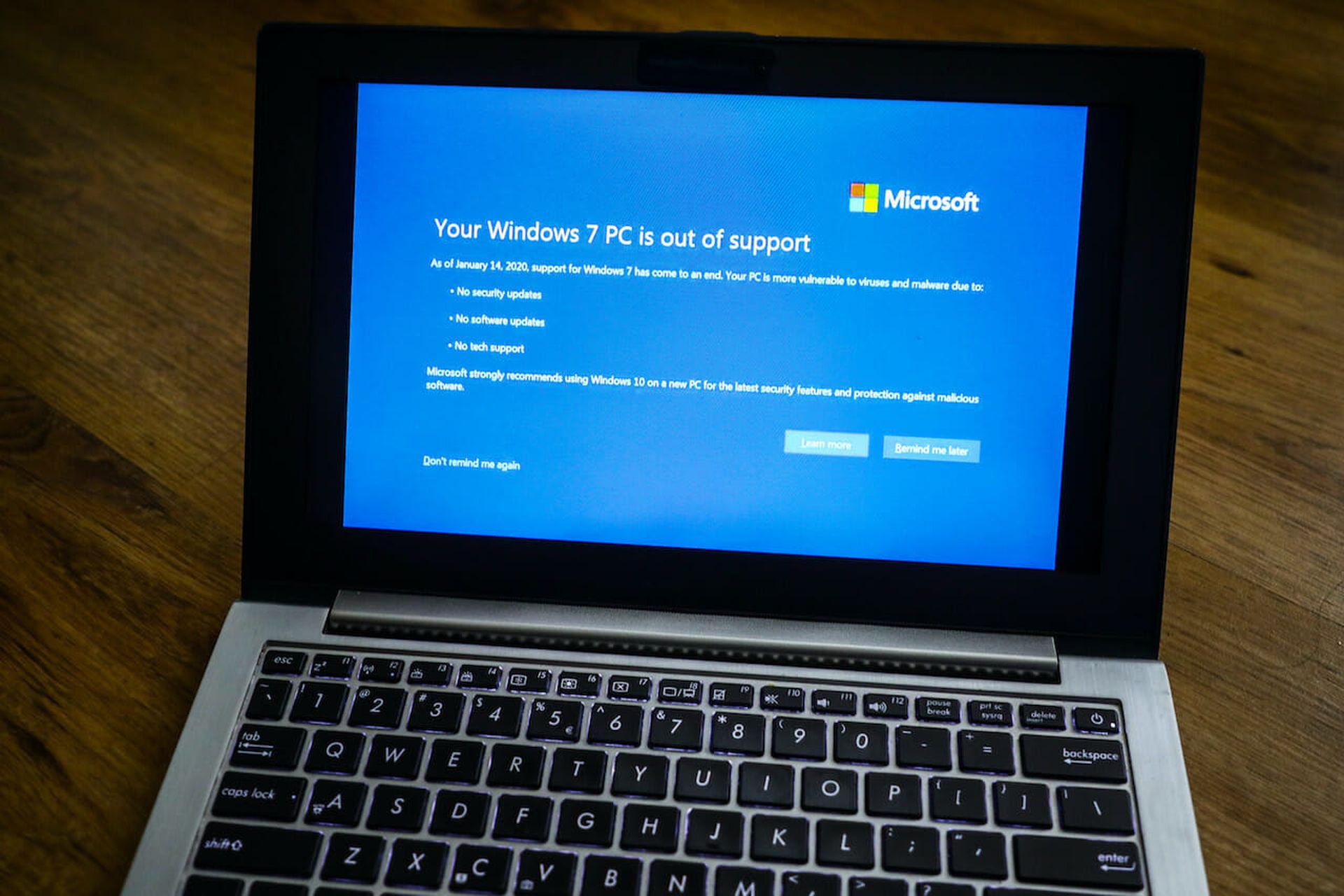
Microsoft finalized the end-of-life for the Windows 7 operating system on January 14, 2020. There are no more updates and in most instances Windows 7 will get replaced by Windows 10. For many IT staffs, the end-of-life for Windows 7 has created a huge security hole for companies still running the old operating system.
How big a hole? We estimate that roughly 50 percent of the machines that run Microsoft Windows in a business setting still use Windows 7 or an even earlier version. These machines are no longer receiving the security updates required to keep applications and the data contained within them, secure and compliant.
Windows 7 and earlier operating systems still exist because the applications that were built to perform on them are difficult to migrate onto the next-generation Windows 10 operating system. So organizations maintain the old operating systems, keeping them in place to maintain the applications that run their businesses.
Now that Microsoft no longer issues the updates for the older operating systems, hackers are exploiting the inherent vulnerabilities in these unpatched systems every day. Here are some tips for security pros and IT staffs facing these end-of-life issues:
- Embrace next-generation cloud computing. Today, businesses know that the cloud stands as the future of commercial software. As 32-bit computing gives way to 64-bit, we find ourselves at an inflection point with legacy systems and how they will move to the cloud. There will be no more security patches for Windows 7, leaving machines and applications vulnerable. Windows 10, the likely new destination for Windows 7 shops, runs on a 64-bit operating system. This next-generation computing will not accommodate applications built for 32-bit machines. IT staffs face largescale business continuity issues, leaving them with a choice to carry on working with an insecure operating system or recreating the app for modern computing using cloud services or web solutions. We understand that budgets are tight, but organizations can’t maintain security under these new end-of-life conditions.
- Take control of your data. Gartner estimates that 99 percent of the vulnerabilities that hackers exploit are already known to security and IT professionals. There’s a huge wave of applications in which security and IT pros know there are problems, but they don’t have the time or resources to recreate them on Windows 10. However, by centrally procuring and deploying solutions, developers can update their own apps and help the business maintain central control of security policies and data.
- Go after the shadow IT. Business organizations use shadow IT to recreate the legacy application experience, but in online, unsecure environments. For instance, not all businesses are ready-to-go when it’s time for a necessary update or change of the operating system. Existing 32-bit applications have a very high chance of not working on new, updated 64-bit machines. Often, the IT team has no time to make the fix, or it’s simply not in the budget, so the business team finds its own solution. They export the necessary data, import somewhere else, often in an unsecure and non-compliant place, and get back to work. There are millions of apps exported to online cloud apps and when this happens, the business no longer has any insight or control of the data and security and compliance risks are opened. If businesses install a centralized, no-code application modernization and building solution, users can securely migrate their application to a modern application and get on with their work.
- Look to the future. Make sure there’s a future-proof cloud app deployed in the business, so users can keep data secure, compliant and inside the company’s control. By procuring a cloud-based product that reassures the security and stability of your team’s applications, it also unearths a huge data opportunity that’s been previously unreachable. Legacy applications maintain data and its context on local machines, so by upgrading these apps to a solitary cloud app, it brings all data into a single location for future analysis, consolidation and further innovation.
- Focus on application security. The company needs to have breach detection and log-in controls placed on any data in the business. This makes the organization’s valuable information difficult to access and eliminates any liability concerns because the company has made a good-faith effort to protect the data. Hackers often attack the application level. Once that happens, there’s no security attached to the application itself, making all of the attached data available. If the applications have been connected to any larger databases, this also gives the hackers a gateway to that data.
While many businesses still run Microsoft 7 or earlier versions, now that its end-of-life has passed, businesses need to stay flexible, consider their options, ensure and maintain compliance and update with the many centrally-controlled cloud apps available. It’s really import for organizations to focus-in. So many of the breaches and ransomware attacks we read about in the news stem from vulnerabilities in unpatched or outdated Windows systems. Migration takes hard work and a lot of cooperation between departments, but it beats the alternative.
James Ford, chief evangelist and commercial lead, Intact