Cybersecurity decision-makers more often turn to purple teaming as the better approach for vetting tools tactics and procedures, ultimately providing the information needed to steer investments.
According to results of a new survey conducted by CyberRisk Alliance Business Intelligence and sponsored by PlexTrac, purple teaming has become a more effective alternative to traditional penetration testing. Some 66% of the 315 IT and cybersecurity decision-makers and influencers surveyed were “very satisfied” with purple teaming and another 32% “somewhat satisfied,” while 66% said they were “very likely” to budget for purple teaming solutions in the coming year. Another 25% were “somewhat” or “slightly likely” to do the same.
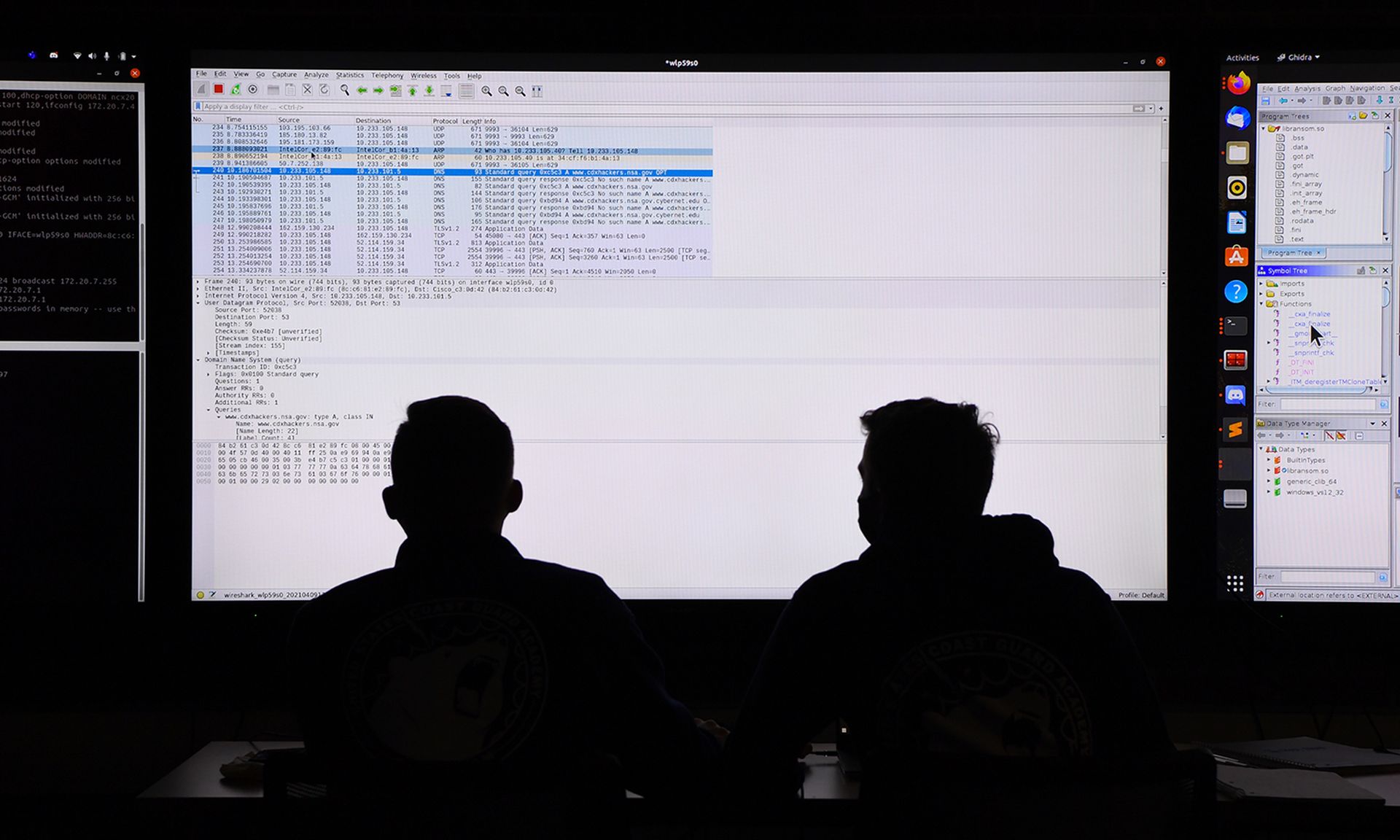
The trend towards purple teaming has taken several years to materialize as for decades, organizations gauged their cybersecurity readiness with traditional penetration testing exercises involving red teams versus blue teams. Red teams are tasked with mimicking the known tactics, techniques and procedures of a threat actor to launch an attack against an organization. It’s then up to the blue team to hold off such an attack. A red team wins points to one or more vulnerabilities that must be addressed. Like traditional war games, no actual harm takes place. Instead, the exercises help the teams find and fix weaknesses in current security controls.
Such penetration testing exercises are seen as safe, competitive programs to discover flaws and establish remediations before an actual malicious attacker can break in and spy, steal or extort. But just as threats continue to evolve, so too are these color-coordinated attack emulations to validate what’s working — and what’s not. Pen testing teams are now starting to come together to create purple teaming, which is built on a more collaborative model. With purple teaming, attack modes and defenses are pre-determined. Both red and blue team members work alongside one another to test controls in realtime and together learn how an attacker can most likely gain illegal access by what works — and what doesn’t.
CyberRisk Alliance studied this trend this past September, surveying participants about their experiences with specific types of penetration testing models known as adversarial attack simulations and emulations (AASEs). When asked if their organization engaged in some type of AASE, almost half (45%) said they had conducted such exercises, whether penetration testing, purple teaming, or both.
Among the key findings from the CRA surey:
- Purple teams have gained popularity, with more than 1 in 4 penetration testers having evaluated or trialed a purple teaming solution or approach and another one-third intending to give purple teaming a try in the coming year.
- The tech, industrial and financial services sectors were most experienced with purple teaming and use results to help shape their cybersecurity strategies, rather than just vetting current security controls.
- Even with a more strategic emphasis, almost 9 out of 10 purple team users found the exercises “very effective” in defending their organizations against ransomware and other advanced attacks.
- While both types of AASE users expected a reduction in future attacks because of exercises, purple teamers were more likely (88%) to believe their cybersecurity defenses had improved, compared with those using only penetration testing (52%). Their programs appeared to be more strategic, using results to advocate for more resources, talent, and tools than those who don’t conduct purple teaming exercises.

Click here to access the full report, "The Power of Purple Teaming."
The CRA survey also found that most purple teaming users primarily built exercises with a specialized purple teaming platform (89%) or breach and attack simulation (BAS) platform (80%) versus 68% of BAS platform usage by red-team blue team users.
While both types of AASE users saw improvements in their security team performance as the top outcome, purple teams were more likely to gain management support for cybersecurity investments and secure more cybersecurity resources. Traditional penetration testers, on the other hand, better understood their biggest threats and performance of current security controls.