The Cuba ransomware group has doubled its number of American victims over the past year, infecting at least 65 U.S. entities across a broad range of critical infrastructure sectors and stealing more than $60 million in ransom payment through August 2022, according to a new joint advisory by the FBI and the Cybersecurity and Infrastructure Security Agency.
That’s an increase from the 49 U.S. victims and $43 million in ransom payments detailed in a December 2021 FBI flash alert. Many of the organizations targeted by the group are designated as critical infrastructure, with the agencies flagging the financial services, government, healthcare, manufacturing and information technology sectors as top targets.
Cuba ransomware has also compromised at least an additional 36 entities outside of the U.S. over that same period.
Ransomware group using new TTPs to deploy malware
To do this, the group has mostly been “living off the land” to carry out attacks, relying on a mix of known vulnerabilities, phishing campaigns, commercial remote desktop tools and stolen credentials to gain access to victim systems and deploy malware.
However, citing research from Palo Alto Networks, the agencies said that since May 2022, the group has been observed deploying a number of new tactics, techniques and procedures. According to Palo Alto Networks' Unit 42 security research team, those changes include the use of the ROMCOM RAT malware family, the ZeroLogon vulnerability, local privilege escalation exploits and a kernel driver that specifically targets security products.
“This year, Cuba ransomware actors have added to their TTPs, and third-party and open-source reports have identified a possible link between Cuba ransomware actors, RomCom Remote Access Trojan actors, and Industrial Spy ransomware actors,” the advisory reads.
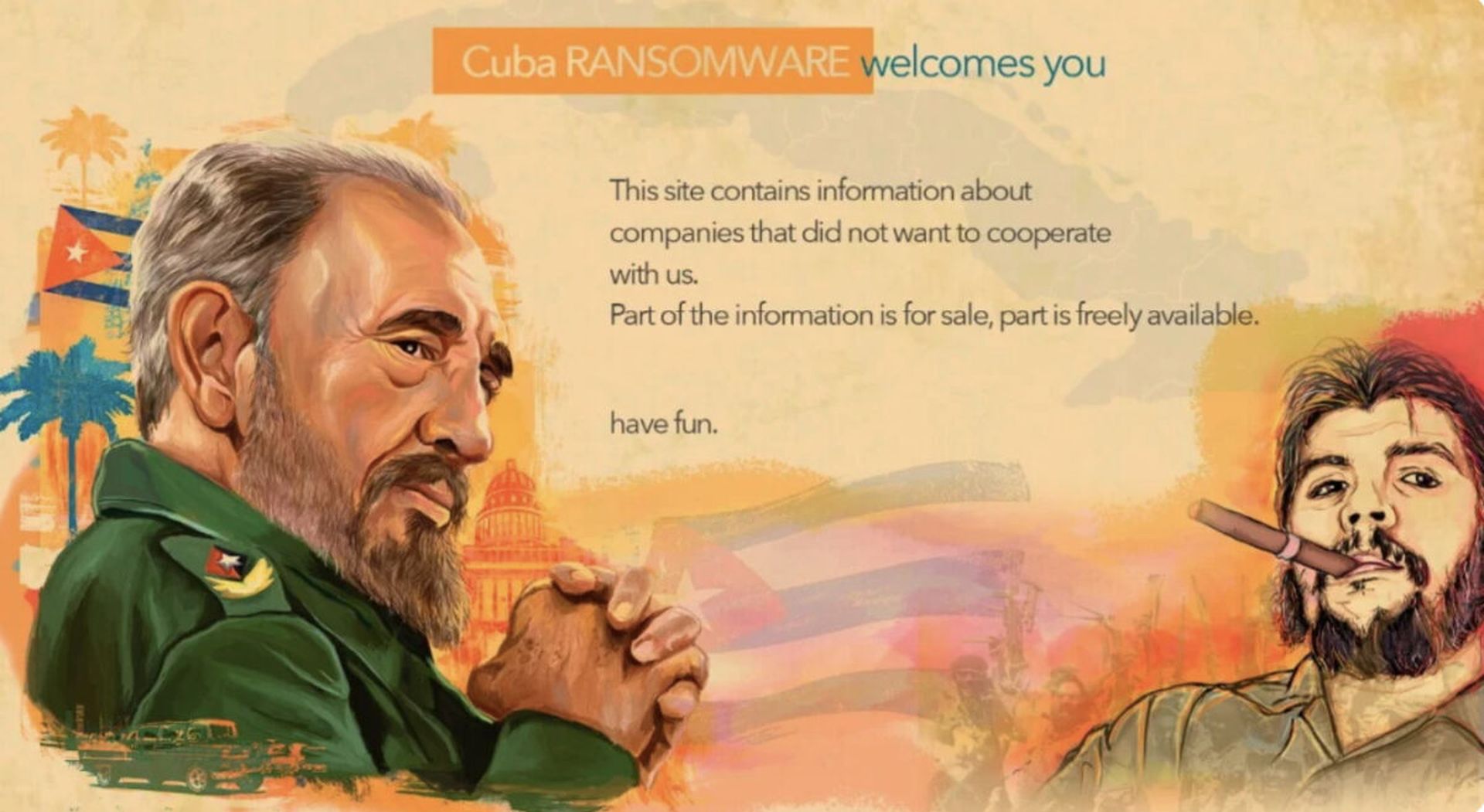
Despite the name, there is no evidence linking the Cuba ransomware group to the country of Cuba or the Cuban government. The document includes fresh indicators of compromise gleaned from FBI threat response engagements related to the group through August, as well as a sample ransom note sent to victims in broken English.
“Greetings! Unfortunately we have to report that your company were compromised. All your files were encrypted and you can’t restore them without our private key,” one sample note reads. “Trying to restore it without our help may cause complete loss of your data. Also we researched whole your corporate network and downloaded all your sensitive data to our servers. If we will not get any contact from you in the next 3 days we will public it in our news site.”
While some groups have experienced significant disruption after high-profile incidents targeting companies designated as critical infrastructure — such as when DarkSide was forced to go underground and rebrand after the Colonial Pipeline incident — attacks against those sectors have become a staple of modern ransomware operations, as many victims are responsible for delivering essential or continuous services to the public and are seen as more likely to pay.
Ransomware incidents against governments, particularly U.S. state and local governments, have also become a reliable revenue generator. Emsisoft analyst Brett Callow estimated there have been at least 99 local U.S. governments impacted by ransomware this year.
While criminal groups have traditionally steered away from attacking national governments, that could be changing as well, with Recorded Future researcher Allan Liska tracking at least 48 unique, publicly reported attacks against national governments and calling it “a big and growing problem, fueled in part by the fact that ransomware groups [are] not fearing repercussions.”
This week, a Treasury Inspector General report revealed that the IRS fought off an unsuccessful ransomware attack in May, identifying a computer with “website traffic patterns consistent with ransomware” before removing it from the network.



