Ninety-two percent of 650 financial apps hosted on the Google Play App Store contain extractable data such as application programming interface (API) keys. The findings come from Approov’s Mobile Threat Lab, which reverse-engineered the mobile application code of financial service apps and was able to pry "high-value secrets" from them.
Sensitive API data was obtained under optimum testing conditions and included researchers using a variety of open-source forensic and pen testing tools. Data was obtained via static analysis of apps and also as code was being executed on the mobile devices.
The study, released Thursday, found, of 92% of leaky apps nearly a quarter of those spilled "extremely sensitive" data, such as authentication keys used for payments and monetary account transfers.
"Even if keys and secrets cannot be easily reverse engineered from the mobile app code, hackers can get another opportunity to grab secrets at runtime by manipulating the app, the environment and/or the communication channel(s)," wrote researchers.

Approov's research focused on the "top 200" financial services apps in the United States, United Kingdom, France, and Germany from the Google Play App Store, which consisted a total of 650 discrete applications.
Researchers used open-source tools such as apk_api_key_extractor, gitLeaks, and Trufflehog to find sensitive data and ran Python scripts to analyze, classify and present the data.
Ted Miracco, chief executive officer of Approov, said he was surprised at how easy it was to obtain this information with the right tools. He pointed out that hackers have access to these same open-source tools to attack applications. Miracco said they did the study in response to concerns stemming from high-profile API leak cases, such as the ones with Twitter last summer and T-Mobile in January.
How Secrets Spill
There are two main ways to steal secrets from a mobile app, according to the report.. "The first is static analysis, inspecting the source code and other components of the mobile app package for exposed secrets prior to runtime. The second is during runtime, when the app is compromised at execution, by instrumenting the application, modifying the environment, or intercepting messages from the app to the backend via Man-in-the-Middle (MitM) attacks."
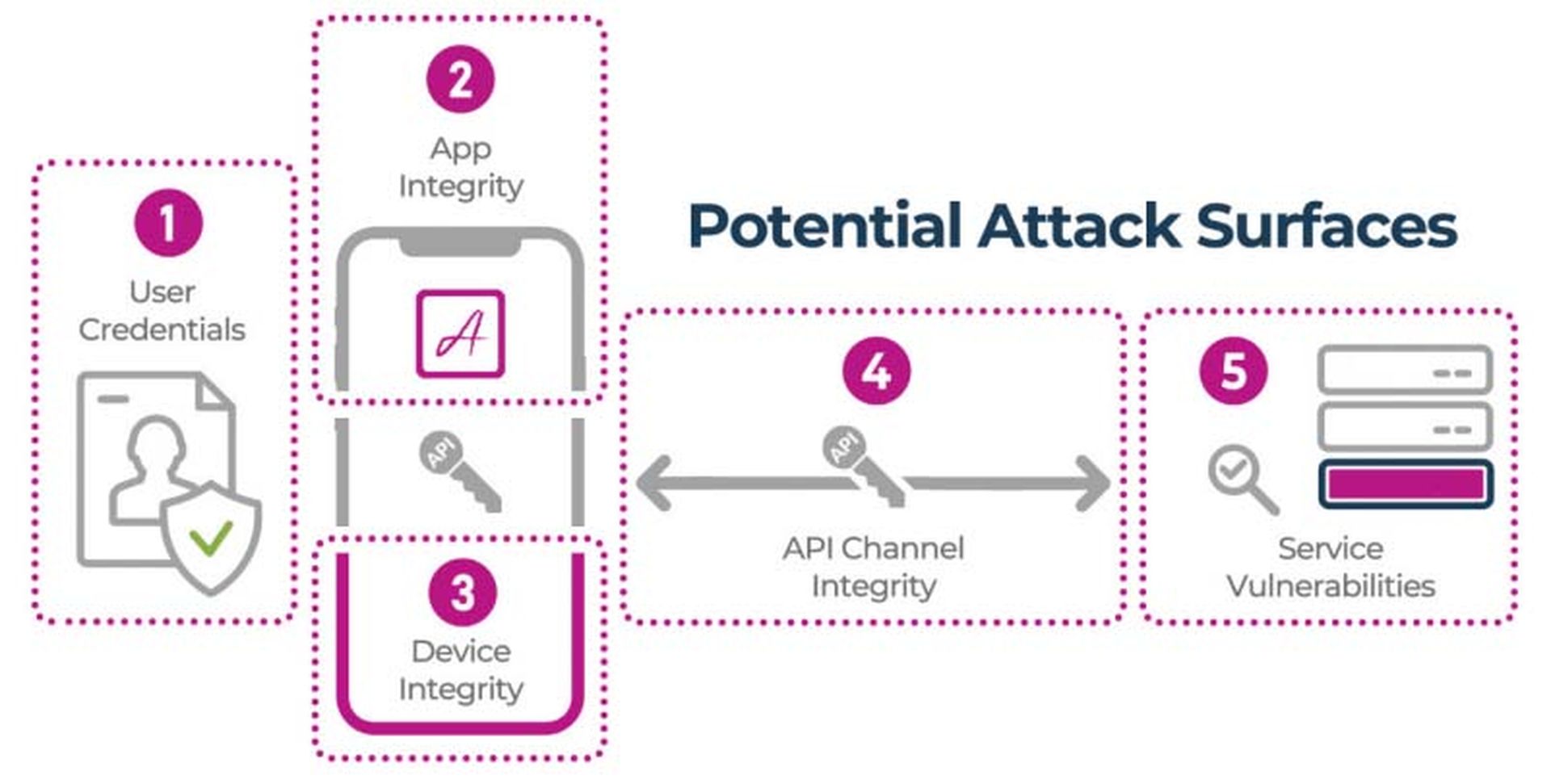
Along with exposing secrets, the scans also found two critical runtime attacks that could potentially be used to steal API keys at runtime. Only 5% of the apps had good defenses against runtime attacks manipulating the device environment, and only 4% were well-protected against man-in-the-middle (MitM) attacks at runtime, where attackers take over communications and in effect get “in the middle” between the two users.
MitM Attack Targets
“Some of reasons MitM has become so prevalent is that multi-factor authentication has become popular, as have encrypted channels such as HTTPS, and MitM allows you to defeat those things,” explained Miracco.
“Man-in-the-Middle [have] been around for years, but there’s more motivation to use it because you have so many mobile apps doing financial transactions and Wi-Fi networks in airports that are unsecured. People have gotten very comfortable, they think with MFA they are safer and they’re not, and they have too much trust in public Wi-Fi networks,” he said.
Miracco pointed to three steps companies can take to manage secrets and API keys more effectively:
- Protect secrets: Don’t put them in code because obfuscation doesn't really work.
- Put runtime protection in place: This will protect against MitM and client environment manipulation which can only be detected and stopped at runtime.
- Manage secrets with a secure cloud service: Deliver secrets "just-in-time" to the app only if the app is deemed safe, and make sure the company can block and change compromised API keys immediately if they are ever compromised, without updating apps.
“The last thing security teams want is to have to roll out a new app,” said Miracco. “It can take months or years before users are using the non-vulnerable version of the app.”
Nick Rago, Field CTO at Salt Security, added that the Approov Threat Lab findings illustrate the critical importance of proper API runtime protection and malicious API behavior detection for an organization's API security strategy. Rago said most mobile apps rely on API-based communication from the application to an application back-end in the cloud or Internet-facing servers. That communication is frequently secured using static, hard-coded, admin-level or privileged API keys and secrets.
“App developers often mistakenly assume that the app user or an adversary could not access these keys,” said Rago. “The Approov report highlights the wide-spread lack of protections app developers put around these credentials and how easy it can be for an adversary to inspect mobile app traffic or app manifests to extract privileged application communication credentials."
Once those keys or credentials find their way into the hands of a bad actor, adversaries can leverage the APIs with admin-like authority. For financial services customers, the impact could be devastating as the attacker could not only gain the power to steal sensitive data associated with customer accounts, but also conduct financial transactions associated with those accounts, he said.
When asked about iOS environments, Miracco said he believed they would find similar results and said it was possible they could run a similar test sometime in the future on iPhone apps.




