A report Wednesday in BleepingComputer that an unknown group launched DDoS attacks on Cobalt Strike servers operated by former Conti ransomware gang members — peppering the attacks with anti-Russian rhetoric — prompted security researchers to warn everyday practitioners to button up any Cobalt Strike servers they use for red team operations.
Security researchers were reported saying that whoever executed these attacks targeted at least four Cobalt Strike servers allegedly controlled by former Conti gang members. The Conti gang shut down its operations in May, but former gang members have joined other groups and continue to use the same Cobalt Strike infrastructure to launch other ransomware attacks.
“Red teamers operating Cobalt Strike infrastructure to help identify gaps for organizations need to ensure that they are properly protecting their infrastructure,” said Jerrod Piker, competitive intelligence analyst at Deep Instinct. “DoS/DDoS protection is necessary as evidenced by the recent Conti group attacks, as well as advanced malware prevention, identity protection, and access control. Attackers will always look for and eventually discover low-hanging fruit, so we have to ensure that we make their discovery process as difficult as possible.”
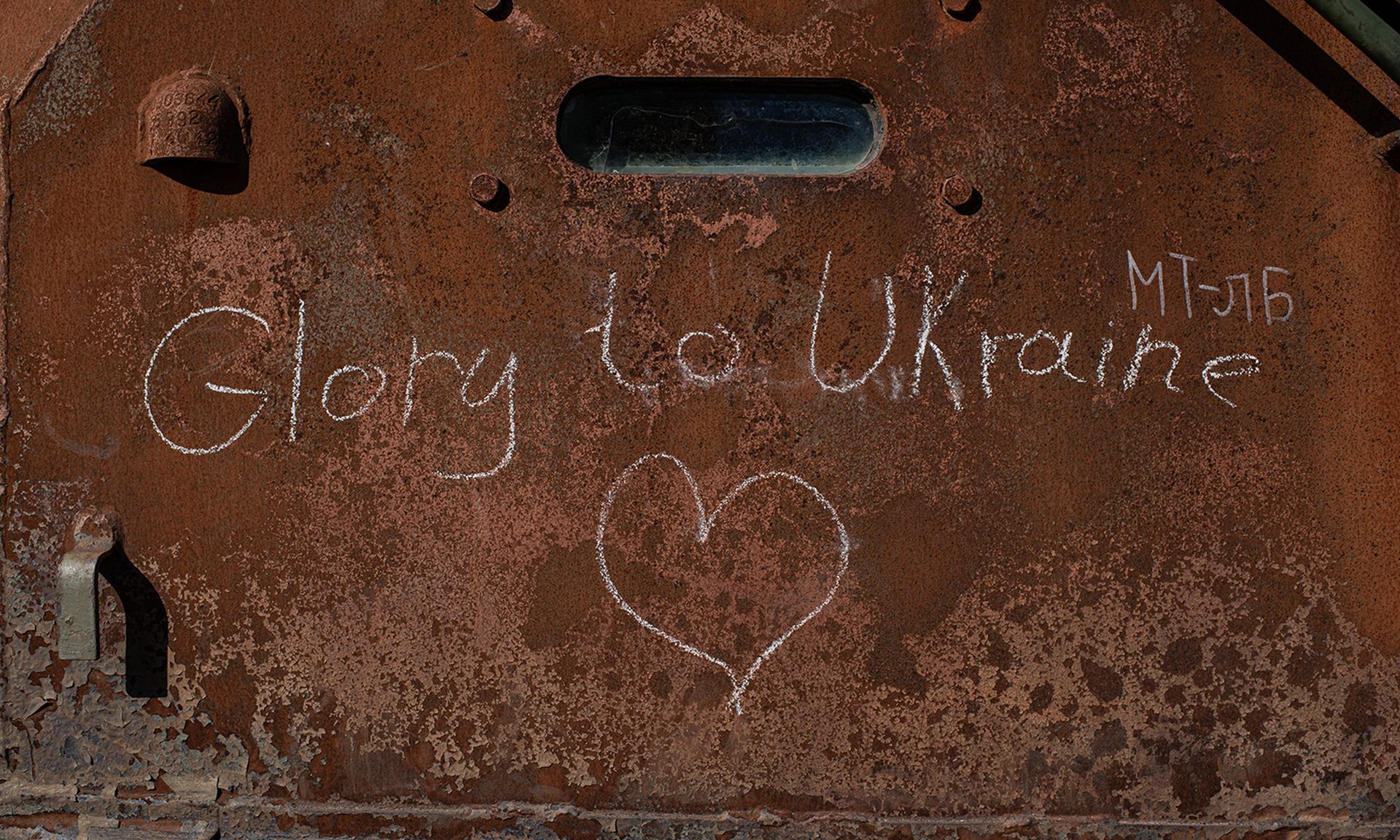
John Bambenek, principal threat hunter at Netenrich, said while we don’t know for sure, this may be purely a Conti problem based on the ongoing conflict in Ukraine.
“Whenever there’s a connection to a major geopolitical event, DDoS and other attacks start taking place in earnest," Bambenek said. "DDoS is the ‘easiest’ form of attack to engage in. That said, anyone running Cobalt Strike legitimately shouldn’t allow the open internet to see their installation.”
Nicole Hoffman, senior cyber threat intelligence analyst at Digital Shadows, said this recent activity reflects a larger trend of hacktivism remaining consistently active and prolific since the Russian invasion of Ukraine. Hoffman said the conflict sparked a resurgence of hacktivism that will likely continue through the end of the year.
“Many groups, such as Killnet and Anonymous, use social media to amplify their messaging and recruit new members,” Hoffman said. “The increase in hacktivist activity should motivate organizations to have defense mechanisms in place to combat or prevent a DDoS attack.”
Deep Instinct’s Piker added that ever since the war began between Russia and Ukraine, we have seen just how much of a role cyber warfare now plays on the modern battlefield. Piker said while it’s unknown if these recent DoS/DDoS attacks on former-Conti Cobalt Strike servers are related to the Russia/Ukraine conflict, it would make sense.
So what does the recent spotlight on cyberwarfare mean for cybersecurity in general?
Piker said it points to the fact that information technology resources have become the most important assets to any organization, be it public or private sector, legitimate or illegal business.
“Nation-states are now recruiting top hacking talent to develop complex APT toolkits that are being sold on the black market, and they are finding their way into the hands of everyday cybercriminals,” Piker said. “So today’s advanced cyber espionage against major national governments and large cybercrime organizations is tomorrow’s WannaCry campaign against private commerce around the globe. What the cybersecurity community must do is rise to the challenge, continue to study and learn from modern APT campaigns, and beef up our toolsets to prevent today’s and tomorrow’s next big global attack.”
In other news related to Conti, Google’s Threat Analysis Group reported today that as the war in Ukraine continues, they have tracked an increased number of financially motivated threat actors targeting Ukraine whose activities seem closely aligned with Russian government-backed attackers.
TAG’s blog post offers details on five different campaigns conducted from April to August 2022 by a threat actor group that potentially overlaps with a group CERT-UA tracks as UAC-0098. TAG assesses that some of threat actors are former Conti gang members.



