A new era of Distributed Denial of Service (DDoS) attacks has arrived. In 2018 DDoS attacks broke the terabit barrier, and have become even more frequent and sophisticated (or vicious) as they now commonly combine several different attack techniques that vary — both in time and geographically — to maximize impact.

Even the giants of today’s platform economy, like Amazon, are not immune or safe. And, when the new generation of DDoS attacks hit, telecom and cloud service providers, large digital enterprises and their customers feel that impact as they are left without services, sometimes for hours.
DDoS threats are no longer just external either (i.e., coming from other networks). Due to the pervasiveness of IP technology as a lingua franca for all communications today, any IP device able to reach other IP destinations in the network can effectively become a threat factor.
The introduction of an all-IP networking environment resulted in the super large “surface attack area” (or expanded security perimeter, as experts call it). Expansion of the internet of things (IoT) space, with millions of IoT devices now residing in our homes and enterprises, sometimes with less-than-ideal security settings, serves as a base for malicious players to explore in order to create botnets.
Botnets are an army of remote-controlled devices, ready to serve their malicious operators in the latest generation of DDoS attacks — dubbed command-and-control (C&C) attacks. DDoS threats are everywhere and can realize themselves as “inbound” attacks, coming from the internet at large, or “outbound,” coming from within service providers networks. These attacks not only put an organization’s own networks, and the internet, in jeopardy, but also potentially leave service providers exposed (legally) for the harm their users may bring to other users and networks.
But what can be done about it?
Historically, security professionals have relied on the use of dedicated hardware probes and Deep Packet Inspection (DPI) technology to detect network anomalies that could be the result of imminent DDoS attacks. From there, these anomalies would be manually investigated, and traffic flows (typically identified by IP “quintuplets” — i.e. their source IP address, destination IP address, source and destination ports, and protocol type) would be subject to a number of router-based mitigation strategies. These strategies encompassed blackholing (i.e. sending all “quintuplet” traffic to unreachable network destinations), partial traffic filtering using BGP Flowspec, and diversion of traffic to scrubbing centers (where the traffic would be “cleaned” and sent back to the destination IP addresses). DPI technology helped mitigate attacks initially but it does not scale economically with the growth of multi-terabit networks.
While traffic scrubbing showed to be the most effective of those three approaches, it has significant costs due to the backhauling of all traffic to and from scrubbing centers, which adds to the overall latency and total cost of ownership because of the exponentially rising traffic volumes (and a proportional CAPEX increase of scrubbing center costs). All of these costs have made the scrubbing approach not cost effective for the largest, volumetric DDoS attacks, and therefore not fit for the future.
Luckily, a few technological developments have come to the rescue.
First, networks today are huge repositories of data, a fact formally recognized by the International Telecommunications Union in their dedicated work on big data-driven networking – seen as a foundation for future networks.
Secondly, IP routers – elements that control, process, and forward all traffic as IP packets within service providers’ networks and across the internet – have become much more capable. As a result, they can generate real-time telemetry data about the traffic they transport, and some have increased processing capabilities that can be leveraged for security. The new generation of more capable routers can also perform additional, on-the-fly “payload inspection,” in order to allow for more precise DDoS detection (since DDoS traffic often contains very specific traffic signatures for specific attacks).
Thirdly, real-time network analytics has evolved to incorporate heuristics – or knowledge-based algorithms to monitor the volume and composition of traffic protocols that are most commonly used in DDoS attacks in order to detect anomalies in real-time, triggering immediate actions and agile mitigation scenarios. Big data collected from the network (e.g., flow-based information, BGP routing information, streaming telemetry, mirrored traffic samples, etc.) can be processed in real-time. This is due to increased processing capabilities of hardware (servers), and because of the progress made in software engineering for analytics platforms, where machine learning (ML) rules are enhancing the process of DDoS detection and paving the way for future uses of artificial and augmented intelligence.
Because of these factors, it was ‘only logical’ to arrive at the next paradigm for DDoS security — closed-loop automation for DDoS protection, which establishes a tight integration between analytics and the network itself.
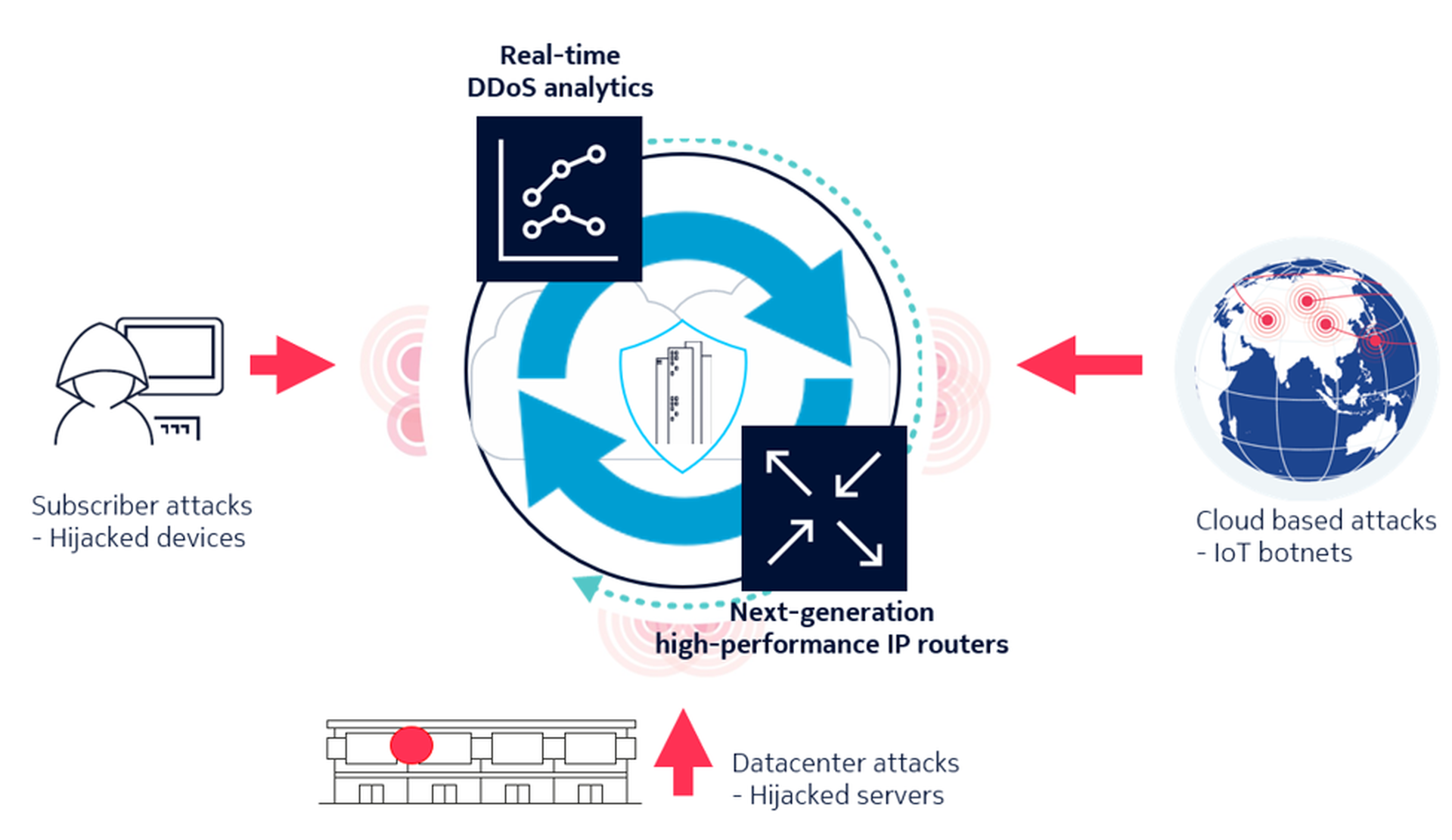
Figure 1. Closed-loop automation for DDoS security between the analytics and the network
In this approach, real-time DDoS detection is made much faster and better by using larger data sets and better DDoS intelligence. Mitigation becomes almost immediate as the analytical platform can instruct routers in real-time (by applying ad-hoc or permanent filters) to take corrective and mitigative actions, filtering out only the malicious traffic without affecting the network or users.
As a result, service providers can leverage advanced DDoS intelligence and analytics with intrinsic, network-based capabilities to monitor, recognize and neutralize the most complex and volume-intensive threats and attacks as they are happening, while leaving their network and users intact and their services running.
Effectively, this approach using network-based DDoS security is allowing unprecedented efficacy and 360-degree protection against outbound and inbound network-level DDoS attacks and represents a major shift in security automation towards the self-defending network.
And that’s good – in the world in which DDoS attacks have become daily news, this future-proof approach can now relegate it to the past.
By: Kevin Macaluso, VP & General Manager of Deepfield, Nokia



