Signaling a shift in what denotes national security risk, this year's Aspen Cyber Summit — traditionally a hub for talks about statecraft in infosec — veered toward systemic risk across the private sector.
"One of the things that's unique about the cyber summit this year is, in past years, normally what we spend much of the day talking about are the big four [Russia, China, Iran and North Korea]. And today it has been a ransomware conversation threaded through, instead," Garret Graff, Aspen Institute director of cyber initiatives told Rob Joyce, director of the NSA cybersecurity directorate during their keynote conversation.
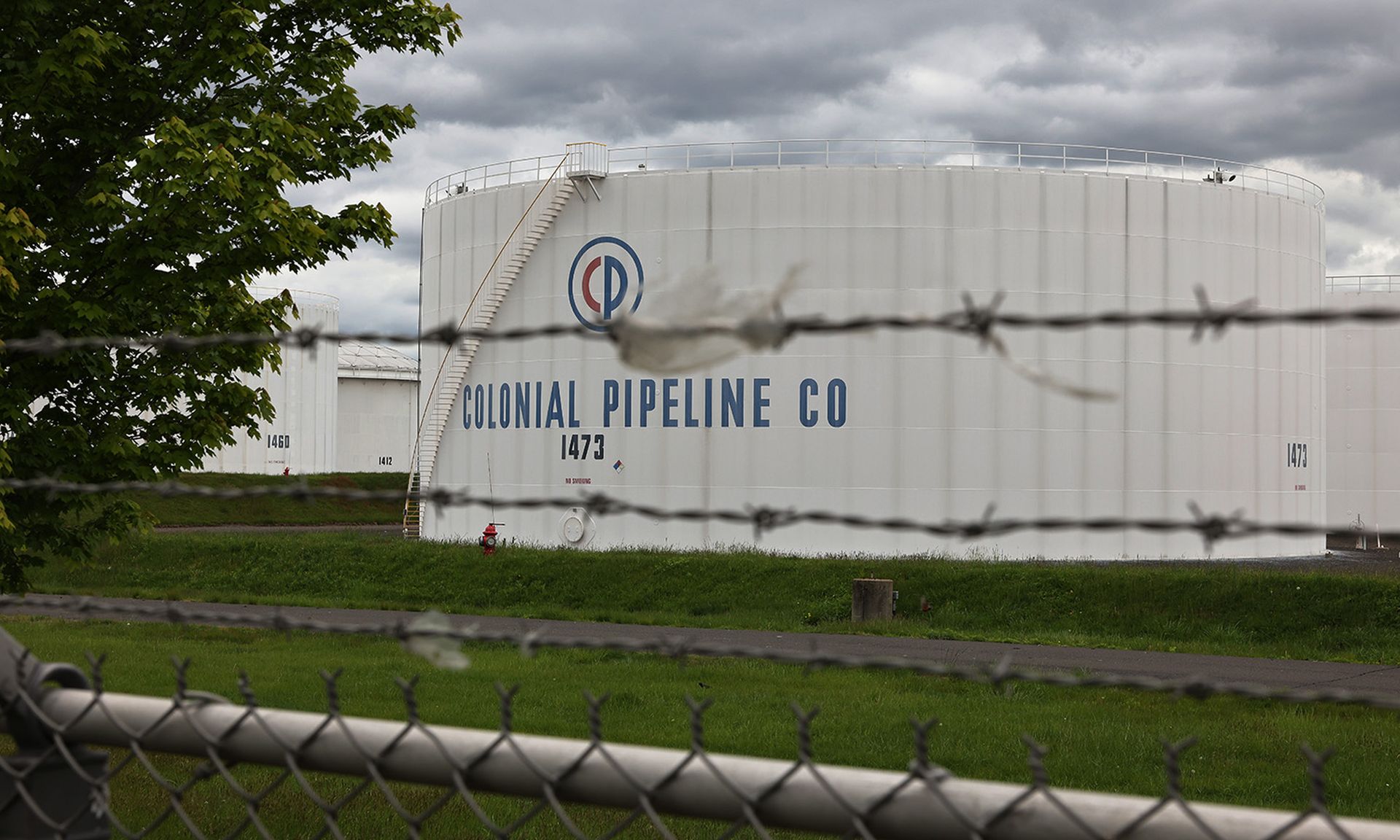
This year has been one where systemic cybersecurity problems have become the most visible and most impactful national security threat. The year started with SolarWinds in media res, which was quickly followed by Outlook Exchange — two instances of market-dominant products becoming single points of failure for huge swaths of the economy. That problem would echo later in the year with Kaseya. Meanwhile, ransomware attacks on meat supplier JBS and the Colonial Pipeline had massive impacts on supply chains, and encouraged government intervention into the private sector.
There's a long history of the interdependency of companies on major IT suppliers causing third-party risk; 2020 and 2021 were just when that risk boiled over to such widespread, simultaneous impact. But instances of open-source vulnerabilities or events like the 2016 DDoS attack on Dyn that caused outages of Netflix, Twitter and the New York Times, have always existed.
"Take a company like Slack, which you might not recognize as critical infrastructure," said Window Snyder, CEO of Thistle Technologies at the Aspen Summit. "But all these different cloud service providers are using Slack as their communication mechanism for operations. So when [Dyn] goes down and Slack depends on Dyn and Slack is not available and Slack is what everyone else is using to manage their operations and try and recover from the outage....we have all of these interdependencies and failures that pop up in unexpected ways."
At the Aspen Summit, Jason Healey, a Columbia University researcher and former White House adviser, said the best metaphor might be "Cyber Subprime," which he said he first heard (and hated) in 2014 after Heartbleed.
"The last thing we need is another 'cyber this' or 'cyber that' referring to the 2008, 2009 credit crunch," said Healey. "But the more I thought about it, the more I thought it's actually a fabulous analogy, because going into the credit crunch, you had these pools of financial risk that was pooling in place because it was not understood, and it had this cascading effect when it finally broke. The more expert you were, the more that you would have said it was impossible — these risks were correlated."
Panelists throughout the day pitched transparency as a key regulatory tool. Mandating software bills of materials, Snyder and Healey used as an example, would allow market forces to account for security, something Healey said security standard mandates might not be agile enough to handle on its own.
Red Balloon CEO Ang Cui said the problems of systemic risk were not problems industry would be able to innovate its way out of.
"Innovation, by definition, actually generates systemic risk," he said, noting that the new technologies implicitly create new externalities.
Johnson & Johnson Vice President and Chief Information Security Officer Marene Allison suggested redundant forms of network software might become critical components of business continuity planning.
"All the things that were put in place, generators and dual redundancy for networks and dual redundancy for power ... now, in cyber, we're starting to see that type of resiliency built-in," she said.
With cyberattacks on IT dependencies and critical supply chains, information security has become more visible than ever — the dependency issue is starting to impact the general public. While the national security problem was top of mind at the summit, Sam King, CEO of Veracode, noted a secondary concern the attention caused.
"When I first started, my parents didn't quite understand what I do for a living. Then they got to a point where they were really proud of what I did for a living, and lately they are at a point where they're looking at me and say, 'Are you really good at your job or not?'" she said.