In a deceptively large leak of personal information, ransomware group ALPHV launched a website on the clear web for employees and guests of an American hotel to see if ALPHV might leak their data.
The hotel acknowledged a cybersecurity event in an email to SC Media.
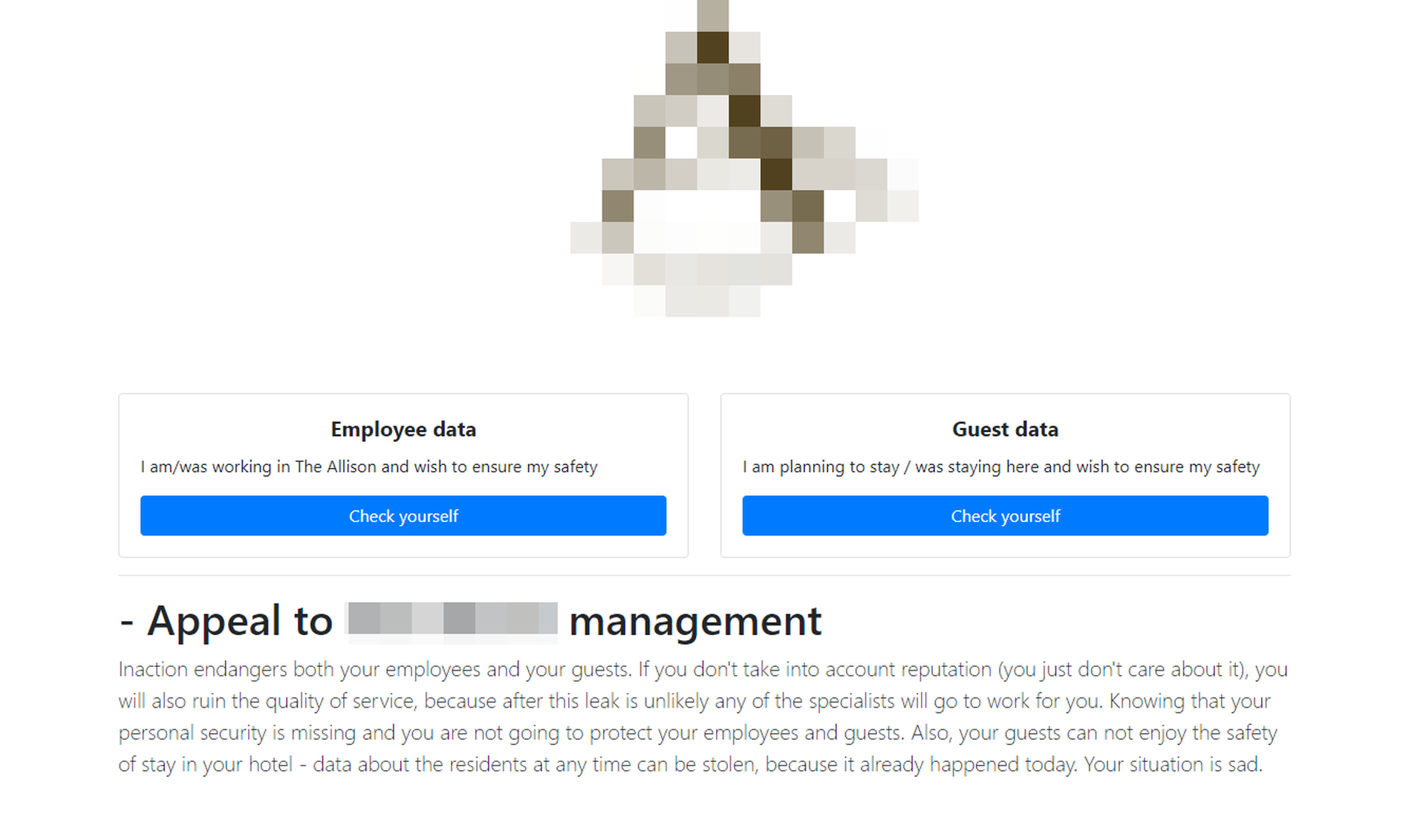
ALPHV, which is also referred to as BlackCat or AlphaCat, designed the site to appear like a breach disclosure site. At the top of the page are two buttons labeled "check yourself," one under a banner reading "Employee Data" with the text "I was/am working at [the hotel] and wish to ensure my safety", and another with a corresponding message for guests. The domain for the site, the same as the hotel's but with the ".com" replaced by a ".xyz", was registered on May 31. It received some Twitter notice on Tuesday, but was taken down after 12 p.m. Eastern.
Ransomware expert Brett Callow of Emsisoft described the site as "kind of like a bad guy version of HaveIBeenPwned."
One difference between HaveIBeenPwned and the ALPHV site: where HaveIBeenPwned is anonymized, all data on the criminal site was displayed onsite, meaning guest names, dates and expenditures, as well as detailed employee personal data were available for all to see. The employee data included email addresses, birthdays and social security numbers. SC Media has opted not to release the name of the hotel to prevent the spread of that personal information.
The purpose of the site is less to be socially responsible and more to place pressure on the hotel to pay, said Callow.
"The hope is that all the employees and all of the customers are going to reach back to the hotel to tell them tell them they do not want their personal information to be released online," he said. "The secondary hope may be to increases the risk of class actions, or at least to make sure the company's insurance thinks there may be an increased risk of a costly class action, which again could sway their decision as to whether or not to pay."
ALPHV tried to drill that point home on its site, including an "Appeal to [the hotel] management]" on the page with the opening line "Inaction endangers both your employees and your guests."
Site may backfire on ALPHV ransomware group
Whether the strategy would work is uncertain, said Kurtis Minder, chief executive of Groupsense, a firm with large ransomware negotiating practice. For one, he said, the gambit assumes people would find the xyz site.
"Are they paying for SEO?" he joked.
The bigger problem, he said, was that the action may actually reduce the value of a ransom. Competent negotiators would argue that creating lawsuits and damaging the brand drains the very bank account ALPHV wants a withdrawal from. Many firms want to pay to prevent embarrassment from employees or clients, something ALPHV no longer is able to use as leverage, having already embarrassed them.
In an email, the director of finance of the hotel said the hotel was aware of the site and had been breached. The hotel was contacting affected parties to offer credit and identity monitoring, and had engaged third-party cybersecurity services.
"The security of the information in our care is one of our highest priorities, and we have already taken important steps to help prevent this from happening again," the director wrote.