This space has seen tremendous development as endpoint security moves from a single point of protection to safeguarding many endpoints across multiple networks, says Katelyn Dunn.
Today’s security tools must meet the demands of an ever-growing cyber landscape and evolving threats coupled with expansive network infrastructures and hybrid architectures.
The journey from the single point of protection to safeguarding many endpoints across multiple networks has led to tremendous development in this space, stemming from developments in antivirus solutions to machine learning tools and threat hunting capabilities. The latest set of endpoint solutions more recently have even incorporated chatbots to make it easier for analysts to understand events.
In this year’s look at endpoint security tools, the SC Labs team found the trend toward cloud management systems continued, nearly making obsolete the once standard on-prem server.
The ability of cloud solutions to share information quickly across all end users with interconnected dashboards linking to a threat intelligence engine inside their private cloud environment keeps a tool’s users abreast of attacks found by others and realizes a complete contextual picture of an attack. Centrally managed offerings also take some of the workload off the shoulders of administrators.
Protecting the endpoint is only a side aspect of protection. What happens when something gets through? The solutions we looked at almost exclusively have some sort of endpoint detection and response (EDR) capability to help security teams understand in the entry point of an attack, what happened after entry and where the attack spread. The storyboarding feature we saw trickling into many of these products takes EDR a step further. It is one thing to know where an attack came from, but what about the bigger picture? For remediation and rollback purposes, it is crucial to see the attack steps and the changes made to a system. A complete picture removes the guesswork from the process and even lends to automating process like patch remediation.
If an attack has infected hundreds of endpoints then removing or sanitizing a few files might not be such a laborious process, but if a large portion of a network is infected, that quickly cloud become a nightmare. Undoing the damage already would be a mostly manual process as well as time consuming. Such widespread infiltration would make it difficult, if not impossible, to isolate all those sections to prevent further spread and damage. But real-time response makes threat mitigation straightforward since security teams can connect to a command-line interface and kill processes and remove files. This is an important tool in remediating machines in a different locations. A one-click isolation button included in one product greatly minimized time-to-action following detection.
We are nowhere close to seeing a single tool providing the security needed across an organization. The threats are just too advanced, too persistent and too destructive. Multiple layers of protection and products capable of communicating and working cohesively are the best defense against those threats. Detection, prevention and remediation, too, are important.
As security teams struggle to keep up with workload demands stemming from the unrelenting threats testing our defenses at alarmingly persistent rates, features like storyboarding functionality take the guesswork out of following an attack vector from pre-execution to breach and subsequent remediation. The ability to automatically piece together an incident’s story found in many of these endpoint tools opens the door to further automation and offers a great deal of contextual understanding and insight into what occurred. Analysts of all skill levels also can use this valuable tool to view other, potentially related detections on a network.
Endpoint security
Protecting all facets of an infrastructure has grown increasingly critical to a successful security posture. The shift from on-premises to cloud and hybrid environments have underscored that criticality, putting greater demands on security tools. That’s why SC Labs revisited the endpoint protection space this month.
Moving from the idea of single-point protection solutions to having multiple points across several networks, has provoked/spawned considerable innovation in endpoint protection, especially with this most recent round of products. The continued evolution of these tools is evident as they add attractive features – from storyboarding functionality and machine learning integration to chatbots.
That endpoint protection and endpoint detection and response have converged in these tools should come as no surprise − they are natural allies. Most offer contextual analysis of the start to finish attack process with patch remediation and automated responses to bolsters analysts’ ability to efficiently perform their duties. These products can even serve as good teaching tools for junior analysts, offering a full picture of a breach’s impact and providing automated workflows and remediation assistance to guide them in their next steps. By incorporating these tools, organizations will not only protect their endpoints but get the most out of their existing security tools.
Pick of the litter
Endgame impressed us with the innovation built into its endpoint security product. The chatbot Artemis and all-around intuitive functionality simplifies the process of following a threat through to remediation. The ease of use and success in detecting threats makes this product an SC Labs Best Buy.
Cybereason’s Cyber Defense Platform 19’s lightweight agent and proprietary detection engine that delivers the full attack story and contextual visibility without being overly technical, made it the SC Labs Recommended product this month.
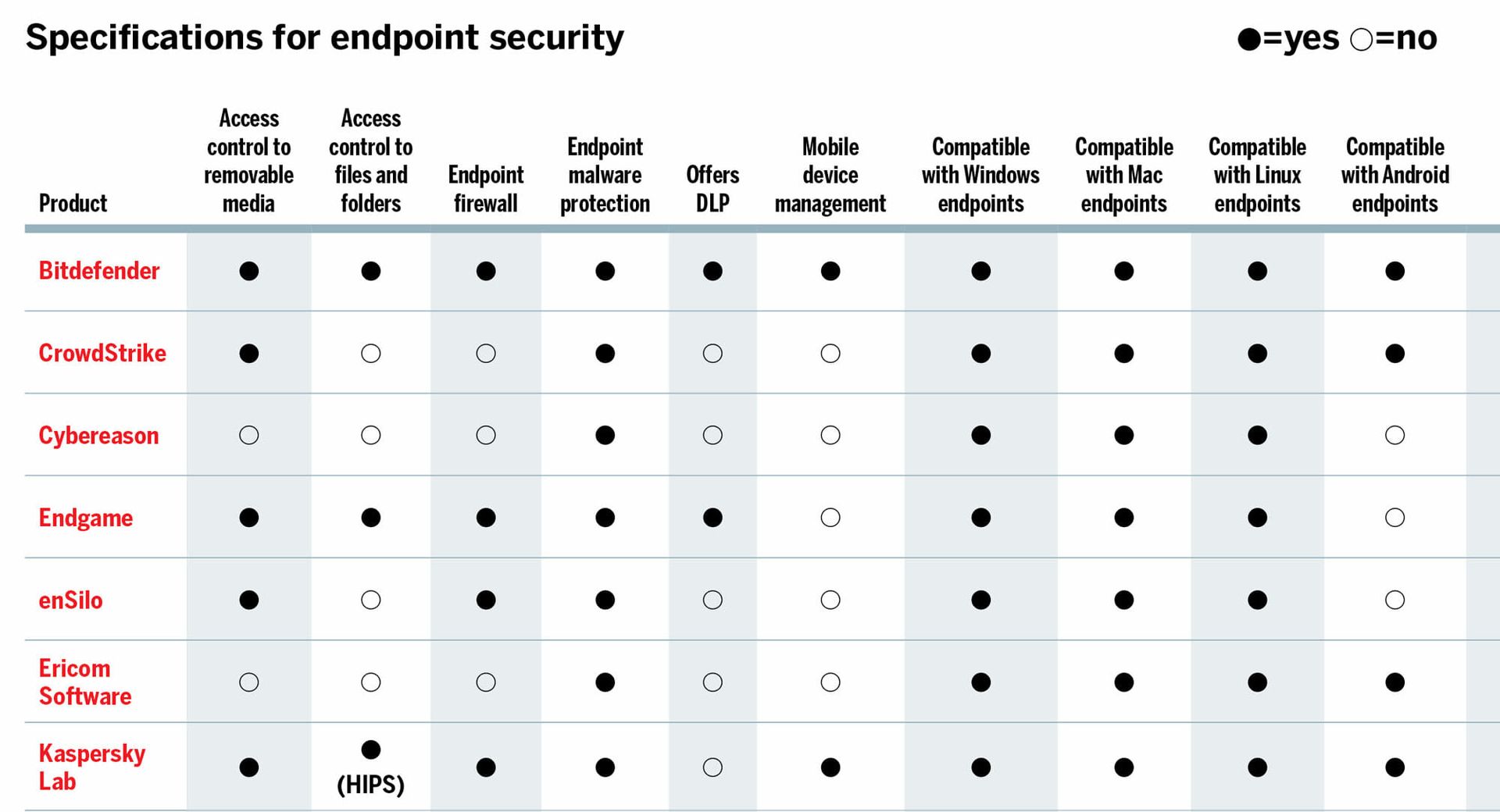
Click on the matrix below to see all the specs for the July products.