Healthcare cybersecurity leaders are being urged to review the IOCs and the recommended proactive measures for defending against BlackCat and LockBit 3.0 ransomware variants given the continued targeting of healthcare environments.
The Department of Health and Human Services Cybersecurity Coordination Center issued two new analyst notes late Dec. 12, which join four previous ransomware alerts issued in the last month on Venus, Hive, Lorenz, and Royal threats.
The uptick in ransomware insights follows the weeks-long outages at CommonSpirit Health and several global providers tied to ransomware. As seen with the lengthy outage at the New Zealand Waikato District Health Board last year, well-practiced preparedness plans and a clear understanding of response priorities are crucial to successful ransomware response.
For the BlackCat and LockBit 3.0 threats in particular, the highly customizable tactics and favored healthcare targeting should serve as a warning to finetune incident response plans and proactive measures.
BlackCat: Extensive relationships compounds reach
First observed in November 2021, BlackCat, aka Noberus and ALPHV, is known as “exceptionally capable” and likely operated by threat actors with significant experience with cybercrime. The variant is part of what HC3 calls “one of the most sophisticated Ransomware-as-a-service (RaaS) operations in the global cybercriminal ecosystem.”
The human-operated BlackCat variant likely succeeded REvil, Darkside and BlackMatter operators, and the group is also connected to FIN7 or Carbon Spider. ReVil notoriously targeted the healthcare sector, particularly those working toward the COVID-19 response.
For HC3, the concern with BlackCat is that its functions are technically superior to other RaaS variants, which enables a wider range of corporate environments. In fact, the variant is highly customizable and heavily relies on internally developed capabilities that its operators constantly develop and update.
Among the “many advanced technical features,” BlackCat is an adaptable malware able “to use several different encryption routines, self-propagate.” The variant also renders “hypervisors ineffective to frustrate analysis.” HC3 notes BlackCat is “one of the more adaptable ransomware operations in the world.”
BlackCat offers a range of encryption speeds and abilities through two algorithms and can be configured with domain credentials to distribute the ransomware payload, while terminating processes and Windows services that are meant to protect against encryption.
“BlackCat can also clear the Recycle Bit, connect to a Microsoft cluster and scan for network devices. It also uses the Windows Restart,” according to the alert. The threat is also known to exfiltrate data.
Healthcare is among its targeted industries, with known targets in the pharmaceutical sector. HC3 expects BlackCat to continue exploiting healthcare into the foreseeable future. The sector is urged to take the “threat seriously and apply appropriate defensive and mitigative actions towards protecting their infrastructure from compromise.”
LockBit 3.0: A shift to triple-extortion methods
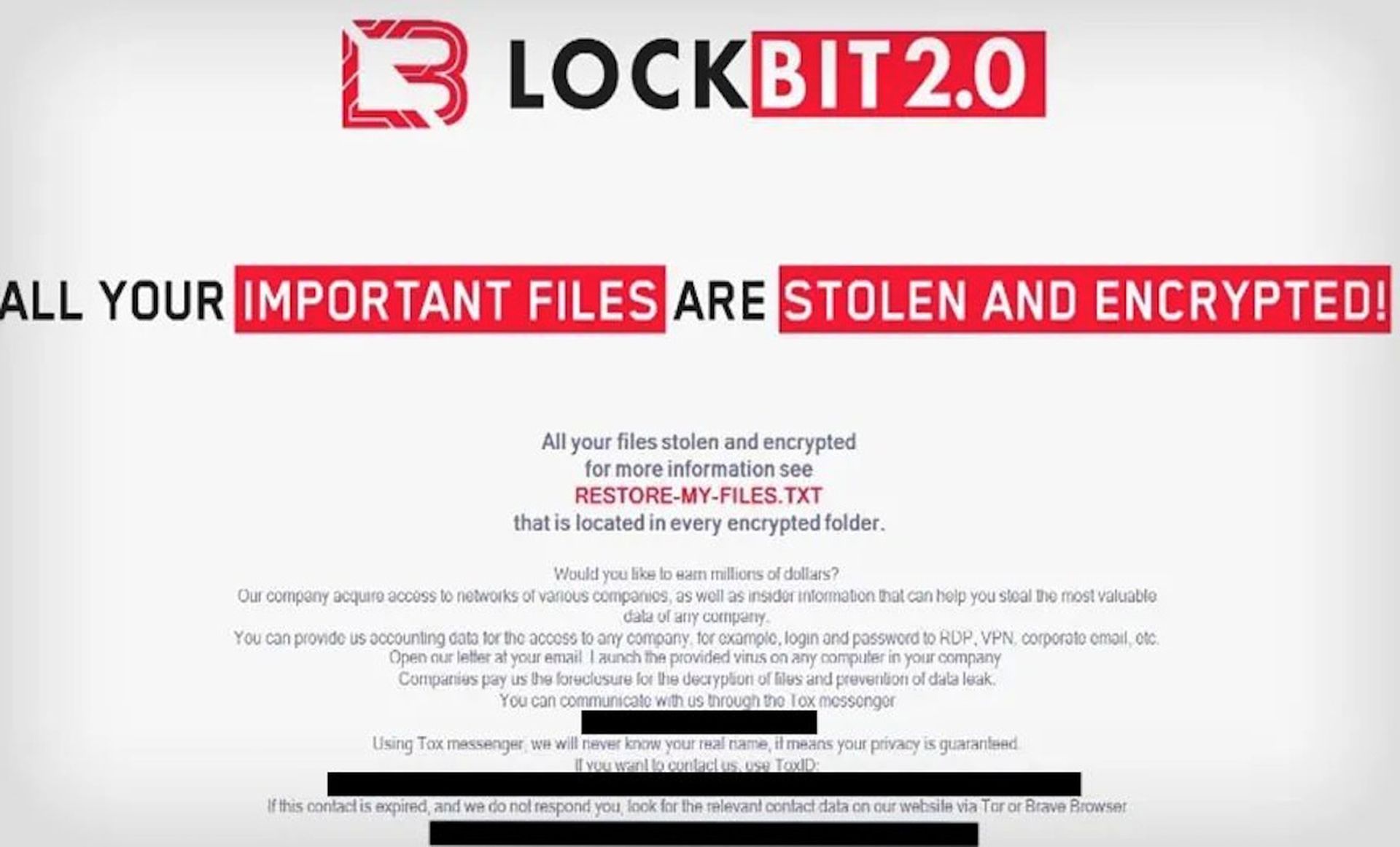
Historically, LockBit leveraged the RaaS model and targeted entities able to pay higher ransoms and leveraged double extortion tactics. The latest version, 3.0, appears to bolster its previously successful extortion tactics by using a triple extortion model that sometimes asks the victim to pay for their sensitive information.
HC3 is aware of multiple LockBit 3.0 attacks against the healthcare and public health sectors.
LockBit 3.0 first emerged six months ago, continuing to operate as a RaaS model and requests for million-dollar ransom payments. As a RaaS model threat, LockBit leverages a range of infection tactics, such as purchasing access to networks and through phishing, brute forcing remote desktop protocol (RDP) accounts, or the exploit of other known vulnerabilities.
The variant has proved challenging for many security researchers as it will sometimes require a unique 32-character password each time it’s launched, which creates “anti-analysis features.”
Analysis has also been burdened by its protection method of leveraging “many undocumented kernel level Windows functions.” It appears the latest variant has simply carried over most of the functions from previously successful versions with additional capabilities, such as the use of features found in another effective variant known as BlackMatter.
Both variants can send the ransom notes to printers on the victim’s network, delete shadow copies, and obtain the operating system of victims. What’s more, LockBit 3.0 also works to obfuscate its presence from the network and also contains worming capabilities to spread without assistance from the operator.
“Once on the network, the ransomware attempts to download command and control (C2) tools such as Cobalt Strike, Metasploit, and Mimikatz,” according to the alert. “Encrypted files can only be unlocked with LockBit’s decryption tool.”
While the group has targeted a host of global entities, the U.S. and healthcare sectors have been heavily victimized by the group. HC3 urges provider organizations to review the provided IOCs and recommended security measures to prevent compromise.



