In the aftermath of a suspected cyberattack on a Toyota parts supplier which caused the carmaker to suspend domestic operations in Japan Tuesday, researchers point to the need for greater focus on unchecked software vulnerabilities throughout any manufactured product’s lifecycle.
Indeed this week's incident demonstrate a more sweeping challenge facing security teams, as demands for integration and speed of development trump the diligence in code integrity. That translates to “solving for secrets in code” in lieu of a comprehensive solution to address code related risks, said Pan Kamal head of product at BluBracket.
“We have also seen this with developers becoming increasingly involved with the deployment of application security, as the software deployment has accelerated and application security has become more complex," he continued. "Vulnerabilities in code are contributing to it becoming the largest cyberattack surface.”
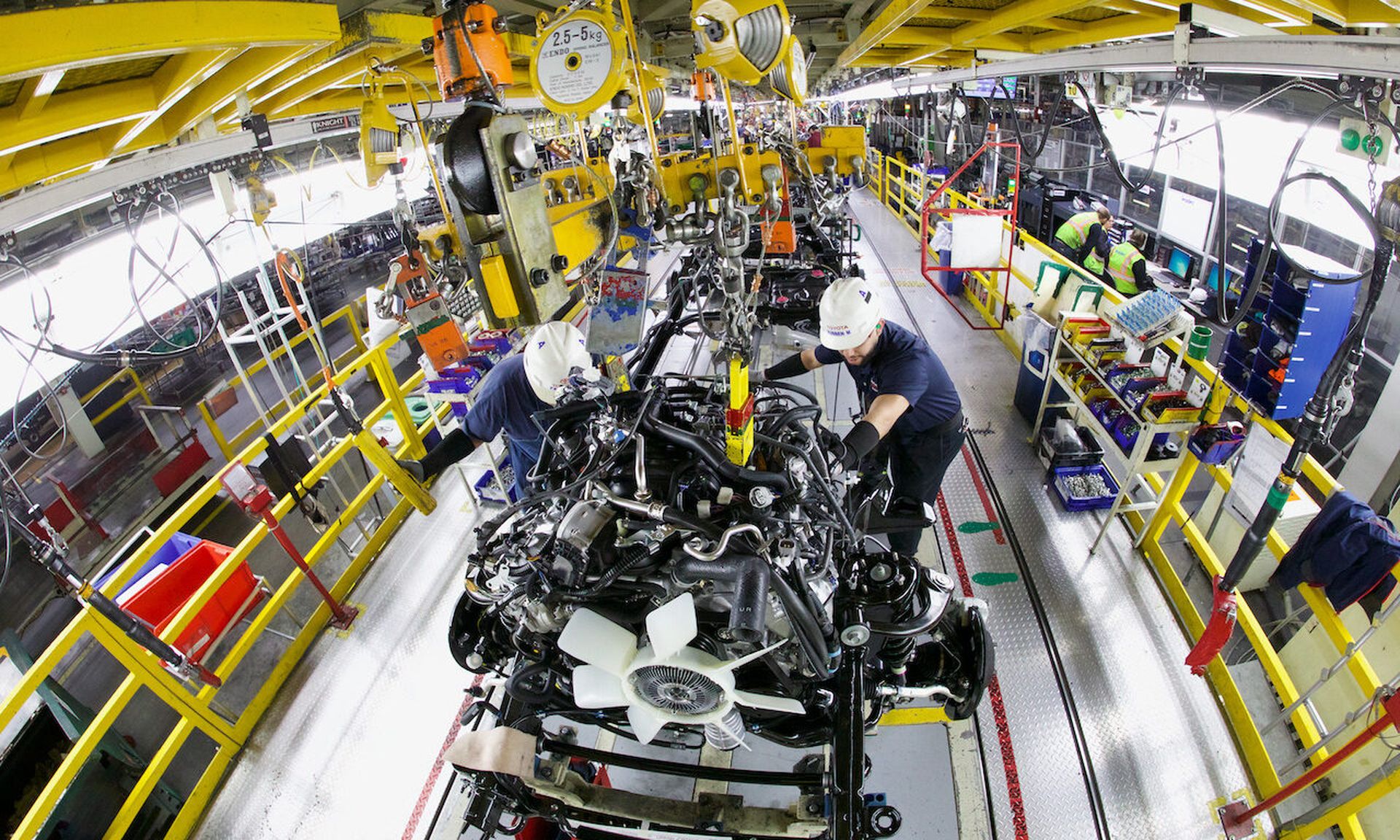
From parts to production
Slava Bronfman, co-founder and CEO at Cybellum, an automotive cybersecurity company, added that for manufacturing plants and other critical infrastructure companies to protect themselves as much as possible from cyberattacks, they need to start at the supply chain and continuously monitor for vulnerabilities, starting with equipment and systems and ending with production.
That sort of visibility speaks to the need for both hardware and software bills of materials tied to incoming components, for review of all open source software in use, and for monitoring of any code developed in-house for vulnerabilities, Bronfman said.
“In addition to vulnerability management, there should be red teams set up whose job it is to infiltrate the companies without limitations so they can accurately simulate a hacking attack and there should also be a group whose job it is to do threat hunting for zero-day vulnerabilities," he added. "These activities should all be coordinated and orchestrated under the chief product security officer and the CISO."
Software and physical supply chain intersection on display
Both the software supply chain and the physical supply chain have frequently made headlines in the last couple of years, noted Hank Schless, senior manager, security solutions, at Lookout. The Toyota incident exemplifies how intertwined the two are, and how a successful attack on the software supply chain can have negative effects on the output of physical goods produced.
“If an attacker wants to disrupt operations of a particular organization, targeting resources higher up the supply chain can have rippling effects,” Schless said. An organization like Toyota has a massive infrastructure with countless access points, which means attackers have a handful of avenues they can exploit to gain unauthorized access to apps and data. Everything is so interconnected, especially when it comes to cloud apps, that successful entry into a seemingly tangential resource could actually give an attacker a backstage pass to more valuable parts of the infrastructure.”
Jennifer Tisdale, CEO, at GRIMM, added that although the auto industry has stepped up its cyber game in recent years, there’s room for improvement in relation to the mitigation of cybersecurity risks – be it to vehicles or production environments.
“Manufacturing facilities, utilities, and critical infrastructure of all types should take heed of the Toyota incident as it’s prevalent in every IT and OT environment,” Tisdale said. “Whether a threat to intellectual property such as design files, quality production of goods, or disruption of service provision of clean water, electricity or power and energy to our communities, the threat is real. Given today’s geopolitical climate, we can no longer operate on the assumption our industries and our communities are not targets.”
The incident also placed on display Toyota’s REinforce Supply Chain Under Emergency (RESCUE) supply chain database system, which was once lauded, but now may need a refresh.
“While many manufactures focus on the availability of those products and services as it feeds into the outsourcer’s own end-product, the outsourcer often fails to assess the resilience controls (e.g., security, recoverability) of the operations and systems that allow the product or service to be provided by the supplier,” said Tom Garrubba, vice president of Shared Asseessments. “Failure to do so can bring on disruptions with catastrophic results such as financial and reputational loss.”
While the nature of the attack has not been confirmed, it came not long after Japan said it would join the Western allies in its effort to harm Russia economically for its invasion of Ukraine.