In the best-selling series of pop-economic books Freakonomics, a ‘rogue’ economist Stephen Levitt partners with veteran journalist Stephen Dubner to uncover the hidden side of everything. Posing such provocative questions as ‘why do drug dealers still live with their moms?’ and ‘how are the Ku Klux Klan like a group of real estate agents?’ the two set about to examine a wide swath of social issues through the lens of behavioral economics, the discipline of psychology that studies how economic decisions are made with the recognition that people do not always make rational decisions.
At its core, behavioral economics is driven by incentives, the levers which policy makers, parents of young children, or in this case, security leaders, push or pull to influence a desired behavior. Will taxing carbon motivate corporations to pollute less? Will taking away your kids iPad compel them to do their chores? Does restricting an employee’s access to certain websites or devices reduce the risk of a security breach?
The value of ‘thinking like a Freak’ isn’t necessarily in definitively answering these types of questions but rather in challenging the conventional wisdom through a combination of quantitative analysis and the quest to understand the often unpredictable power that incentives have in shaping human behavior.
The Unforeseen Security Consequences of Bitcoin
One need look no further for an object lesson in the law of unintended consequences than the rise of cryptocurrencies in general and Bitcoin specifically. It’s often forgotten that Bitcoin was initially designed as an incentive lever for the blockchain itself as a means to encourage early community stakeholders to perform the critical Proof of Work calculations required to validate and maintain the blockchain itself.
Few if any of the very first Bitcoin miners were committing time and computing resources to solving these calculations as a speculative investment vehicle. Rather their incentive was rooted in the act of participation itself. Of course, for the blockchain to mature and scale beyond its initial, tightknit community, another incentive was required – a profit motive that would reward individual contributors for validating these Proof of Work transactions and ensuring the integrity of the blockchain (for more background, check out Hugo Nguyen’s excellent four-part series on Bitcoin Fundamentals here).
As Levitt and Dubner write, “economists love incentives....The typical economist believes the world has not yet invented a problem that he cannot fix if given a free hand to design the proper incentive scheme.” Yet, as any economist who has witnessed their theories being implemented in the real world can attest: beware the impact of unintended consequences.
As far as incentive schemes go, Bitcoin has proven itself wildly successful. However, as the primary incentive shifted from participation to profits, human behavior naturally took hold as participants quickly discovered workarounds for mining Bitcoin -- from simply adding more nodes to perform the proof of work in the early years to building massive mining farms close to cheap energy sources which have consequently become a significant environmental threat that few could have predicted when Bitcoin first came to market.
Of course for threat actors, Bitcoin was a true game changer. Its premise of anonymity fundamentally disrupted the threat landscape, providing criminals with both a mechanism to monetize their efforts while also enabling them to effectively launder and hide their ill-gotten gains. From the perspective of a malware author, Bitcoin also offered up a new type of incentive, one that would directly result in the creation and propagation of an entirely new breed of malware threats.
From Cryptomining to Ransomware: Weighing the Calculus of Risk v. Reward
Every criminal, be they a small time street hustler or the head of a crime syndicate, has one thing in common: they must weigh the risk versus reward of their actions and make a determination as to whether the reward is worth the risk. Cybercriminals are hardly different in this regard.
Trade-offs are an essential component of economic decision making. Security leaders are constantly weighing trade-offs, having to balance their organization’s overall security posture with the needs and user experience of their employees and customers. Likewise, threat actors also are making similar trade-offs between risk, effort, and rewards.
This dynamic is perhaps best illustrated by looking at the relationship between two very different breeds of malware: cryptojacking and ransomware. As shown in the chart below, ransomware in 2017 represented the fastest growing type of malware accounting for a third of all malware families.
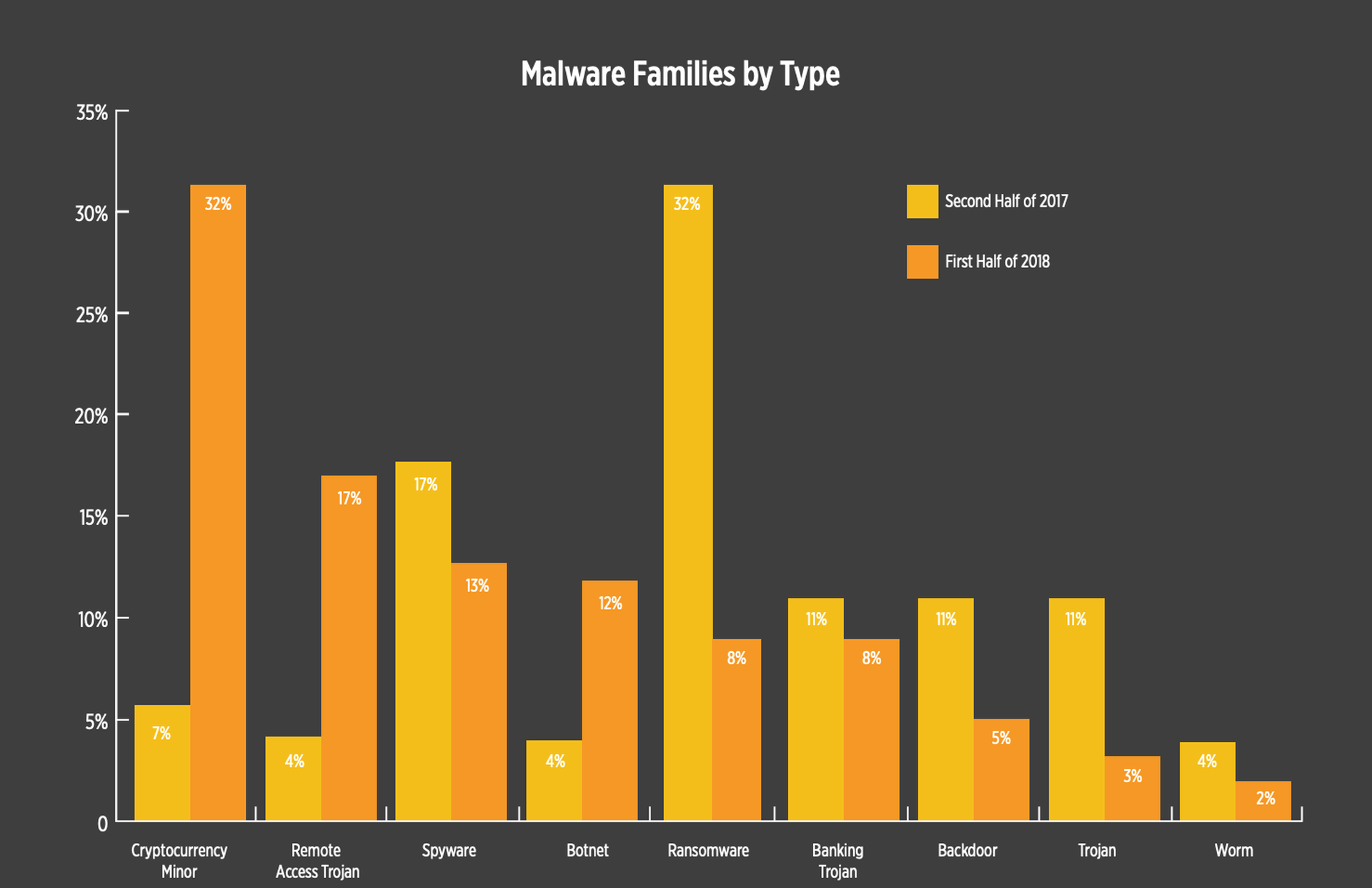
Source: https://lp.skyboxsecurity.com/WICD-2018-07-Report-VT-Trends-MY_03Asset.html
However, in 2018, cryptojacking and ransomware essentially traded places, with incidents of cryptojacking outpacing ransomware by a ratio of four to one. The surge in value of Bitcoin and Monero are the most likely explanation for this strategy shift, while it is also likely that the anti-ransomware measures that companies took after 2017 made it more challenging for ransomware to succeed.
Beyond these market factors, there is also likely an important behavioral factor at work: the risk of getting caught. While Bitcoin is perceived as being anonymous by many, criminals recognize that these payments are by design part of a permanent ledger and can ultimately be traced to an individual. On the other hand, cryptojacking does little more than slow down a victim’s computer, making it far less likely that a perpetrator will face any real consequences. To put in terms any criminal would understand, the difference between the two is like stealing the change from the glove box of an unlocked car versus robbing a bank.
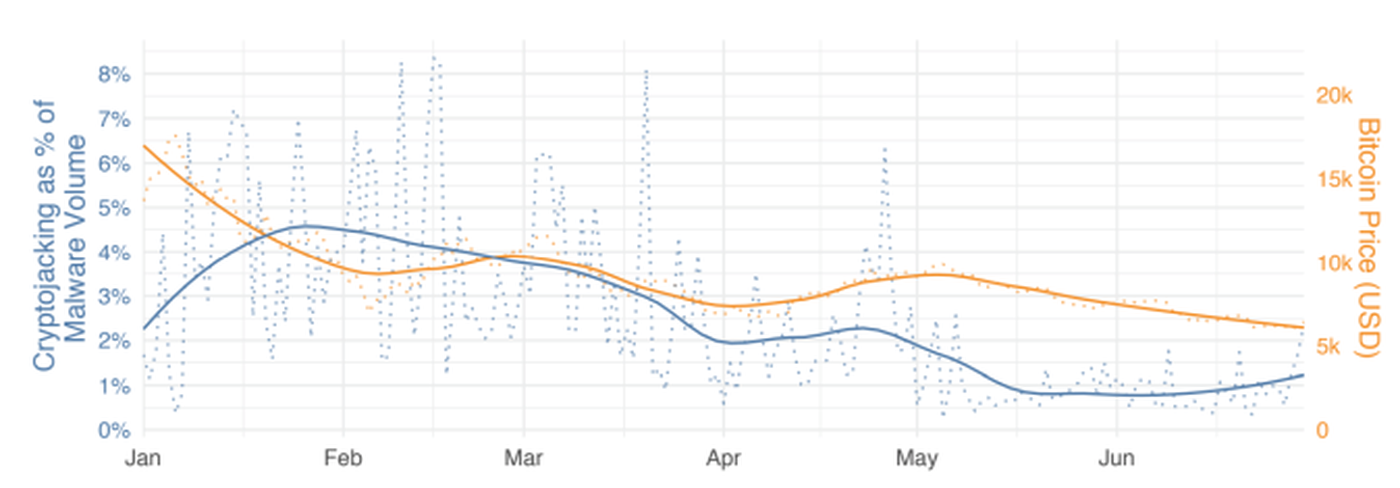
As the price of Bitcoin dropped, so did the incidents of cryptojacking. Source: https://www.fortinet.com/fortiguard/threat-intelligence/threat-research.html
In the realm of cybersecurity, it’s instructive to remember that most security issues are not solely technology problems, they’re also people problems. To prepare for the next generation of unknown security threats, we as security leaders need to not only understand how the latest technologies are driving new threats but also should seek to question and deconstruct the underlying motivations of threat actors and how they might impact the behavior of the constituents we are tasked with protecting. And perhaps most challenging of all, we must also attempt to divine the unintended consequences of these decisions.



