Vulnerability management tools can help organizations identify, assess, resolve, and report security vulnerabilities in their IT systems and software applications.
In the last few years, however, vulnerability management (or VM) has proven especially challenging for security teams to get right. 2021 was a record year for vulnerabilities, with the number of new Common Vulnerabilities and Exposures (CVEs) exceeding 20,000 for the first time ever. 2022 isn’t looking any better: As of July, roughly 13,800 vulnerabilities have been logged already – an average of 68 per day.
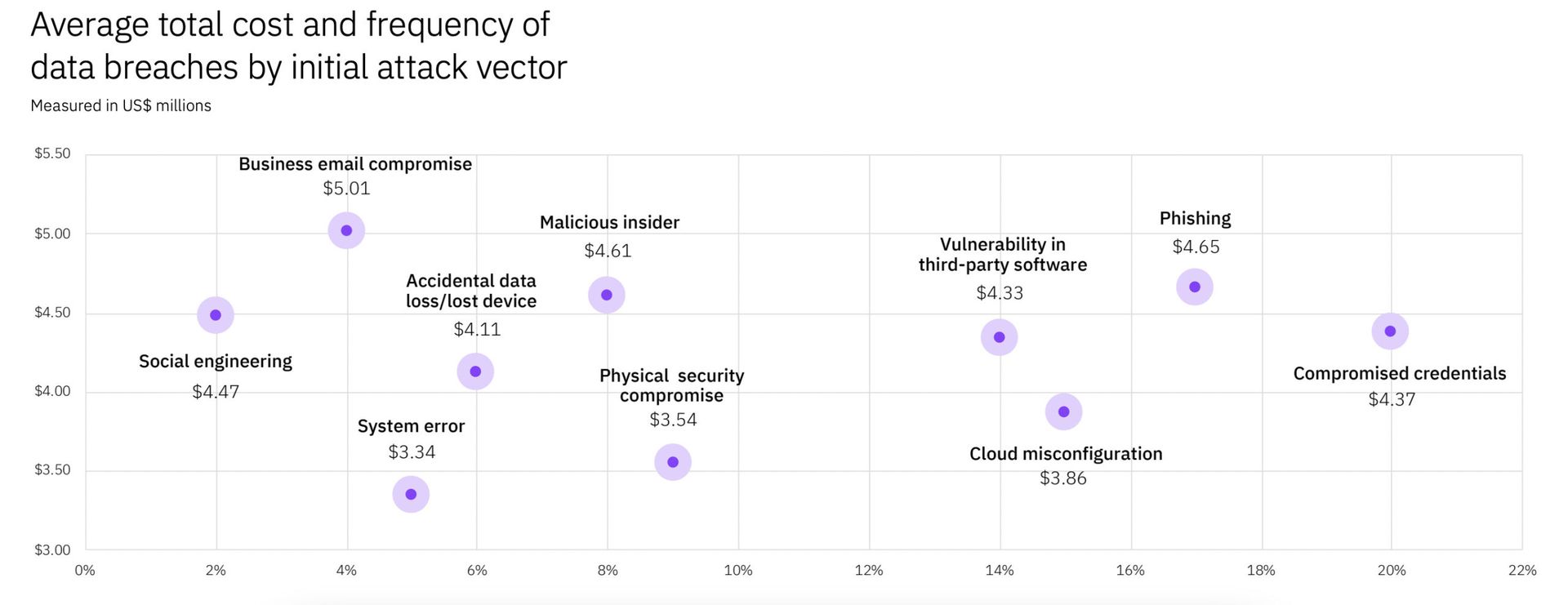
Given the numbers, it’s not surprising that organizations with poor VM are paying a high price. The average cost of a data breach rose nearly 10% between 2021 and 2022, from $3.86 million to $4.24 million. The same study found that the pandemic and shift to remote work environments only made matters worse: In breaches where remote work was a factor, the average cost was $1.07 million higher than breaches involving non-remote work settings. Additionally, employers with predominantly remote workforces took, on average, 58 days longer to contain breaches than their non-remote counterparts did.
Vulnerability management challenges
Clearly, many organizations are struggling to implement effective vulnerability management. This could be due to any number of reasons, but below are a few of the more common culprits.
#1: Tool overload. Many organizations address their security concerns by acquiring a new tool for every concern: threat remediation, asset management, vulnerability detection and more. This creates a varied tool box that looks good from the outside. But, in many cases, these tools do not integrate well and create security silos -- preventing organizations from taking a more cohesive security posture.
#2: Alert overload. A common complaint from organizations is the overwhelming volume of security alerts flagged by SIEMs. A large portion of these alerts are false positives that the system believes are malicious, but which are in fact benign. Security teams that are victims of alert-overload are forced into spending an exorbitant amount of time discerning false flags from genuine vulnerabilities -- time that could be better spent on remediation.
#3: Skills shortage: Organizations are struggling to meet modern cyber security needs in a rapidly changing digital landscape. There are lapses in cybersecurity skills and experience in both the job market and the workplace. In a recent survey of 1,200 security professionals, 80% of respondents attributed one or more breaches in their organization to insufficient cybersecurity skills or awareness. Without sufficient personnel, vulnerabilities are going to pile up and overwhelm existing security teams.
How automated vulnerability remediation can help
Lately, more organizations are finding success by introducing automated patching and remediation capabilities. Here are a few reasons why:
#1: Focus on what matters. Automated management and remediation can remove a huge portion of routine, low-risk vulnerabilities -- allowing security to focus on dealing with critical vulnerabilities that deserve more hands-on treatment. Effective, automated VM solutions continuously scan software vulnerabilities and check findings against a comprehensive signature database that includes known CVEs and NVD threat data, and then assigns a vulnerability risk score that helps security distinguish between low-risk and high-risk assets.
#2: Shared context and collaboration. The pandemic’s impact has resulted in a highly distributed workforce, complicating efforts to centralize coordination and communication among security teams. The latest breed of automated VM solutions are solving this with context-build features like automatic asset discovery, threat intel analysis, and single app workflows to ensure that everyone is working from the same set of data.
#3: Simplifying security. With many organizations already in possession of 50 or more security tools, the last thing they need is one more point solution that doesn’t integrate with the rest of the bunch. It’s a good idea to work with a vendor who can unify automated VM capabilities in a single end-to-end package. For example, Qualys’s VMDR 2.0 integrates with configuration management databases (CMDB) and patch management solutions to quickly discover, prioritize, and automatically remediate vulnerabilities at-scale to reduce risk.




