Threat groups behind Killnet and BlackBasta ransomware are targeting the healthcare sector and other critical infrastructure industries in force, according to Microsoft and the Department of Health and Human Services Cybersecurity Coordination Center.
The threat alerts were issued alongside a joint federal alert from the FBI, Cybersecurity and Infrastructure Security Agency, and the Multi-State Information Sharing and Analysis Center (MS-ISAC) over growing concerns about LockBit ransomware against multiple sectors.
In January, the Killnet hacktivist group deployed a massive DDoS attack campaign against healthcare, resulting in data exfiltration for more than two dozen covered entities. The campaign was believed to be only the first round of attacks and joined other targeted cyberattacks deployed by nation-state threat actors.
While DDoS attacks cause limited impacts for most sectors, denial of service against a patient-facing device can have serious impacts on care.
A blog post issued by Microsoft on March 17 provides greater detail on the scope of Killnet DDoS campaigns over the last three months. Researchers analyzed the DDoS attack landscape deployed against healthcare apps hosted in Azure between Nov. 18, 2022, and Feb. 17, 2023, and found the attempts spiked from 10-to-20 attacks in November to 40 to 60 daily attacks in February.
“DDoS attacks on healthcare organizations didn’t demonstrate severely high throughput,” researchers wrote. Several observed attacks hit 5 million packets per second (pps), but the majority of attacks fell below 2M pps.
Pharmaceuticals and life sciences industries were the primary targets (at 31% of attacks), followed by hospitals (26%), and health insurance, health service, and care at 16% each. “These attacks, although not extremely high, could take down a website” without proper DDoS security protection,” researchers explained.
Web apps and intertwined TCP and UDP were the primary attack vectors. In several instances, the researchers observed seven-layer DDoS attacks “consuming many TCP connections and keeping them alive long enough trying to deplete memory state resources to render the application unavailable.” The attack method models previous attacks tied to Killnet.
In another common attack method, the DDoS will attempt to “establish many new TCP connections over short intervals to hit CPU resources.”
In contrast to overall DDoS attack trends for 2022, in which TCP was the most common attack vector, 53% of the attacks on healthcare were UDP floods, and TCP accounted for 44%, reflecting a different mixture of attack patterns used by adversaries on healthcare.
Black Basta ‘credible threat’ to unpatched vulnerabilities
HC3 is urging healthcare entities to review tactics and recommended mitigation measures aimed to shore-up defenses against the ongoing threat of Black Basta. First spotted in early 2022, the threat actors behind the variant are known for their use of double extortion tactics.
Black Basta leverages ransomware, exfiltration techniques, and a cybercrime marketplace for extortion attempts. It’s believed the group is actually a rebrand of the Russian-speaking Conti group or perhaps tied to other Russian-based threat groups, due to the “level of sophistication” used in their ransomware operations.
“The threat group’s prolific targeting of at least 20 victims in its first two weeks of operation indicates that it is experienced in ransomware and has a steady source of initial access,” according to the alert. The group is also reluctant to recruit or advertise on dark web forums.
As such, it’s believed the actors are “seasoned cybercriminals.”
“Rather than rely on comprehensive spray-and-prey tactics, the elusive group takes various precautions and relies on a more targeted approach, calculatingly assessing its victims before compromise,” according to the alert. Black Basta “either excludes affiliates or only collaborates with a limited and trusted set of affiliates.”
In its initial attacks, Black Basta worked to purchase credentials for access to specific network targets. The “cunning” operators will often use unique tactics to gain initial access, before spreading laterally, exfiltrating data and deploying ransomware.
The exploits enabled the group to “cumulatively steal several gigabytes of data” tied to personal information of healthcare customers and employees.” In only a “short span of time, by remaining under the radar, Black Basta has conducted massive breaches in critical infrastructure across multiple countries.”
Notably, the cross-platform ransomware “is only executed with administrator privileges on both Windows and Linux systems,” the alert noted. Once deployed, the ransomware hinders machine processes and “ultimately makes desktop files unusable before sending a ransom note to a victim.”
The actors have successfully exploited specific health IT websites, they’ve also disrupted healthcare industry services, laboratory and pharmaceutical, and health plan entities.
HC3 believes these attacks will continue to target unpatched critical vulnerabilities in the public health and healthcare systems, which could have “potentially life threatening” impacts to critical infrastructure.
The alert contains a long list of relevant defensive measures, focused on multi-layered actions that can minimize exposures and potential ransomware impacts. These tactics are not specific to Black Basta’s custom tactics, but include effective measures noted by security researchers.
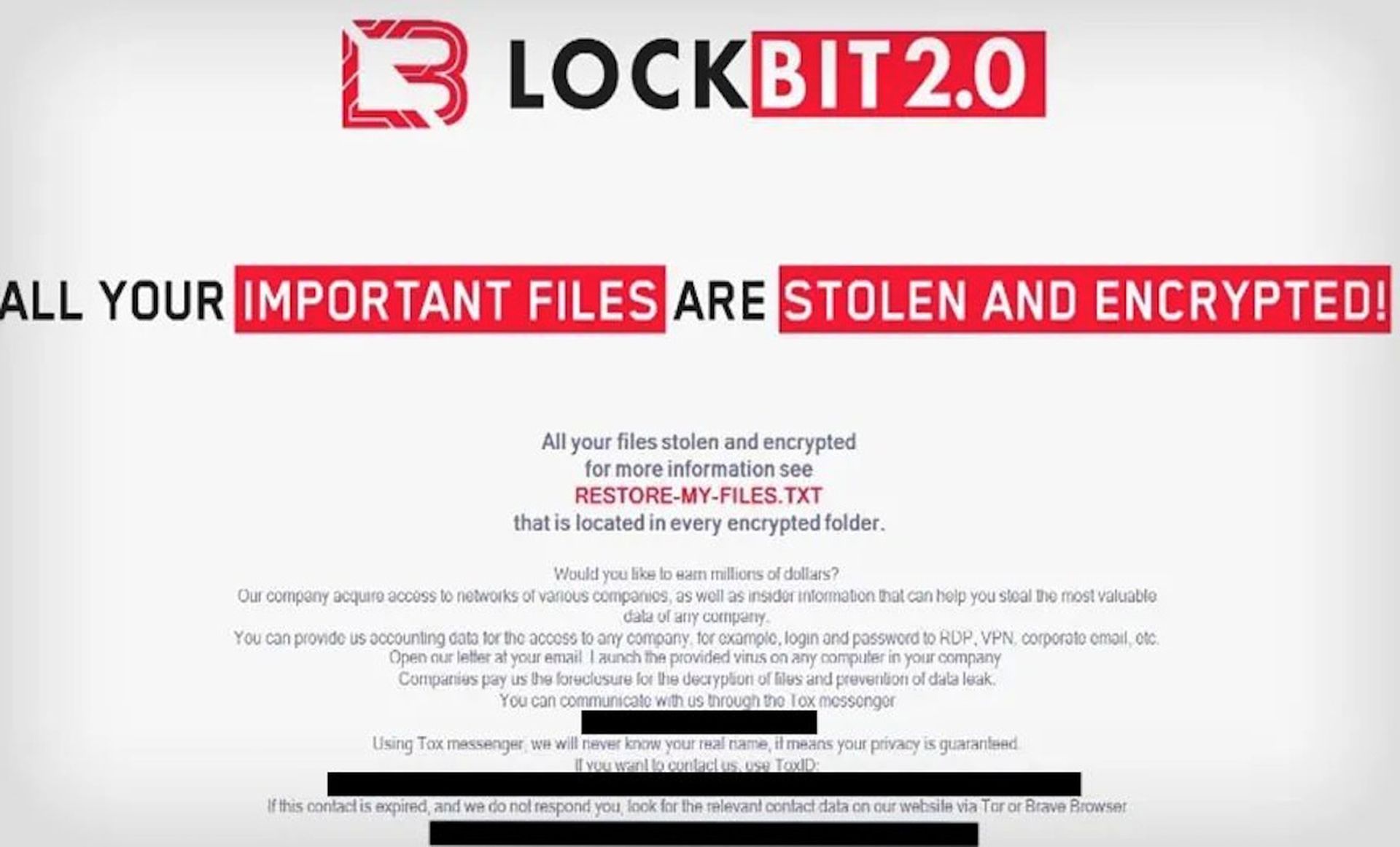
LockBit3.0 continues its effective malicious campaigns
On the heels of multiple reports detailing the prolific impact of LockBit3.0 attacks, a joint federal alert updates the known tactics of the group in hopes of stymying the ongoing impacts. The group has already hit the Washington state public transit system and ION Group in the last month.
The ransomware-as-a-service (RaaS) model is a continuation of previous LockBit versions and all have highly effective tactics that hinder the effectiveness of computer network defenses and mitigation.
Also known as LockBit Black, the latest variant “is more modular and evasive” than previous versions and shares similarities with Black Matter and Black Cat ransomware. The variant is both configured ahead of execution and able to determine the behavior of the ransomware on the targeted device.
In one instance, LockBit 3.0 was observed accepting “additional arguments for specific operations in lateral movement and rebooting into Safe Mode.” its code is password protected and affiliates without access to this model will be unable to execute the ransomware.
The CISA-FBI alert explains that the code protection helps evade detection and analysis, as the “code is un-executable and unreadable in its encrypted form.”
The actors behind the variant are still gaining access through remote desktop protocols (RDPs), “drive-by compromise”, phishing attacks, abuse of valid accounts, and exploits of public-facing applications.
Entities are urged to prioritize patch management or network segmentation of known, exploited vulnerabilities, in addition to training users how to recognize and report phishing attacks and enforcing “phishing-resistant” multi-factor authentication.