KELA on Monday released threat intelligence data at the RSA Conference which said in Q1 2022, ransomware gangs continued as a major threat, collaborating with cybercriminals such as initial access brokers (IABs) to conduct attacks on companies worldwide.
Although KELA identified around 700 victims in its sources, showing a decrease of 40% compared with the end of 2021, there was an increase in attacks per month from January 2022 (152) to March 2022 (320). On average, KELA observed 227 ransomware attacks in each month of Q1 2022.
"IAB offers continued to be in demand in Q1 2022 with some of the sold access listings exploited by ransomware gangs for their attacks," said David Carmiel, chief executive officer of KELA. "It's crucial to monitor such activities and stay one step ahead of cybercriminals to prevent a potential ransomware attack."
The KELA survey also pointed out some other important ransomware trends:
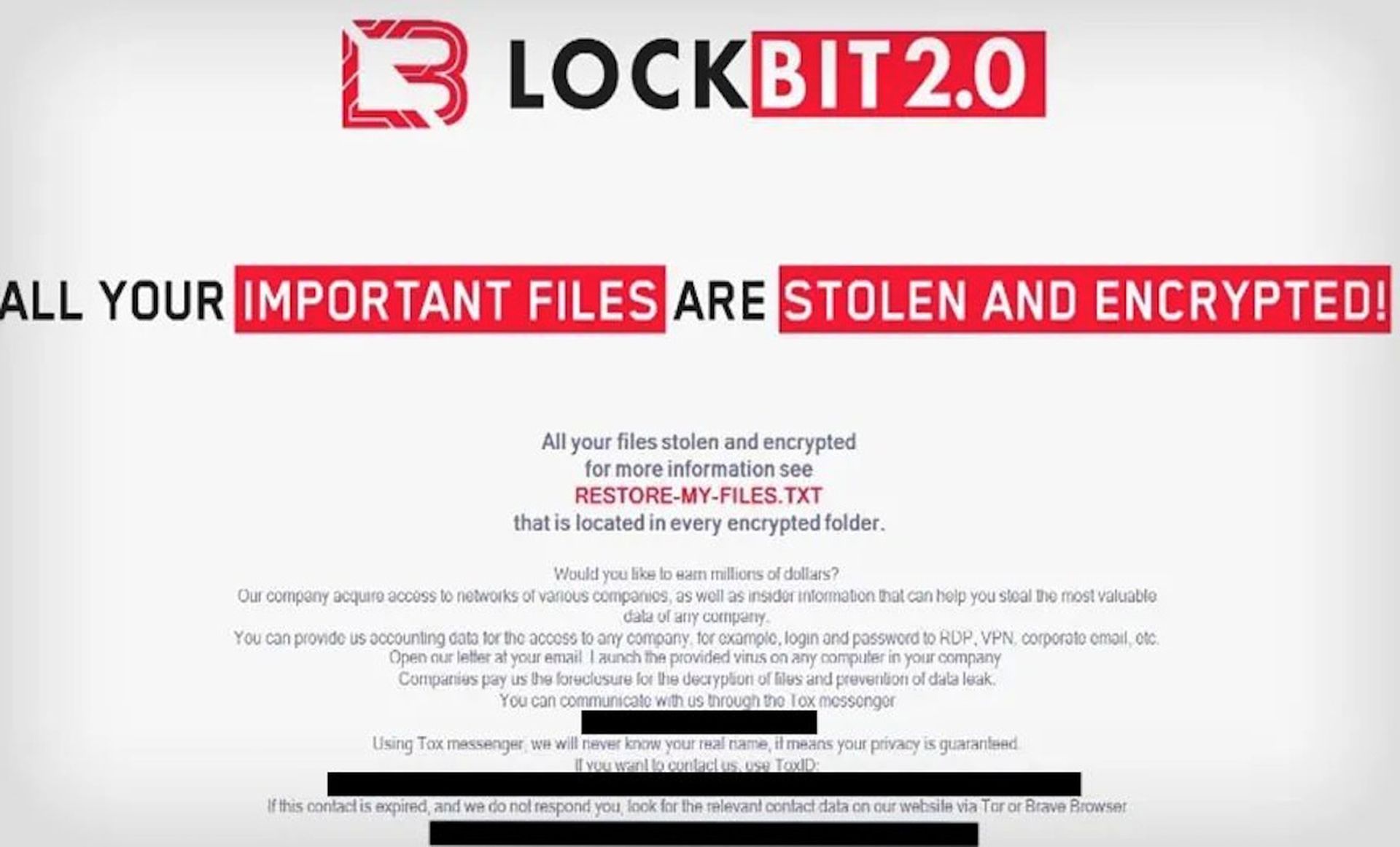
- LockBit replaced Conti as the most active gang since the beginning of the year. The number of attacks launched by the Conti gang fell in January 2022 and increased following a leak of Conti's internal data.
- In Q1 2022, 41 healthcare organizations were compromised by ransomware gangs; 34% of the attacks were associated with the Conti and Karakurt gangs.
- The finance sector made it to the top five targeted sectors, with LockBit carrying out the largest number of attacks against financial companies.
Matthew Warner, co-founder and CTO at Blumira, said ransomware techniques have not necessarily evolved. Rather, Warner said they have expanded over the last five years. Previously, only certain groups would have the capability to perform advanced attacks that leverage zero-days within days of release. Now, Warner said ransomware operators are either buying or identifying their own zero-days or leveraging zero-days as soon as possible within their campaigns.
“It’s extremely important that organizations focus on detecting the first three steps of a ransomware attack: discovery, gaining a foothold, and escalating privileges,” Warner said. “Detection, in addition to being aware as to what data you hold, will allow you to quickly respond to attacks and worst case be sure of post-exploitation handling of a ransomware event.”
Jason Hicks, field CISO at Coalfire, said the KELA report showcases the ecosystem that exists between ransomware threat actors and threat actors that specialize in gaining initial entry, and then reselling that entry to other threat actors.
“It helps to put all of this activity into context,” Hicks said. “These are profit-seeking ventures for the people behind these threat actor groups. If they can purchase access for a good price, they will do so versus taking the time to gain entry on their own. I was surprised to see finance moving into the top five industry’s being attacked. Typically finance spends the most on cyber security (other than defense) and would therefore be a harder target than the other industry verticals in the top five.”