The Transportation Security Administration is developing a security directive that would impose a series of new cybersecurity requirements on “high risk” rail and subway entities as well as the aviation sector.
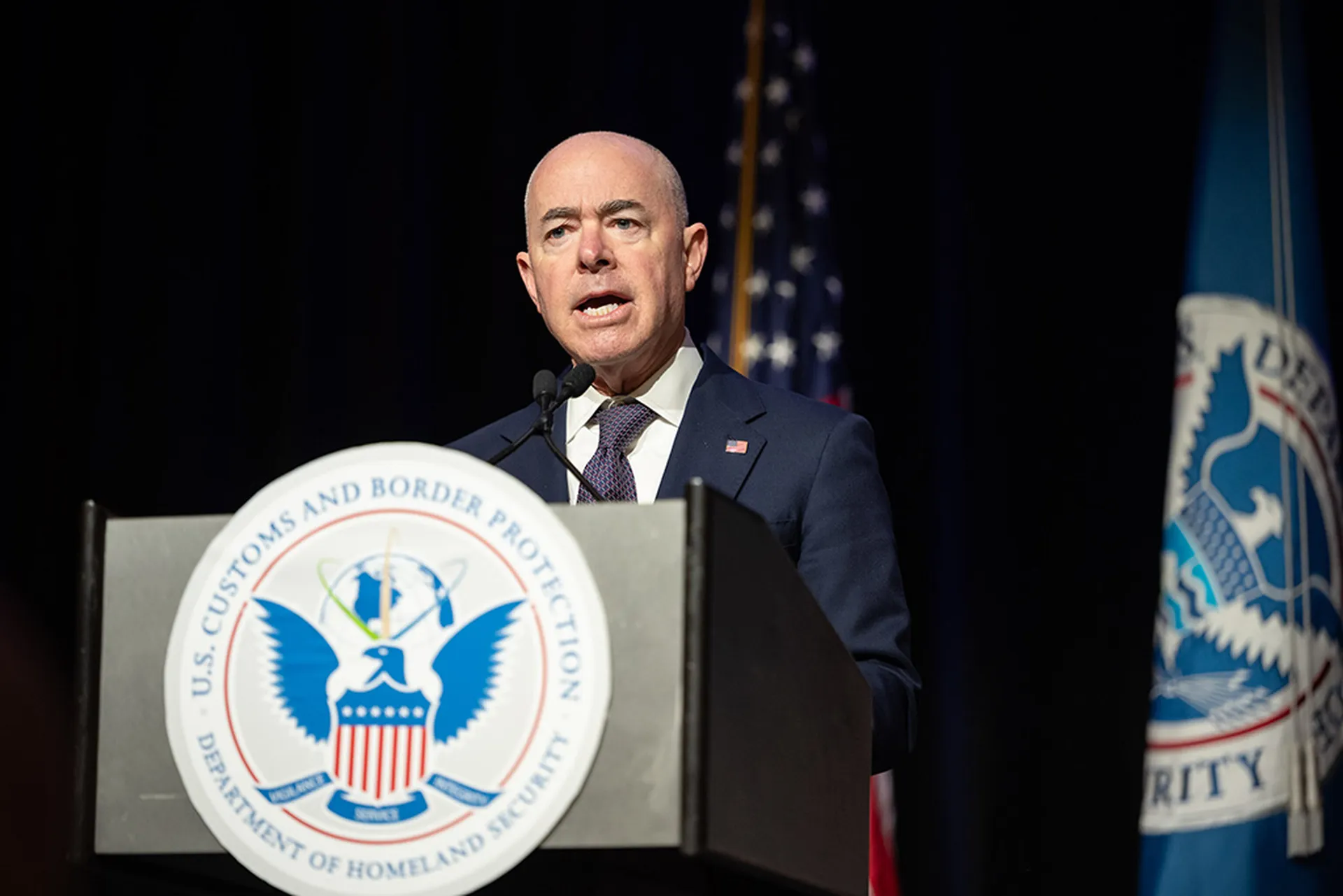
Speaking at the Billington Cybersecurity conference Wednesday, Secretary of Homeland Security Alejandro Mayorkas said that the new directive, expected to be issued later this year, would require railroad and transit systems to report to the government when they’re hacked, designate a point person at their company to interact with the government on cybersecurity issues and develop proactive incident response plans.
Additionally, Mayorkas said that TSA will require critical U.S. airport operators, passenger aircraft operators and cargo aircraft operators to name a cybersecurity coordinator and report incidents to the government.
“These elements – a dedicated point of contact, cyber incident reporting and contingency planning – represent the bare minimum of today’s cybersecurity best practices,” said Mayorkas.
Mayorkas also said that his department will be “coordinating and consulting” with industry as it develops the railway directive and will be issuing a separate set of voluntary standards for lower risk surface transportation entities. TSA will also kick off a rulemaking regulatory process to develop “a longer-term regime to strengthen the cybersecurity and resilience of the transportation sector.”
It marks the second time this year that the TSA has moved to increase cybersecurity regulations on critical infrastructure, after rolling out new mandates on gas and oil pipeline operators earlier this year following the Colonial Pipeline ransomware attack.
It also reflects the Biden’s administration’s increasing comfortable position when it comes to imposing mandatory cybersecurity requirements on the private sector, critical infrastructure and government contractors.
Mayorkas cast the new mandates as part of a larger effort by the Biden administration’s over the past eight months, including efforts to strengthen the authorities and role of the Cybersecurity and Infrastructure Security Agency, remove barriers to interagency and private sector cooperation on cyber issues and increase or expand baseline regulations for critical infrastructure entities to plan ahead and in the immediate aftermath of a cyber attack.
It also coincides with a larger cybersecurity “sprint” launched in September focusing on the transportation sector, with the U.S. Coast Guard updating its cyber strategy outlook for the first time since 2015, deploying cybersecurity specialists to major U.S. ports and more than 2300 maritime entities now being required to report dedicated cyber plans to Coast Guard officials.
The announcements should increase activity and investment around cybersecurity in a market that was already predicting impressive growth over the next decade. The same day Mayorkas made his remarks, Allied Market Research released research indicating that the current $7.72 billion railway cybersecurity market is expected to double by 2030, spurred by increasing volumes of digital attacks, rise in demand for passenger and freight capacity and a glut of pending railway investments and projects around the world that is expected to further grow the already robust transportation sector.
Mayorkas said TSA actions were “laying the foundation for a more resilient aviation and surface transportation sector” and stressed that his department was coordinating and consulting with industry as they develop the mandates.
“We can’t do this alone, As I’ve said before, the Department of Homeland Security is fundamentally a department of partnerships,” he said. “Our ability to execute our critical mission relies on the strengths of our partnerships. We need your expertise, perspective and strategic guidance. We need your partnership.
The news was part of a flurry of government cybersecurity-related news and initiatives to be announced Wednesday. At a conference hosted by the Aspen Institute, Deputy Attorney General Lisa Monaco announced the creation of a national task force focused cryptocurrency enforcement on as well as a civil cyber fraud initiative that would impose “hefty fines” on government contractors that aren’t transparent about cybersecurity breaches.