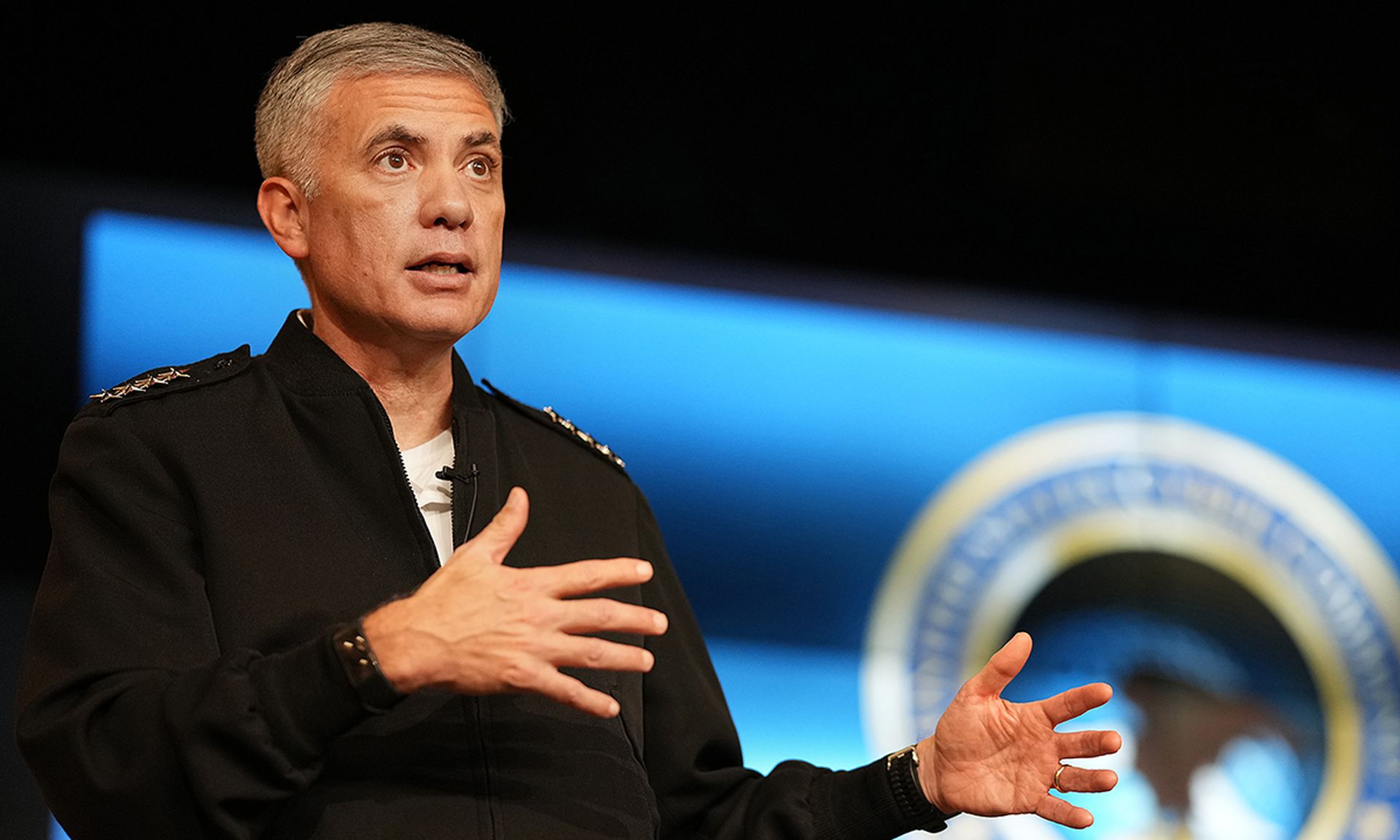
Gen. Paul Nakasone, director of the National Security Agency and U.S. Cyber Command, acknowledged the U.S. had begun "imposing cost" on ransomware groups in an interview with the New York Times, all but explicitly saying that the U.S. was taking offensive hacking operations against criminal groups it had previously reserved for state actors.
It's the most definite language Nakasone has used so far in not-quite-saying the United States is using offensive force to degrade ransomware groups. At the Aspen Forum last month, he said that the U.S. had conducted a "surge" since July, without fully explaining what that meant. It could have meant anything from gathering intelligence to acting on that intelligence.
The Times reports that Nakasone said that they had been gathering intelligence (“The first thing we have to do is to understand the adversary and their insights better than we’ve ever understood them before,” he said), as well as "imposing cost."
"Before, during and since, with a number of elements of our government, we have taken actions and we have imposed costs,” Nakasone told the TImes.
While imposing cost could refer to any element of making the act of crime more difficult, anything from diplomatic solutions to sanctions to kinetic warfare, the implication — as reported by the Times — was that the U.S. had deployed its own hacking measures.
Using offensive measures is one of a number of solutions frequently discussed by lawmakers, and a popular one among more hawkish leaders. But a multistakeholder study into ransomware known as the Ransomware Task Force, which gained a lot of traction on the Hill since its release in April, sees it as one consideration in a more balanced approach including raising cybersecurity standards, incentivizing alternatives to paying ransoms and geopolitical manuvering.
That balance works both ways, Michael Daniel, former White House cyber czar and current president and CEO of the Cyber Threat Alliance who served on the task force.
"Focusing on purely defensive measures is not going to be sufficient, since ransomware has risen to the level of a national security threat, in the near term using military cyber capabilities against the actors responsible for such attacks is therefore appropriate and necessary."