Malicious actors are using the massive supply of previously stolen login credentials to help brute force their way into high-profile cloud-based business systems that cannot easily use two-factor authentication for security.
Proofpoint researchers found the availability of these tools has powered a massive increase in the number of cloud attacks taking place which in turn enable the attackers to possibly gain access to the people inside an organization who can be conned out of money. One new use of the previously harvested credentials was to utilize the stolen usernames and passwords to conduct a hybrid brute force attack password spraying attack. In these cases the stolen logins are used to enmasse with the hope that a match takes place allowing access.
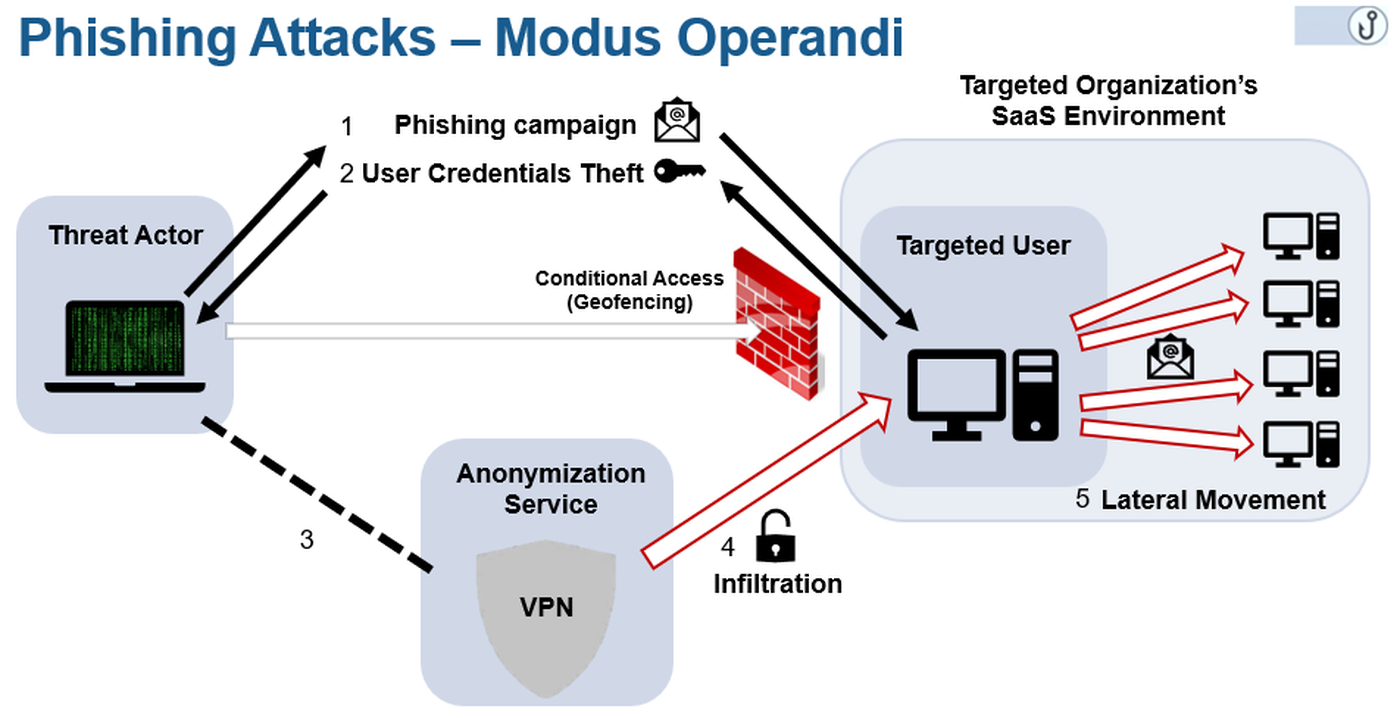
There is also an ancillary attack type that uses phishing to gain initial entry into a target organization, then using the older credentials to move laterally.
“The attacker’s primary aim is often to launch internal phishing, especially if the initial target does not have the access needed to move money or data. Post-login access to a user’s cloud email and contact information improve an attacker’s ability to expand footholds within an organization via internal phishing and internal BEC,” the report said.
Proofpoint’s researchers studied hundreds of thousands of unauthorized logins and found 72% of cloud tenants were targeted at least once by threat actors, 40% of tenants had at least one compromised account in their environment 15 out of every 10,000 active user-accounts were successfully breached by attackers.
Perhaps tiring of relying on Nigerian prince scams and looking for something new and more productive, the most of the successful attacks, 40 percent, were tracked to IP addresses located in that African nation. Next on the list was China being home to 26 percent of the attackers, than the United States, Brazil and South Africa.
“Between November 2018 and January 2019, successful brute force and phishing-related attacks involving Nigerian IP addresses increased by 65%. While these attacks did not all necessarily involve Nigerian actors, recent arrests and activity are consistent with widespread cybercrime in the region,” the report stated.
The research showed most of the attacks abused the IMAP protocol, most likely because it bypasses multifactor authentication and failed attempts to gain access to not result in account lock out so it is difficult to detect the attack because no trail is left.
About 60 percent of Microsoft Office 365 and G Suite tenants were hit with IMAP-based password brute force/spraying attacks resulting in a successful breach 25 percent of the time.
“The recent breach of Microsoft Office 365 and G Suite accounts despite them being protected with multi-factor authentication (MFA) highlights the underlying issue with MFA. It is still ultimately built on passwords and shared secrets, and as such it leaves critical infrastructure open to credential stuffing and spraying attacks,” George Avetisov, CEO and co-founder of HYPR.
The attacks that started with a phishing attack also proved successful with 31 percent of the cloud tenants studied being breached in this method. Again, the Nigerians led the way here with 63 percent of successful attacks coming from this nation, followed by South Africa home to 21 percent of the fruitful attacks and then the U.S. with 11 percent.



