To kick off RSA USA 2022 in San Francisco earlier this month, Qualys unveiled VMDR 2.0 with TruRisk, the latest version of its vulnerability management, detection and response cloud-based service platform.
The updated service puts greater emphasis on cyber risk management, as Qualys Vice President of Product Management Mehul Revankar explained June 8 in an interview, streamed from RSA Conference 2022, with CyberRisk Alliance Vice President of Content Strategy Bill Brenner.
"When we launched VMDR 1.0 about two years ago, the key thing we were trying to drive was through consolidation," Revankar said. "Customers had many tools but fewer solutions. They had one solution for asset management, one solution for vulnerability assessment and detection, a different solution for prioritization, a different solution for remediation and response."
"These tools didn't necessarily talk to each other," Revankar added. "So we consolidated all of that into an all-in-one solution to discover, prioritize and remediate vulnerabilities at scale."
VMDR "helped us change the game on vulnerability management," Revankar said, citing more rapid detections of both vulnerabilities and assets, plus improved patch times of almost 60 percent.
Appetite for risk management
But, he added, when the Qualys team began to plan VMDR 2.0, they found that their clients were looking for something more.
"Customers were more focused on risk and less about vulnerabilities," Revankar said. "Everything, every question that we were getting asked was 'How do I manage risk? How do I reduce the risk? What do I do to close the gap in IT and security? How can I automate things?'"
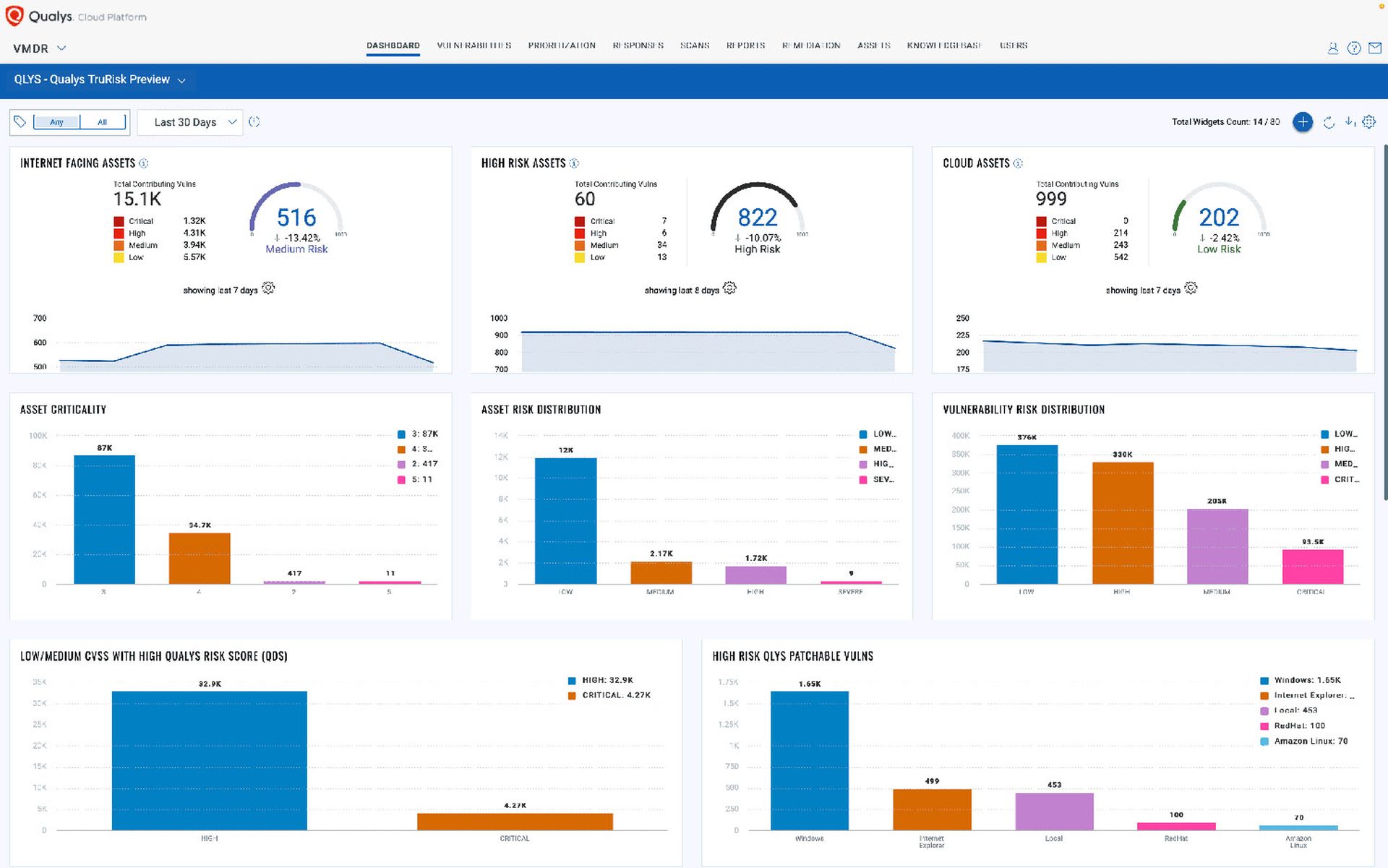
To that end, VMDR 2.0 with TruRisk was developed to provide organizations with greater insight into their cyber risk, along with new ways to mitigate and manage those risks. Users are presented with a dashboard that applies risk scores of zero to 1,000 for internet-facing assets, high-risk assets and cloud assets, along with bar charts showing the criticality and distributions of assets and vulnerabilities.
"The concept of risk is very easy to understand, but to implement is very difficult," Revankar explained. "You could have a vulnerability on an asset that is internal and a critical vulnerability but the risk is low. But the same one on an external-facing asset, it's actually a big deal."
"Same thing goes with the criticality of the asset," he added. "What value does it prove? Is it like, you know, import[ant]? Does it serve an important function in the organization? All these things have to be taken into account as part of your risk equation."
No critical errors
The asset criticality is determined automatically in VMDR 2.0, Revankar explained, to avoid human error.
"One of our fundamental beliefs is if organizations have to manually set the criticality we have lost the game already," he said. "If you have like 100 systems, that's probably fine, but if you're dealing with 100,000 or millions of assets, that's just not feasible. So we integrated with CMDBs [configuration management database] to automatically bring in the business criticality for asset criticality, and that automatically drives the asset risk score."
Likewise, VMDR 2.0's assessment of vulnerability risk is based on the specific risk to a particular organization instead of being based on a one-size-fits-all CVSS score, which Revankar said "represent[s] the technical severity of the vulnerability."
Instead, VMDR 2.0 probes the parameters of each vulnerability to reveal its aspects and how they might threaten your organization.
"What is the exploit code maturity for this vulnerability?" asked Revankar. "Is it weaponized? Can somebody just take it and run it and exploit in a compromised system? Or is it just a proof of concept? Are there malwares or threat actors exploiting this vulnerability? If so, which ones are exploiting this vulnerability?"
Qualys' threat-intelligence database contains about 185,000 known vulnerabilities, Revankar said, but only about 4,000 have corresponding exploits. And of those, he said, "only 700 to 300 vulnerabilities are getting exploited by malware or threat actors," which naturally pose a high risk.
However, even well-known vulnerabilities may not pose a high risk to all organizations, Revankar said.
"If you had a mitigation controller compensating control on the system for that vulnerability, we lower the risk score for you so that you can focus on the real high-priority items in your infrastructure," he said.
Closing the gap
Revankar explained that one of the key things Qualys aims to do with VMDR 2.0 is to "close the gap between IT and security."
"One of the fundamental beliefs we have is [that] for vulnerability management to be done well, three key aspects have to come and converge: people, technology and processes," he said. "No matter how many improvements we make, how many improvements we make to the algorithm of the risk client, if the people and processes are not taken care of, the vulnerability management program will fail."
One way to achieve that, Revankar said, was to introduce Qualys modules compatible with ServiceNow's IT service management (ITSM) platform.
"You can directly import all these findings into ServiceNow, create tickets, assign it to the right people, close it out," he said. "IT teams can track their reporting and dashboards directly from ServiceNow. … No more manual spreadsheets, no more passing along PDF reports and things falling through the cracks."
Another was to add a no-code, drag-and-drop programming workflow to VMDR 2.0 to make automating of tasks much easier.
"With the rise in vulnerabilities, the number of people required to fix these things are not rising at the same rate," Revankar said. "You're expected to do more with less. The only way to do that is with more automation."
"So we're also introducing no-code workflows," he said. "We're introducing templates in our in our platform where you can quickly select our pre-packaged templates" to more quickly respond to new threats.
"All of this is included with the VMDR solution so [our customers] get risk-based vulnerability management automation with our integration with ITSM and then the no-code workflows to empower the security teams and IT teams to do more," Revankar said. "A lot of value is packed into VMDR so that customers can do vulnerability management really well."



