Researchers on Tuesday reported on new insights into the Chaos ransomware builder, research that revealed a twisted family tree that links it to both the Onyx and Yashma ransomware variants.
In a blog post, the BlackBerry research and intelligence team said that clues to the Chaos malware’s links to Onyx and Yashma surfaced during a discussion between a recent victim and the threat group behind Onyx ransomware. The discussion took place on the threat actor’s leak site.
According to the researchers, someone claiming to be the creator of the Chaos ransomware builder’s kit joined the conversation, and revealed that Onyx was constructed from the author’s own Chaos v4.0 Ransomware Builder. The author went on to promote the most current version of the Chaos ransomware line, now renamed Yashma.
This was not the first time the connection between Chaos and Onyx was disclosed. SC Media reported April 29 that research from Jiří Vinopal also found that Onyx based its wares on the Chaos ransomware builder.
The BlackBerry researchers pointed out that what makes Chaos-Yashma dangerous going forward is its flexibility and widespread availability. Because the malware is initially sold and distributed as a malware builder, any threat actor who purchases the malware can replicate the actions of the threat group behind Onyx, developing their own ransomware strains and targeting chosen victims.
"In addition to the technical deep-dive provided on the Chaos malware family tree, our research dives into the mindset of these threat actors, by showing an online exchange from someone claiming to be the very same Chaos ransomware builder author,” said Ismael Valenzuela Espejo, vice president of threat research and intelligence at BlackBerry.
“It’s interesting to see how beyond the obvious financial motivation, there’s a sense of pride in their creations, even when this malware has been labelled as a 'PoC' and 'unsophisticated wiper' by many researchers in the last yea," continued Espejo. "It’s also interesting to see how this comes from someone that at the same time attempted to steal thunder from an existing threat group (Ryuk) about a year ago, but was angered when their own creation (Chaos/Yashma) was also stolen and used as the foundation of a new threat (Onyx)."
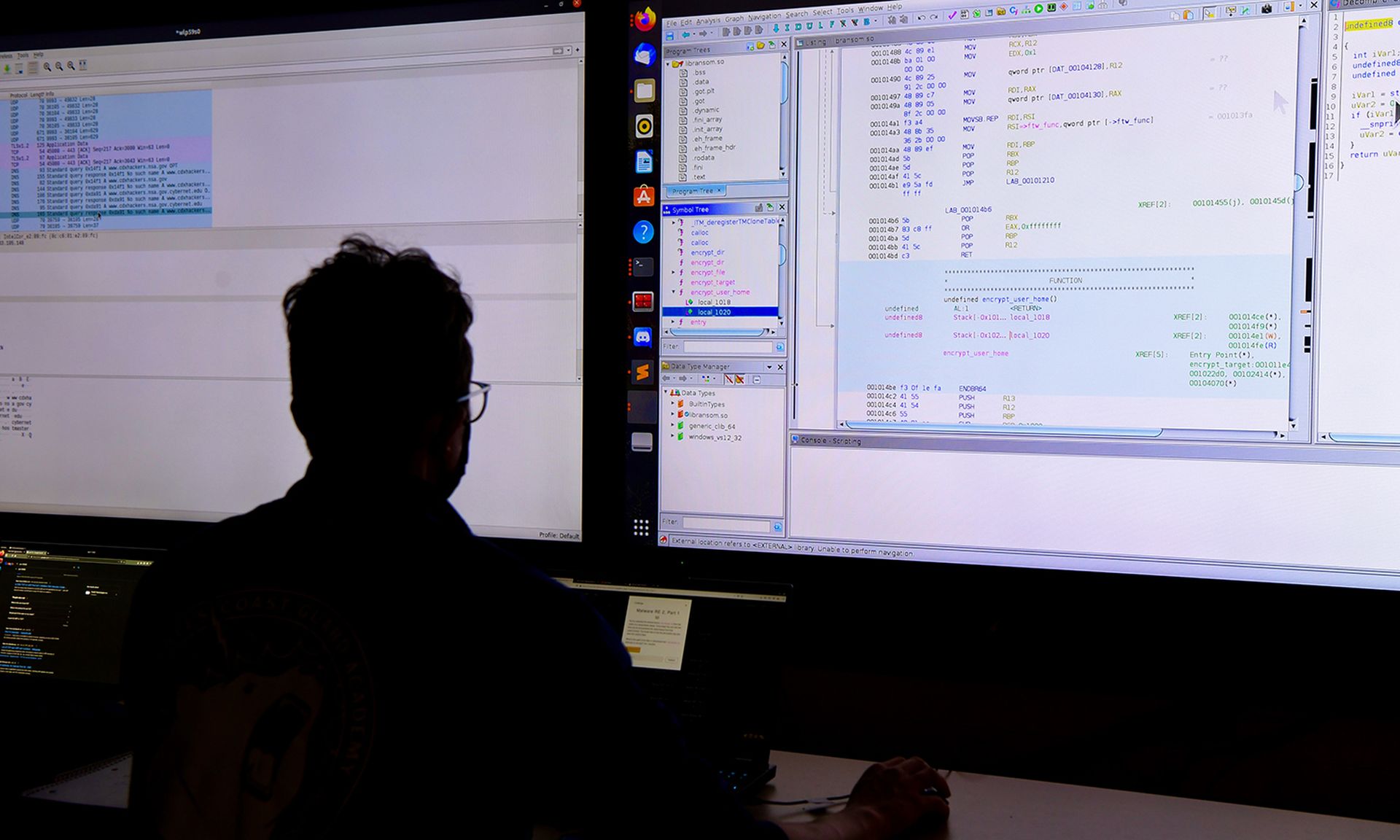
John Hammond, senior security researcher at Huntress, said the BlackBerry research offers a great historical overview on the origins and trajectory of the Chaos ransomware leading up to its sixth revision and new branding name, Yashma. Hammond said the latest crypter includes new features and functions to detect if the ransomware is executed in a forbidden country, can disable antivirus, and stop services for other preventive solutions.
“Seeing the rapid growth of ransomware tooling becoming something so customizable and advanced is a bit bone-chilling,” Hammons said. “Like a software company that adds new features and updates to their product, so does a cybercriminal group — making their product faster, more flexible, and more accessible for their customers...but this time, with ill intent. The notification of a new and improved Chaos ransomware rendition isn't something to sound the alarms and turn the sirens on for, but it’s another wind of warning: the adversaries are just getting stronger. A solid security posture with monitoring, redundancy, and strong detection efforts still remains the best foundation to counteract a threat actor's end-goal of ransomware."
Nicole Hoffman, senior cyber threat intelligence analyst at Digital Shadows, added that in 2019 the Maze ransomware gang changed everything by introducing double-extortion, and now most ransomware attacks result in data breaches. Hoffman pointed out that Chaos ransomware variants can delete files larger than approximately 2 megabytes, resulting in a significantly destructive attack for many organizations.
“It will be unfortunate if destructive ransomware will be a new trend in the industry, with more amateur cyber criminals joining the scene,” Hoffman said. “Either way, security teams should get ahead of the threat by using the 3-2-1 back-up rule, which means three copies of the data, two media types used for the back-ups, and one back-up stored offsite. This rule is not a new recommendation, but it’s more important than ever to combat destructive ransomware attacks.”