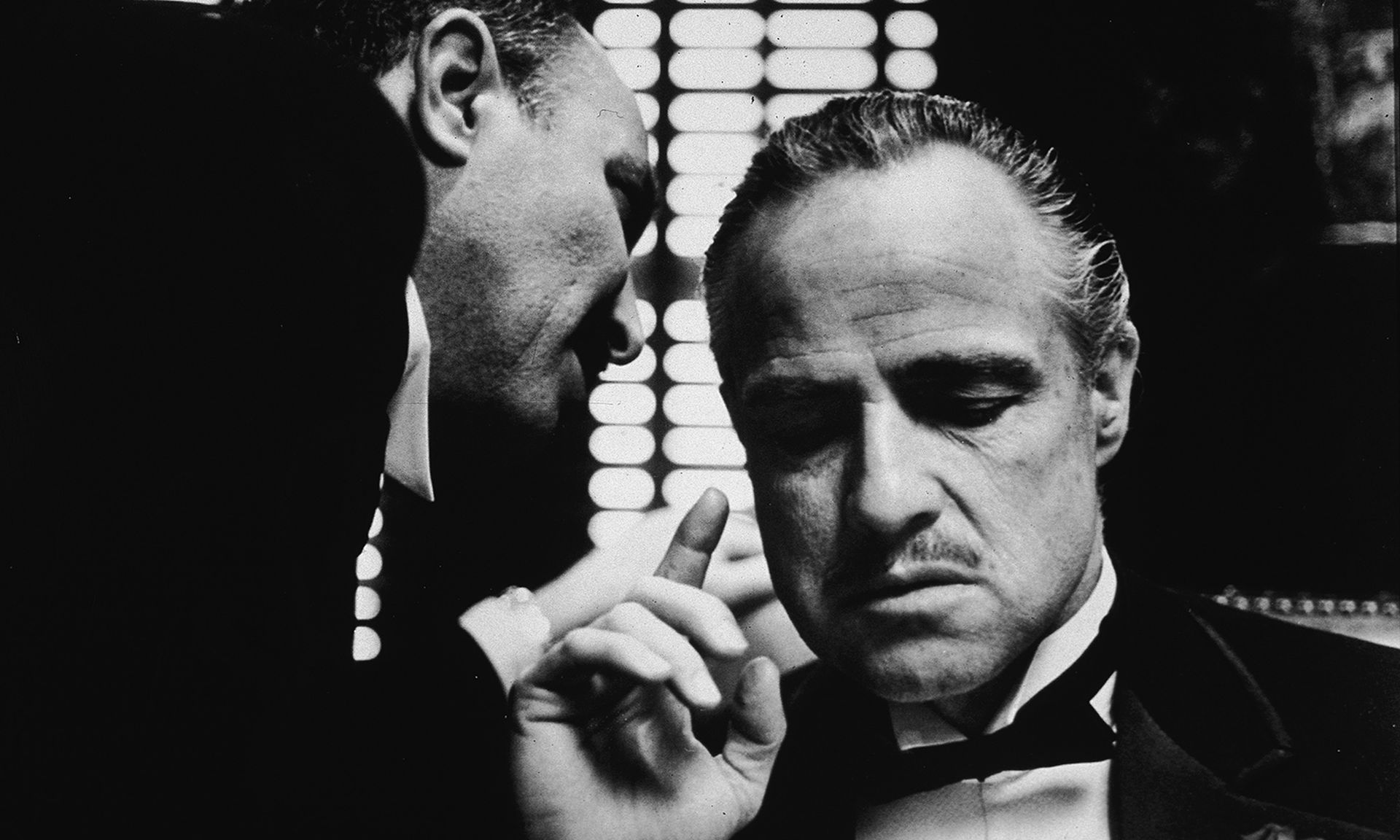
Using imagery and verbiage from the iconic movie starring Marlon Brando, researchers reported that the Android banking trojan Godfather has been using “web fakes” to attack more than 400 targets across 16 countries, including mobile banking applications, cryptocurrency wallets, and crypto exchanges.
In a Dec. 21 blog post, Group-IB researchers explained that Godfather has been designed to let cybercriminals harvest login credentials for mobile banking applications and other financial services — and then drain the accounts. It should be noted that the Group-IB blog does not offer an estimate of the total financial impact.
Group-IB first detected Godfather in June 2021. In March 2022, researchers at Threat Fabric first mentioned the banking trojan publicly. A few months later, the trojan was taken out of circulation. Group-IB researchers believe Godfather was taken out of use so developers could update the malware. Godfather reappeared in September, now with slightly modified WebSocket functionality. Godfather’s predecessor is Anubis, another banking trojan. The researchers said Godfather’s developers used Anubis source code as a basis and modernized it for newer versions of Android.
The researchers say as of October, 215 international banks, 94 cryptocurrency wallets, and 110 crypto exchanges have fallen victim to Godfather. Financial services providers in Canada, France, Germany, UK, the United States, Italy, Poland, Spain, and Turkey, among many others, were targeted.
Of interest to Western countries, the researchers say Godfather spares users in post-Soviet countries. If the potential victim’s system preferences include one of the languages in Eastern Europe, the trojan shuts down. This could potentially suggest that Godfather’s developers are Russian speakers, say the researchers.
Like most other Android-based malware, Godfather is also delivered by a fake application that uses a name and icon similar to a popular app or game, said Venky Raju, Field CTO of ColorTokens. Unsuspecting users download the phony app and get infected, so Raju said users need to be very cautious when downloading applications to their mobile devices.
“On desktop browsers, we have learned to look at the URL closely to ensure it’s not a fake site and we need to exercise the same caution on mobile device app stores,” said Raju. “This is more of an issue on Android devices as Google Play does not exercise tight controls on developer submissions. Even though Google removes malicious applications as soon as they become aware of it, many unsuspecting users get impacted.”
Dangerous malware has made its way onto mobile phones and many developers and app publishers still believe that the app stores from Google and Apple are protected from being infected with malware, said Will LaSala, Field CTO at OneSpan. LaSala said with this new Godfather trojan, it’s important to understand that malware evolves as quickly as the big app stores can take them down, so developers and app publishers should ensure their applications are protected with app shielding, beyond what these stores can offer.
“The trojans of today focus on specific types of attacks, which can be stopped by app shielding being applied to an application before they can cause damage,” LaSala said. “App shielding is a process of hardening the application before it’s published to the app store. It will protect from screen readers, library injection, and even app store repackaging — which is how many trojans are being deployed now. Trust in the big app store providers should be evaluated, and additional technology should be applied to protect users.”



