A narrative has emerged over the years to explain why the intelligence community sometimes does not see eye-to-eye with chief information security officers: They are less technical, they don't have as much hand's on experience, and they don't grasp the significance of implementing a comprehensive incident response program.
"This is straight hot trash," said Matt Olney, director of threat intelligence and interdiction for Cisco Systems.
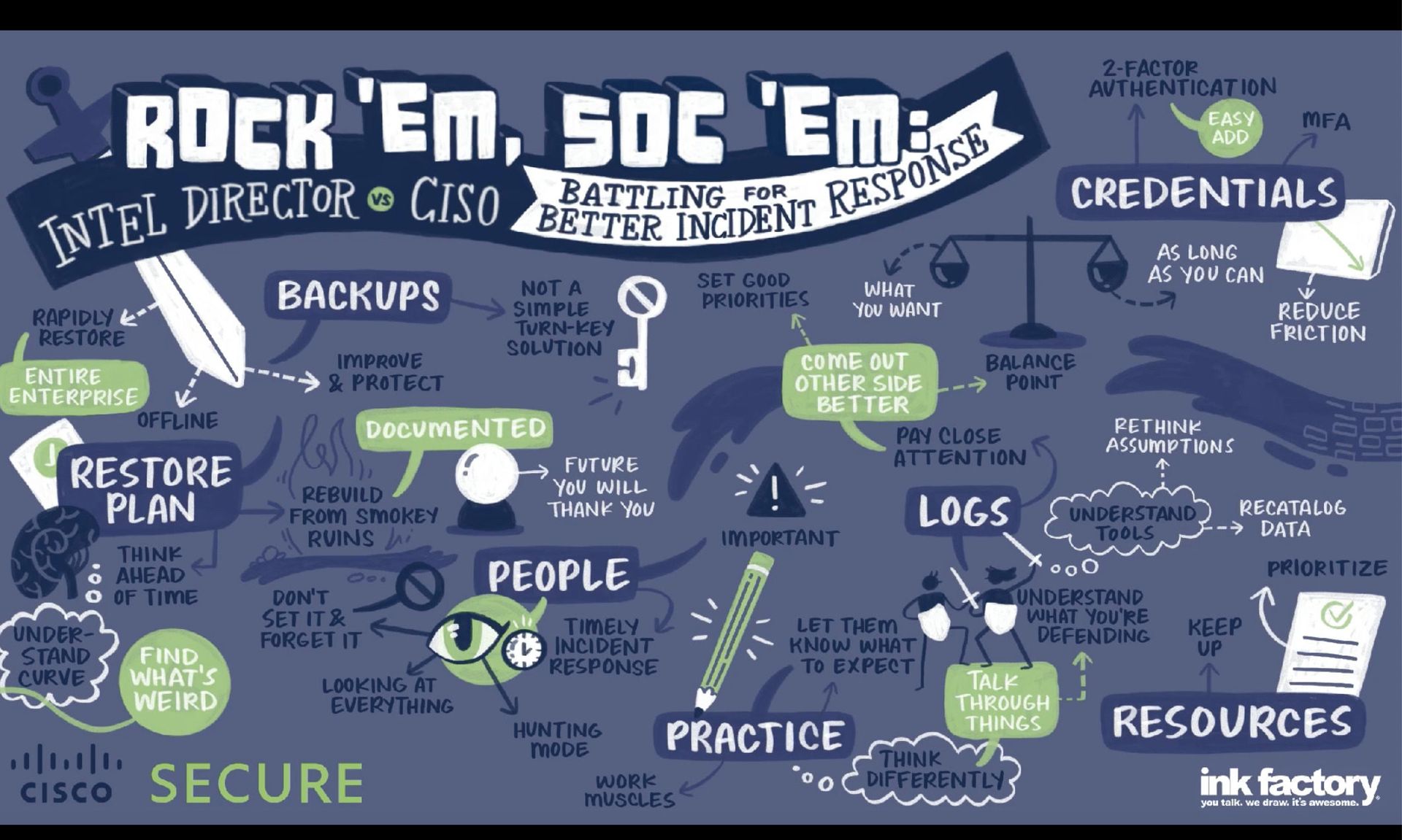
Olney and Wendy Nather, head of Cisco's Advisory CISO team, spoke to SC Media ahead of their virtual session at Black Hat, "Rock ‘Em, SOC ‘Em: Intel Director vs. CISO Battling for Better Incident Response," which dug into the sometimes complex relationship between enterprise security chiefs and the intelligence responders that come in following an incident to help piece together what went wrong.
"We find a number of things where these two are quite coordinated in their thoughts, then other times where there's a little bit of antipathy going on between the two of them," Olney said.
Indeed, "the most important message that I always want to get out is that the reason we keep seeing these problems is not because security defenders are stupid or lazy or malicious," added Nather. "It's an indicator that these are very tough intractable problems that need solving." The talk is "very much rooted in the respect for the CISO position," and understanding that the role is often rooted in resource management and prioritization.
Of course, the frustration among incident responders is not that difficult to undertand. So often they come in to assess situations that they have seen before, where they "know this playbook," as Olney put it. The frustration is followed by self reflection: What are we failing to do to get this information out?
"It's a false question. That information is out there," Olney said. "What you don't have is the person asking the questions in the context of all the challenges inside the enterprise."
The enterprise has all the constraints, agreed Nather, not just in terms of prioritization and money, "but cultural issues, or lack of influence, or the vendor being able to afford to hire the people that the defender really could have used internally." Too often the most compelling argument to the board for investing in cybersecurity is less risk management, and more an actual breach. Nather pointed to a CISO at a telco provider that had been fighting to implement new encryption in point of sale systems, but was denied because of the costs tied to 27,000 trucks rolling to the different locations.
Cisco approaches each incident with an "incident commander" — a senior person who manages the interaction between the client and the technical team, communicating that as much as there's a cost to that incident, there's also an opportunity to draw focus to problems that needs to be solved on the business side. When the peer got breached, that same CISO got the multi-billion dollar budget request approved within three days.
"The role of the CISO is not to be able to stand in at any given point on the wall and be a defender at the technical level," Olney said. "Their role is to be the ambassador of the security team to the board of directors, to the CEO, to the executives. And that is a very specific set of skills. There's a duality to it where you have to be empathetic to what is happening on this technical side, but also empathetic on the business side, and there are very, very few people in the world that can do both of those things."