Amid the pandemic-fueled shift to remote work and collaboration, having a good end-user experience (UX) has become critical. Applications now place UX front and center, a massive change from legacy systems.
But there’s a problem: Security and compliance requirements invariably increase endpoint complexity, decrease performance, and detract from an employee’s ability to focus on their core jobs. Meanwhile, employees are being saddled with unrealistic security demands.
Fortunately, there’s a solution to this problem, which is outlined in a recent paper from HP: “Rationalize Security Awareness Training to Improve User Experience.”
Pain points
The paper captures the arduous, unrealistic responsibility companies place on users to avoid social-engineering tricks that can lead to a data breach, such as phishing. “The approach has an unacceptable level of user experience degradation, and isn’t particularly effective,” the author notes. The pain is also captured in this table:
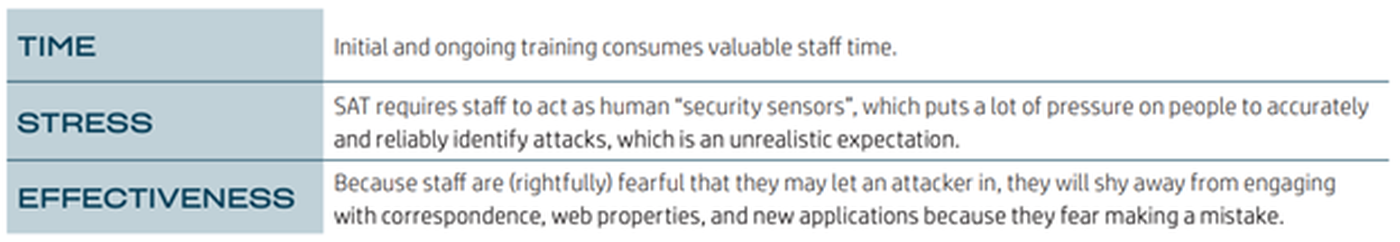
“While security awareness training (SAT) may be seen as a necessary evil, we need to consider the possibility that there’s a better way to reduce risk with less negative impact to user experience,” the author writes.
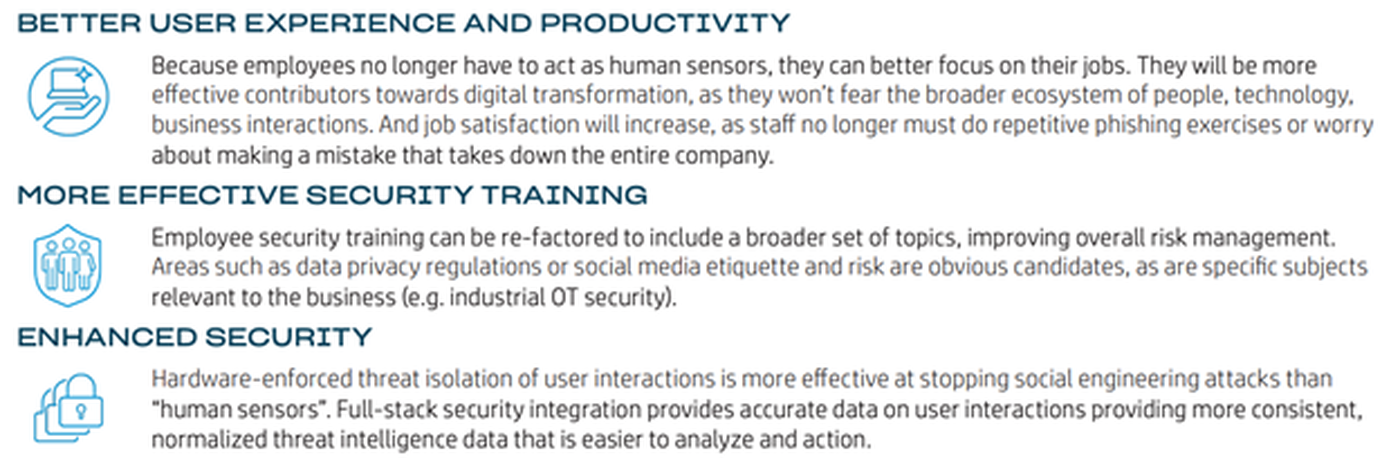
The solution: moving to hardware-enforced threat isolation to detect and defeat such threats. By doing so, IT teams can immediately improve user experience, increase the value of security training and reduce risk, maximizing employee engagement, flexibility and retention.
“In this scenario, we do not depend on our employees to be accurate, reliable ‘phishing detectors’ and instead leverage scalable, reliable technology,” the paper states.
How it works
Advanced threat isolation works by removing humans from the SAT process, relying instead on an approach where the hardware, operating system, and security policy enforcement work together to form a defensive net to contain endpoint attacks before they can infect the user’s PC. It has the added benefit of providing detailed security forensics data that informs company policy control strategies.
The benefits are captured in this visual:
HP’s approach to endpoint threat isolation is its Sure Click Enterprise (SCE) solution, which
places each user task in its own micro-virtual machine, trapping and isolating malware that tries to download during common user actions like clicking on a link or opening an attachment. This isolation is enforced in hardware by the PC’s CPU, so malware can’t escape. When the task is completed, the micro-VM is deleted, permanently removing the malware from the PC. The process is transparent to the user while funneling threat intelligence to the security team.
More information is available here.