483,980 detections – well more than half. Exploits are malicious programs designed to take advantage of vulnerabilities in software. They typically run other malware on the system, elevate an attacker’s privileges, or cause the target application to crash. They often penetrate a victim’s device without any action by the user.
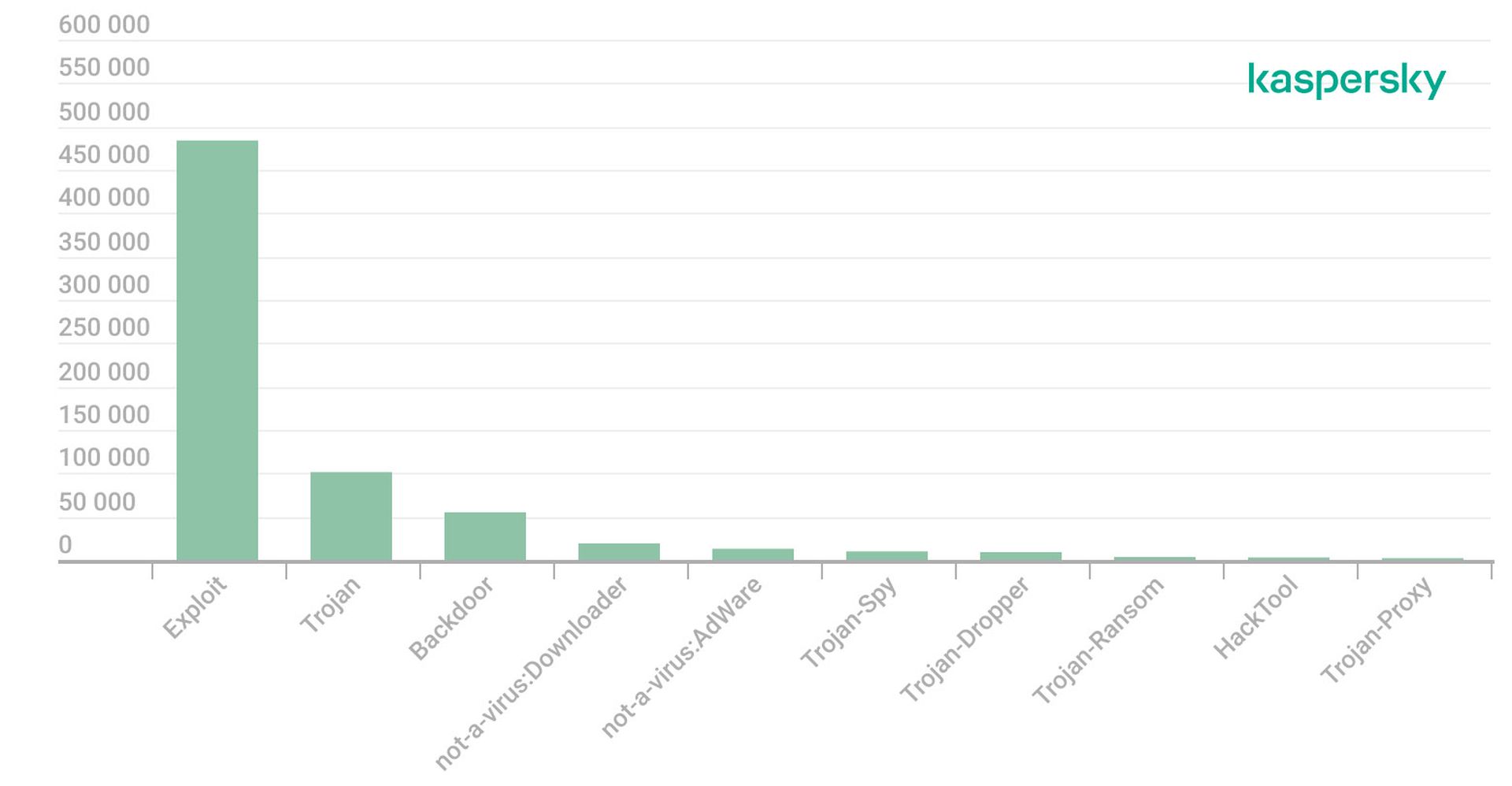
Trojans, the second-biggest SMB threat, enter the system in disguise and then start loading malware. A Trojan can perform various destructive actions, such as deleting, blocking, modifying or copying data, or disrupting the performance of a computer or a network.
While exploits and trojans are very common, the researchers said backdoors are among the most dangerous types of malware because once they infiltrate a victim’s device, they give attackers remote control. Once attackers gain control, they can install, launch and run programs without the consent or knowledge of the user. Attackers use backdoors to send, receive, execute and delete files, and harvest confidential data from the computer.
SMBs are often more of a target than they realize, said Mike Parkin, senior technical engineer at Vulcan Cyber. While an attacker’s potential take is smaller, it’s a low-risk attack and SMB organizations often have less investment in cybersecurity than larger organizations. SMBs are particularly susceptible to ransomware and business email compromise attacks, said Parkin.
“While zero-day exploits and other high-profile attacks get a lot of attention many, if not most, attacks still target users,” said Parkin. “For SMBs, that usually means phishing emails or other social engineering attacks that lead to compromise, or business email compromise attacks that can lead to direct losses through fraud. “SMBs are often resource-restricted when it comes to cybersecurity, which means they need to be efficient with the resources they do have. Focusing on user education can deliver a lot of value for the investment.”
Many SMB organizations have good security measures for their core IT systems, but they don’t for their IoT and OT devices, said Bud Broomhead, chief executive officer at Viakoo. These devices often are used by malicious hackers to gain access to a network, and in many SMB environments, Broomhead said that network access lets attackers move laterally to breach core IT systems. Some remediation: an automated method of firmware, password, and certificate management on IoT/OT devices can dramatically reduce the attack surface within an SMB.
“The proliferation of connected devices, especially IoT/OT devices, has led many organizations to lose track of what they have, let alone be able to secure them,” said Broomhead. “With many SMBs still having employees work from home, the blending of work and home networks has expanded the opportunities for unsecure devices to breach and exploit corporate resources. More SMBs are turning to outside service providers to perform a range of services, such as having a virtual CISO do security assessments and maintain cyber hygiene on IT and IoT/OT devices.”





