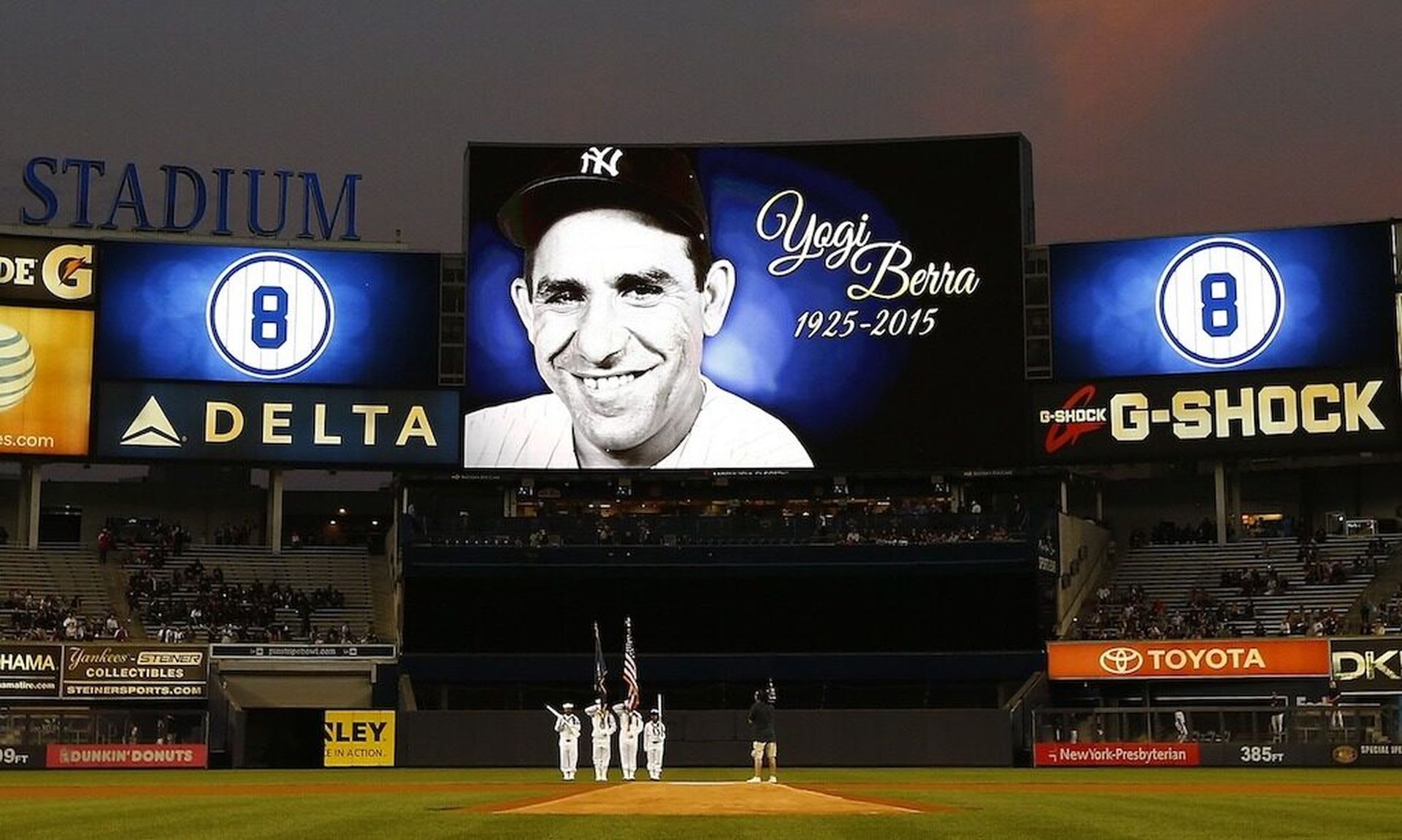
The great Yogi Berra said it best: “It's tough to make predictions, especially about the future.” I agree.
Each December, like clockwork, we are bombarded with security predictions and trends for the new year, and yet, security does not always change dramatically year-over-year. Even in a year as unpredictable as 2021 and the recent Log4j vulnerability, the threats organizations and individuals faced were similar to those in years past, such as phishing and fraud, just with more timely lures attached.
Despite “new” predictions coming out each year, we still face the same long-standing problems. So, for this year, rather than making 2022 predictions, I want to highlight three fundamental problems our industry needs to resolve to make a meaningful impact on the security risk landscape: the workforce gap, vulnerability management, and the need for technology providers to build more secure technology. Only after acing the fundamentals will organizations have a fighting chance against more advanced and evolving threats.
- Workforce gap.
Cybersecurity operates as an asymmetric environment in which hackers have nearly unlimited potential to cause harm to organizations, and defenders have to get it right every time. Regardless of industry, any environment like this would clearly require an amazing defensive team. However, most organizations struggle to staff a defense because there’s not enough adequate cyber talent.
Talent may be the biggest issue facing our industry. Having the right talent in place is foundational to what we do, but we are seeing a workforce gap with 2.72 million unfilled jobs. Investing in training programs and developing employees in transferable skills are important to attracting and retaining the talent necessary to keep organizations secure, in parallel to efforts to make our industry less dependent on labor, such as through automated cyber defense innovation and efforts to reduce overall vulnerability.
Organizations working to fill their security hiring needs may consider transitioning interested employees from non-traditional security backgrounds like risk, IT, data analytics or engineering roles into security positions. These individuals can build upon the foundation of their existing roles with focused security training. More broadly, nations and educational institutions should invest in cybersecurity as a long-term strategic priority, as it’s essential to the safety and stability of our digitally-dependent future.
- Vulnerability management.
Too many organizations also have a difficult time effectively managing their vulnerabilities. This begins with organizations having awareness of what technology they have deployed and are dependent upon to function - often via an asset inventory system - and then finding and fixing misconfigurations and other security vulnerabilities in those systems in a timely manner. While IT governance processes such as asset inventory and patch management are simple in concept, we as an industry tend to struggle with these basics -- and hackers to continue capitalize.
The discussion around asset inventory must extend beyond IT managed systems to anything plugged into corporate networks, as well as third-party cloud services that organizations depend upon. Further, the discussion around patching should focus on patch speed and prioritization. This has become crucial because it commonly takes weeks, if not months, for organizations to patch vulnerabilities, yet hackers commonly exploit vulnerabilities within hours or days of their publication. It’s imperative to know what technology the company has at all times in near-real time, and to find and patch vulnerabilities within hours. While this level of excellence exceeds industry standards, organizations need to practice this effectively to defend against today’s threats.
- Secure technology.
At the heart of many vulnerabilities are technology systems that were not designed with security in mind. They often use inadequate design and development practices. This issue only gets worse as the number of companies developing technology explodes with the digitization of “smart” product lines across every sector – from appliance companies to watch makers, everyone develops code today.
Technology providers must become far more proficient at developing technology that’s intrinsically more secure and resilient, designed with the foresight on how these devices will connect into networks that are likely crawling with hackers. An intrinsic security approach results in technology that’s less likely to have security bugs, but also that fails with fewer consequences when vulnerabilities are inevitably discovered. Additionally, by deploying intrinsically more secure technologies, this reduces the need for the dozens upon dozens of security tools that most organizations are forced to run, which in turn reduces the skilled cyber labor needed to operate these tools. This illustrates the harmony and interplay that exists between these three fundamental security areas, where only by implementing each in concert will we realize the full potential of this opportunity.
Please don’t get me wrong, I am not saying future-looking security predictions are not useful. I just believe we should spend our time solving the long-standing problems that hurt us every day, rather than pontificate about problems that don’t yet exist. With a renewed focus on getting the fundamentals right, organizations can begin to close the asymmetry that exists in this challenging field.
John Scimone, senior vice president, chief security officer, Dell Technologies