The Department of Homeland Security has formally established a review board that would be charged with investigating the cause of and fallout from major hacks that touch the federal civilian government.
According to a Federal Register Notice published Feb. 2, the board will be comprised of up to 20 members selected by the director of the Cybersecurity and Infrastructure Security Agency (CISA) and will be chaired by the Department of Homeland Security undersecretary for strategy, policy and plans, a post currently filled by Rob Silvers. Google senior director of security engineering Heather Adkins will serve as vice-chair.
The board must include at least one member from the Departments of Defense, Justice and Homeland Security, the FBI, CISA and the NSA. On the industry side, the board will include “individuals from private sector entities to include appropriate cybersecurity or software suppliers.” A representative from the Office of Management and Budget (OMB) will also “participate” in meetings for incidents that affect federal civilian IT systems.
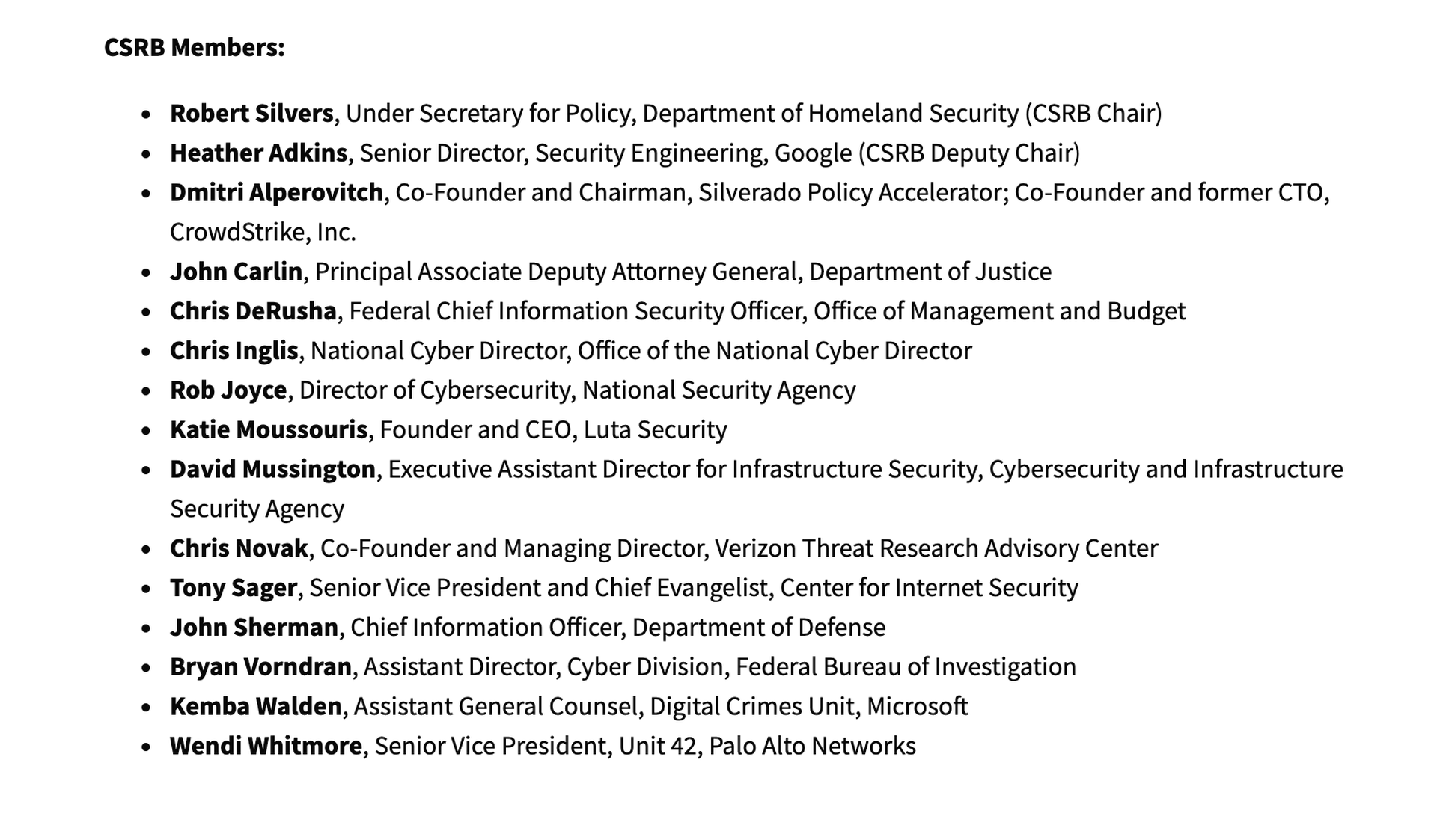
A day later, CISA officials released a full list of members, which includes National Cyber Director Chris Inglis, Federal Chief Information Security Officer Chris DeRusha, Deputy Attorney General John Carlin, NSA Director of Cybersecurity Rob Joyce, Luta Security CEO Katie Moussouris, Palo Alto Network security executive Wendi Whitmore and others.
News of the individual members was first reported by the Wall Street Journal.
The Cyber Safety Review Board was created through an executive order signed by President Joe Biden last year. Similar to the National Transportation Safety Board’s role investigating the cause of airplane crashes or train derailments, the board will be charged with studying the cause of and fallout from major hacks that affects the government, like the SolarWinds and Microsoft Exchange vulnerabilities that led to the compromise of numerous federal agencies.
There is one major difference: whereas the NTSB is an independent agency empowered by Congress, the CSRB is intended solely as an advisory body to CISA, which has a central role coordinating and managing the cybersecurity operations of civilian agencies along with agency chief information security officers (CISOs), OMB and the National cyber director.
According to the notice, the board will convene following “significant cyber incidents” that trigger the establishment of a Unified Coordination Group, which act as flash task forces that allow agencies to quickly gather and meet to coordinate or respond to emerging threats and incidents. The review board can also be convened at the discretion of the president of the United States or the director of CISA as needed.
The purpose of the board is to develop “advice, information or recommendations…for improving cybersecurity and incident response practices and policy” that will eventually feed up to the secretary of Homeland Security and White House.
“It’s only a matter of when, not if, we face another widespread cyber breach that threatens our national security," Sen. Mark Warner, D-Va., said in a statement. "I was glad to see this NTSB-like function included in the President’s May 2020 executive order on cybersecurity, and this is a good first step to establishing such a capability."
Last October, Robert Huber, chief technology officer for Tenable, laid out qualifications prospective members should have in order to make the board’s work effective. It must draw members with deep technical experience, including CISOs and chief technology officers (CTOs) who can analyze the details of attacks and formulate technical solutions, digital forensics and research experts who can map out exactly how attackers compromised vulnerable IT systems or hardware and CEOs and other C-Suite leaders who can bridge the security recommendations to larger business goals in industry and critical infrastructure.
“The Secretary of Homeland Security should consider the above experience and expertise as key assets as it establishes the Cyber Safety Review Board; otherwise, it runs the risk of attenuated and ineffective cyber strategies and recommendations,” Huber wrote.




