Companies in the water and wastewater sector are the latest industry to receive a warning from U.S. government agencies that malicious hackers are targeting their systems and equipment.
A joint alert by four federal agencies (FBI, National Security Agency, Cybersecurity and Infrastructure Security Agency and the Environmental Protection Agency) said that companies in this sector continue to face “ongoing” targeting of their information technology and operating technology by both known and unknown malicious hacking groups.
“This activity — which includes attempts to compromise system integrity via unauthorized access — threatens the ability of [water and wastewater] facilities to provide clean, potable water to, and effectively manage the wastewater of, their communities,” the agencies warned.
Ransomware, insider threats and shoddy access controls are at the heart of many threats against the water and wastewater industries. Since the onset of COVID-19, these facilities are also increasingly reliant on remote login tools, like Remote Desktop Protocols, that have been persistently targeted by ransomware actors and other hacking groups during the pandemic.
Like almost every industrial sector, these companies are vulnerable to spearphishing campaigns, vulnerabilities in old or unpatched legacy software and other common staples of the hacking world. And like those other sectors, water and wastewater facilities are understaffed and underresourced when it comes to cybersecurity.
In many cases, IT systems are connected to or integrated with operational technology that control physical machines, and getting access to one can sometimes be sufficient to compromise the other. The agencies highlight a number of security incidents — nearly all of them ransomware related — that have affected the sector since 2019:
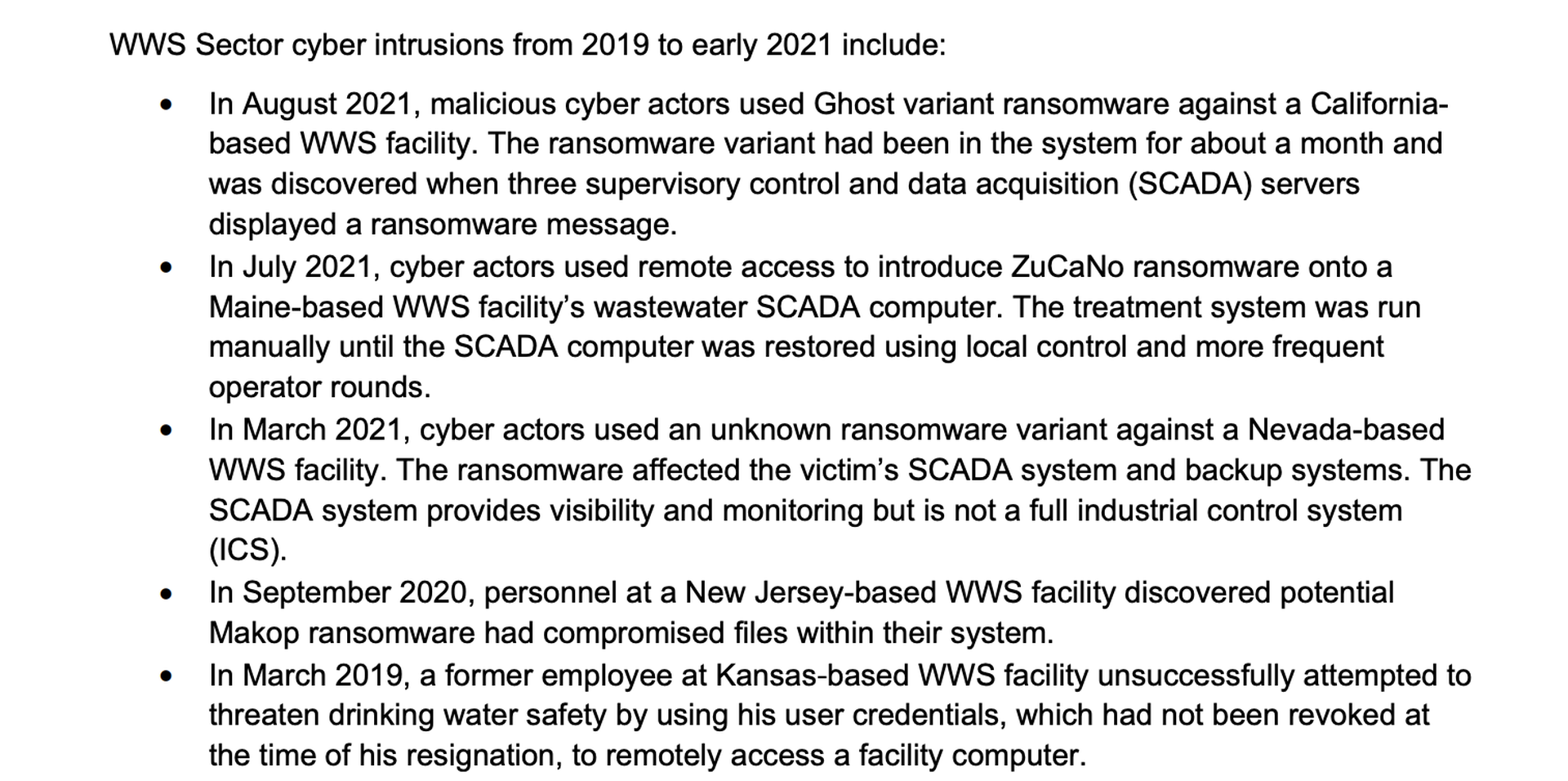
Additionally, hackers attempted to poison a water treatment plant in Oldsmar, Florida, in February, while reporting from NBC News uncovered a similar attempt by unknown hackers against a water treatment plant in the San Francisco Bay Area in January.
If many of the tactics, techniques and procedures are relatively basic, so too is much of the mitigation advice the agencies dole out. Building in strong multifactor authentication protocols for accessing operational technology networks — including access requests from the same company’s IT network — can dramatically limit the amount of damage that a malicious actor can do to the actual machinery and the protocols they follow to treat and process clean water. So too can things like strong logging, blocklisting or allowlisting and network segmentation between IT and OT. They also recommend implementing “demilitarized zones” in the form of firewalls, jump servers, and one-way communication diodes to prevent IT and OT systems communicating in an unauthorized way.
Many of the incidents cited by the government involve compromise of supervisory control and data acquisition systems that monitor and manage machinery. To that end, the agencies recommend water and wastewater companies set up strict monitoring regimes and look for anomalous behavior or signs, like an inability for employees to gain access to those systems in whole or in part, unfamiliar data windows or system alerts, access at unusual times of the day and unexplained restarts.




