In the same way that 9/11 led to substantial changes to how intelligence was handled, how the government was structured, and how laws applied to terrorist threats, the SolarWinds supply chain hack could inspire governments to rethink laws, regulations and strategies.
Sources differ whether this particular national security disaster, where the security of one private sector firm impacted organizations across the government and business spectrum, will bring similar change.
"This is a big intrusion, but we've seen big intrusions before," said Jonathan Reiber, a former chief strategy officer at the Department of Defense for cyber policy and current senior director for strategy and policy at AttackIQ. And, none of them, from the OPM and DNC breaches to WannaCry and NotPetya, have brought about dramatic cybersecurity changes.
"I am not optimistic about significant reform, at least at the legislative level, because I am not optimistic that we will find common ground or convergence on the SolarWinds and related hacking, and the need for bold action," said David Kris, former head of the Department of Justice's National Security Division and founder of the Culper Partners consulting group via email.
In the aftermath of the SolarWinds hack, three stumbling blocks dot the path to change, Kris said: A tendency of the government to hold hearings to "admire the problem" without solving it, a political separation that has been especially sharp around Russia throughout the Trump administration, and the technical complexity of cybersecurity, which can spin the heads of less savvy lawmakers.
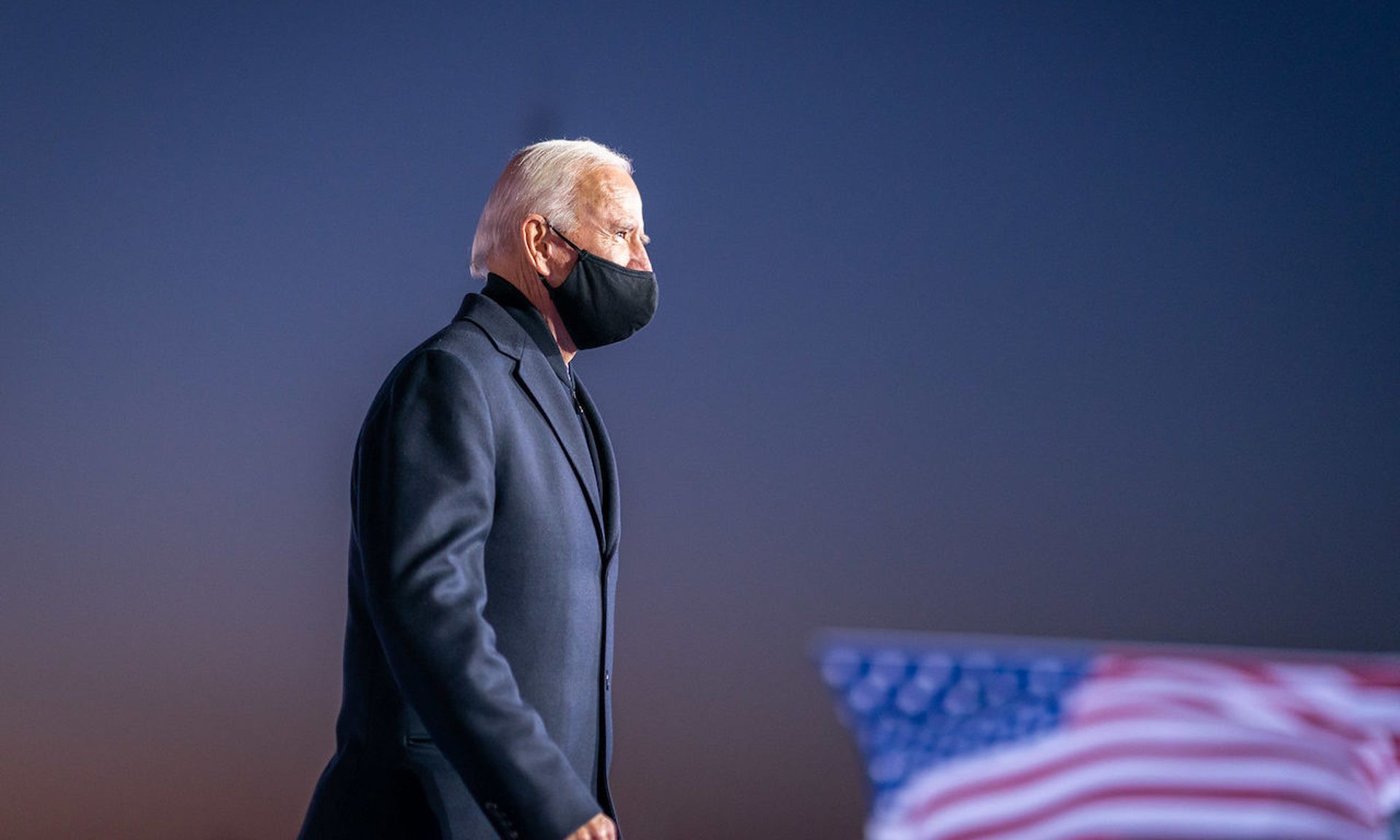
But the sway of the Trump administration's posture toward Russia will fade as his administration nears its end, leaving the incoming Biden administration with several opportunities to take up the cause.
"There's often a sense when you're in the middle of one of these where it feels like everything will change, before it doesn't," said Philip Reiner, CEO of the Institute for Security and Technology. "The interesting thing here is the timing."
Reiner suggested, for example, that Biden could shift resources from the offensive cyber operations to the defensive side, devoting significant federal resources to researching and defending critical infrastructure and critical supply chain components like SolarWinds.
"We could spend more on [the Cybersecurity and Infrastructure Security Agency] and less on Cyber Command," he said.
Former White House Cyber Czar Michael Daniel, now president and CEO of the Cyber Threat Alliance, is optimistic that changes are in the offing, but stressed that the form and efficacy of those changes would depend on who spearheaded the effort.
"Absent clear leadership, it will not be obvious what policies to focus on or which changes to make," he said via email.
Daniel offered several potential policy options for improving supply chain security, including requiring vendors for critical products or services to address cybersecurity in all contracts within their supply chain. He also advocated for the "bill of materials" concept, where vendors provide detailed explanations of the third-party components that make up software and hardware.
Daniel and Kris both suggested that in the future the entire government, and not just the Department of Defense, could use cybersecurity as a criterion for selecting vendors.
"Would such a requirement entirely prevent an incident like this? Of course not, because even companies that are good at cybersecurity can get hacked," Daniel said. "But it can reduce the risk and force the adversaries to go slower and take on more risk."
Calls have also been made for improved cooperation between government and industry. Microsoft President Brad Smith said in a Thursday blog, "we need a more effective national and global strategy to protect against cyberattacks. It will need multiple parts, but perhaps most important, it must start with the recognition that governments and the tech sector will need to act together."
Importantly, noted Daniel, government should not respond to SolarWinds by focusing only on SolarWinds-type attacks.
"We can’t forget we still have much more work to do dealing with your more standard cyber threats," he said.